- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Wildfire Email Link Analysis
- LIVEcommunity
- Discussions
- General Topics
- Wildfire Email Link Analysis
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Wildfire Email Link Analysis
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2014 04:21 AM
Hello,
I have a question regarding this new functionnality for PANOS 6.1.0 version.
One of my customer has tested, but he doesn't get an email when a suspicious link in an email is send/received by users.
So I tested on our lab, and I have the same behavior. I use the informations from WildFire Email Alerts: Subscribe or Add Additional Recipients
It seems to detect threat links as informational/low severity for smtp:
Even if the link I used for my test in the email, is known as malware by Wildfire:
And it's blocked when I use this link on my browser:
So, did anyone has successfully applied this functionality and received an email alert?
And which link do you use to test it? ![]()
Regards,
Renan
- Labels:
-
Configuration
-
Content-ID
-
Troubleshooting
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2014 04:35 AM
Hello Renan,
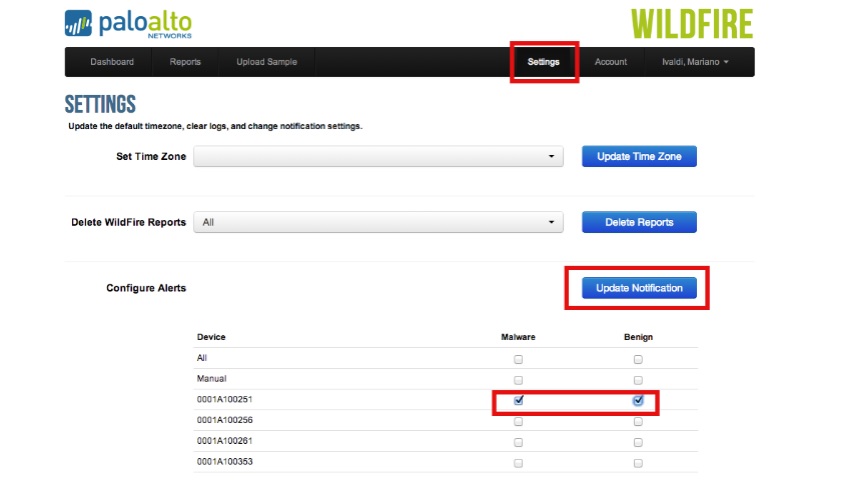
Did you verify your wildfire portal that, above mentioned serial number is "checked" for notification.
- Login with your credentials at: https://wildfire.paloaltonetworks.com/
- Go to Settings > Configure Alerts and search for the firewall serial numbers desired to subscribe to for alerts, and whether the user wises to receive an alert for verdicts resulting as malware or benign.
- Once the appropriate check boxes are selected, click on 'Update Notification' to apply changes
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2014 06:28 AM
Hello Hulk,
I have check and enable notifications from WF portal, and it works.
But from my understanding, when a suspicious link is present in an email, the device is supposed to send an alert message through smtp, right?
Regards,
Renan
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2014 06:34 AM
Hello Renan,
That is a different option to send SYSTEM log messages (for different severity) to an email account.
Reference DOC: How to Configure Email Alerts for System Logs?
Hope this helps.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2014 06:53 AM
Hello Renan,
Do you see the wildfire log show as benign or Malware?
Once firewall get the verdict then firewall will send an email alert.
Regards,
Hari Yadavalli
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2014 06:56 AM
Hello Renan,
Wildfire email link analysis is no different compared to other file types you have in file blocking profile.
If any email contains a http or https link then firewall will forward that link to wildfire and gets an analysis report.
If the link in email is benign or malware then firewall will send an email report.
Regards,
Hari Yadavalli
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2014 07:21 AM
Hello Hari,
Yes, I do not see the Wildfire submission in the WF logs, neither in the portal for this activity.
Other WF threats are correctly send.
Maybe a missconfiguration?
I have just followed the KB: WildFire Email Alerts: Subscribe or Add Additional Recipients
@Hulk: I have tried, but not receiving email.
Regards,
Renan
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2014 07:43 AM
Hi Renan,
Hari is right, firewall is supposed to get logs. After that it forwards it to Email.
Now first thing is why firewall is not generating wildfire logs. Did you configure file blocking profile with "forward" or "Continue-forward".
Regards,
Hardik Shah
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2014 08:03 AM
Hello Renan,
You may need to check your firewall configuration once more. ![]()
- Need to check the wildfire action, data-filtering profile, security rule where it should be apply.
A KB document for your reference: How to Configure WildFire
FYI: WildFire CLI commands
Once the basic configuration is complete, the following commands provide the details of the best server selected. To test the Connectivity, follow the steps below:
> test wildfire registration
This test may take a few minutes to finish. Do you want to continue? (y or n)
Test wildfire
wildfire registration: successful
download server list: successful
select the best server: va-s1.wildfire.paloaltonetworks.com
Initial registration can only be done on the active unit in an Active/Passive cluster.
Note: Do not use PING to test connectivity to the server. Ping requests are disabled on the WildFire server. Best practice to test connectivity is to Telnet to the server on port 443.
To verify, if any files have been forwarded to the server, use the following command:
> show wildfire status
Connection info:
Wildfire cloud: default cloud
Status: Idle
Best server: va-s1.wildfire.paloaltonetworks.com
Device registered: yes
Service route IP address: 10.30.24.52
Signature verification: enable
Server selection: enable
Through a proxy: no
Forwarding info:
file size limit (MB): 2
file idle time out (second): 90
total file forwarded: 0
forwarding rate (per minute): 0
concurrent files: 0
The total file forwarded counter will provide the number of files being forwarded to the server.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2014 09:11 AM
Hello Renan,
Share the output of below command:
>show wildfire statistics
Regards,
Hari Yadavalli
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2014 09:15 AM
Hello Renan,
And also another point to note if we already have the signature in our Virus database firewall won't even forward to wildfire.
Regards,
Hari Yadavalli
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2014 09:29 AM
Hello
my configuration is fine, other suspect files are send to WF, and on this specific function in the screnshot, you can see that "wildfire-upload-success" is the action.
For other questions:
> show wildfire status
Connection info:
Wildfire cloud: public cloud
Status: Idle
Best server: eu-s1.wildfire.paloaltonetworks.com
Device registered: yes
Valid wildfire license: yes
Service route IP address: 62.23.197.100
Signature verification: enable
Server selection: enable
Through a proxy: no
File size limit info:
pe 2 MB
apk 10 MB
pdf 400 KB
ms-office 500 KB
jar 1 MB
flash 5 MB
Forwarding info:
file idle time out (second): 90
total file forwarded: 647
file forwarded in last minute: 0
concurrent files: 0
> show wildfire statistics
Packet based counters:
Total msg rcvd: 269318
Total bytes rcvd: 224453980
Total msg read: 241801
Total bytes read: 197836829
Total msg lost by read: 27517
Total DROP_NO_MATCH_FILE 27517
Total files received from DP: 2155
Counters for file cancellation:
CANCEL_BY_DP 31
CANCEL_TIME_OUT 4
CANCEL_FILE_DUP_EARLY 32
CANCEL_FILE_DUP 647
CANCEL_FILESIZE_LIMIT 93
CANCEL_CONCURRENT_LIMIT 15
Counters for file forwarding:
file type: apk
FWD_CNT_LOCAL_FILE 1
FWD_CNT_REMOTE_DUP_CLEAN 1
file type: pdf
FWD_CNT_LOCAL_FILE 64
FWD_CNT_LOCAL_DUP 12
FWD_CNT_REMOTE_FILE 55
FWD_CNT_REMOTE_DUP_CLEAN 13
FWD_CNT_REMOTE_DUP_TBD 3
file type: email-link
FWD_CNT_LOCAL_FILE 48
FWD_CNT_APPENDED_BATCH 49
file type: ms-office
FWD_CNT_LOCAL_FILE 28
FWD_CNT_LOCAL_DUP 22
FWD_CNT_REMOTE_FILE 27
FWD_CNT_REMOTE_DUP_CLEAN 9
FWD_CNT_REMOTE_DUP_TBD 10
file type: pe
FWD_CNT_LOCAL_FILE 46
FWD_CNT_LOCAL_DUP 15
FWD_CNT_LOCAL_FILE_CLEAN 25
FWD_CNT_REMOTE_FILE 3
FWD_CNT_REMOTE_DUP_CLEAN 55
FWD_CNT_CACHE_SYNC 1
file type: flash
FWD_CNT_LOCAL_FILE 1120
FWD_CNT_LOCAL_DUP 598
FWD_CNT_REMOTE_FILE 519
FWD_CNT_REMOTE_DUP_CLEAN 907
FWD_CNT_REMOTE_DUP_TBD 39
FWD_CNT_REMOTE_DUP_MAL 9
FWD_CNT_CACHE_SYNC 4
file type: jar
file type: unknown
file type: pdns
Error counters:
FWD_ERR_CONN_FAIL 4
LOG_ERR_REPORT_CACHE_NOMATCH 198237
Reset counters:
DP receiver reset cnt: 1
File cache reset cnt: 1
Service connection reset cnt: 1
Log cache reset cnt: 1
Report cache reset cnt: 1
Resource meters:
data_buf_meter 0%
msg_buf_meter 0%
ctrl_msg_buf_meter 0%
File forwarding queues:
priority: 1, size: 0
priority: 2, size: 0
priority: 3, size: 0
@Hardik: The file blocking profile is set to "forward"
@Hari:that's an interesting point, so this is relevant only to unknown applications not seen by WildFire?
Because what I have understood, and also my customer, is for every suspect application, we will get an email alert from device with this.
Regards,
Renan
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2014 09:44 AM
Hi Renan,
By defualt benign files are not logged. You have to enable it by following command. May be files are benign and not malicious.
> configure
# set deviceconfig setting wildfire report-benign-file yes
# commit
Regards,
Hardik Shah
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2014 10:01 AM
Hello Renan,
My apologies, I stand corrected.
For any http or https links in an email body firewall does not check virus database because firewall cannot hash links and so it has to send any links to wildfire and should get a report.
Once the firewall receives a report then you will receive wildfire report via email.
Regards,
Hari Yadavalli
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2014 01:34 PM
Hello Renan
Could you please run the below command and check for the "Wildfire logs written"
> debug log-receiver statistics
Now try to download an exe file . You can use the link " http://wildfire.paloaltonetworks.com/publicapi/test/pe"
Check if the counter increases. This will let us know if the counter will indicate if the wildfire logs are written.
Restart var-data receiver, management server and device server one at a time to see if it fixes the issue
> debug software restart vardata-receiver
>debug software restart management-server
> debug software restart device-server
If this does not resolve the issue please turn ON the debug for the the following daemon
> debug vardata-receiver on debug
> debug device-server on debug
>debug log-receiver on debug
Run the test again and turn off the above debugs. Then download a tech support file and contact TAC for further assistance.
Regards
Khan
- 9966 Views
- 15 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Wildfire False Positive on Detection of .XLSX extension in General Topics
- Palo Alto for email security in Next-Generation Firewall Discussions
- Local Analysis Malware and WildFire Malware Alerts in Cortex XDR Discussions
- Newsletter: Cloud Delivered Security Services, Oct-2025 in Advanced Threat Prevention Discussions
- Can Cortex XDR fully substitute for Microsoft Defender Attack Surface Reduction (ASR) rules? in Cortex XDR Discussions




