- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Wildfire reports association to wildfire-virus
- LIVEcommunity
- Discussions
- General Topics
- Re: Wildfire reports association to wildfire-virus
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Wildfire reports association to wildfire-virus
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-23-2016 05:55 AM
For every wildfire-virus signature tripped in Threat logs should I expect to recieve a corresponding wildfire report in the Wildfire Submissions too?
Could someone answer or point me to documentation please.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-23-2016 08:11 AM - edited 02-23-2016 08:19 AM
@lewis in the threat log if you're seeing "wildfire-virus" as a type, I don't think you're gonna see a submission report. That log type just means, as I understand it, that somewhere in the "WildFire network" the communications stream/file was seen and was determined to be malicious. So that signature was added at somepoint to the threat subscription you have.
So it wasn't necessarily a WildFire submission in your environment which created the original signiture and as such you wouldn't see a report.
https://www.paloaltonetworks.com/content/dam/pan/en_US/assets/pdf/framemaker/70/pan-os/pan-os.pdf
P. 29
"WildFire—Provides near real-time malware and antivirus signatures created as a result of the analysis done by the WildFire cloud service. Without the subscription, you must wait 24 to 48 hours for the signatures to roll into the Applications and Threat update"
--EDIT--
Under the "Threat Logs" this describes the log
P.321
"wildfire—A WildFire verdict generated when the firewall submits a file to WildFire per a WildFire Analysis profile and a verdict (malicious, grayware, or benign, depending on what you are logging) is logged in the WildFire Submissions log.
wildfire-virus—Virus detected via an Antivirus profile."
So yeah one will have the report, one won't.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-23-2016 10:06 AM
thanks Brandon_Wertz.
I guess what is confusing for me is when we have wf submissions and a wildfire-virus signature is available we typically see a 1:1 corrilation. But earlier today I noticed we had about 200 wildfire-virus signatures tripped in the threat logs but no wf submissions related to these.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-23-2016 12:16 PM
Hi Lewis and Brandon,
Brandon is correct. Let me clarify it a bit more: wildfire-virus in threat logs means that threat was identified with a signature that is coming from your Wildfire updates. This signature was created based on a submission to the cloud of the file where it received verdict "malicious", that triggered two actions: sending back report to the device that submitted it, and creating a signature to be distributed to all those who enjoy benefits of the Wildfire subscription. File could have been uploaded by anyone, you will get Wildfire report only if you were submitter.
Regular "virus" as a sub-type means definition was found in AV updates, "wildfire-virus" means definition is found in Wildfire updates. Those databases are not the same, Wildfire subscribers should get signature in less than an hour, usually under half an hour or even sooner from the private cloud (WF-500, appliance with local sandboxing).
If you check your Wildfire Submissions log, and file isn't there, than you didn't submit it, someone else did. If you have Autofocus subscription, you can use sha256 of that file (or some other details to search by) and still learn plenty of details that would otherwise be available only in Wildfire Report and for original submitter. Those are anonymised from the submitter perspective, you will not have insight into attacked party, just into attacker's information, but that is all what matters anyhow.
Some intelligence comes from thirt party or their submitters chose not to share details of reports, so not all files can be checked in Autofocus but plenty can be found and more details on the particular threat learned. This is very handy for those that need extended information on threat landscape, IMHO.
Hope this sheds some more light onto your question and that I still helped a bit 🙂
Best regards
Luciano
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-26-2016 05:30 AM
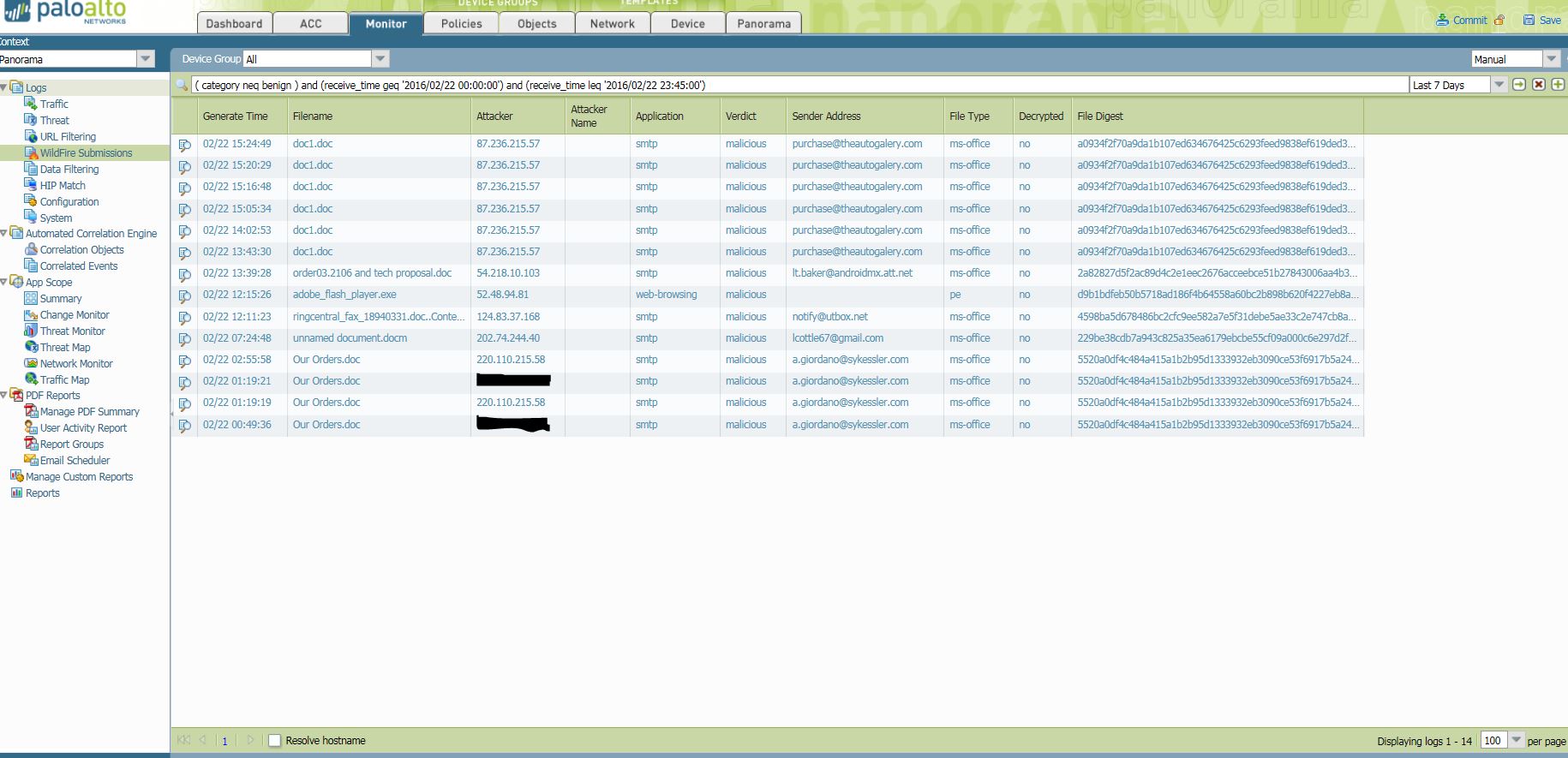
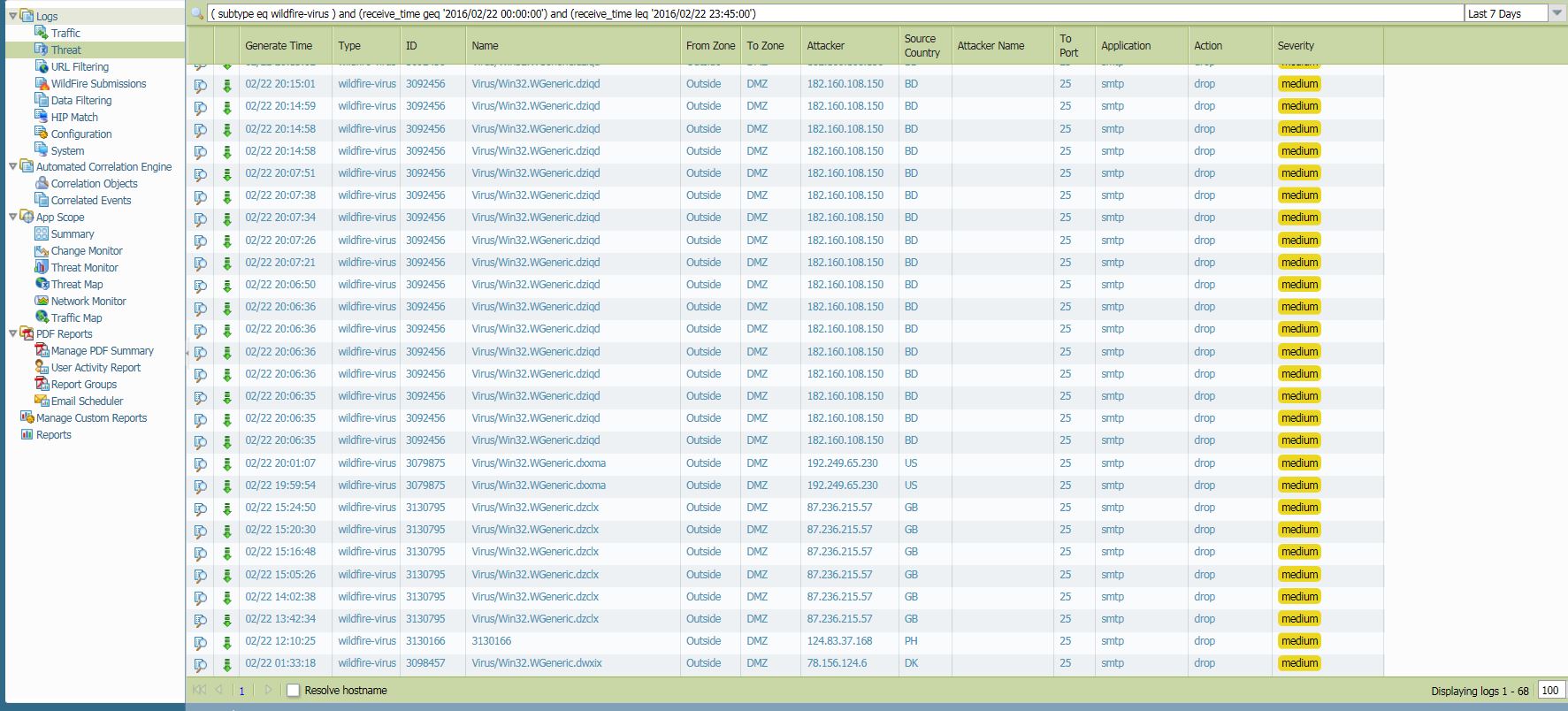
Thanks Lucky. I understand what you are saying but I guess I am just seeing a bunch of inconsistencies. What I am observing is related to malicious smtp traffic. In my screenshots below you will see IP 87.236.215.57 in the wf submission log and a corresponding wf-virus signature in the threat log as there happens to be wf-virus sig in this case. Which has been what we have grown to expect since using wf. Also in the screenshots you will see IP 182.160.108.150 in the threat log tripping wf-virus signatures but no wf-submissions. I am fine with no wf report if a wf-virus is tripped but just the inconsistency is what has me puzzled.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-26-2016 09:48 AM - edited 02-26-2016 09:53 AM
Hi Lewis,
Malware IDs are different, so those are two different attacks in my opinion. For first one (ID 3130795) you generated signatures yourself (doc1.doc files that were arriving between 13.32 and 15.24), second (ID 3079875) and third round (ID 3092456) came later.
I don't see discrepancy in your threat logs as I can see good timeline for 3130795 that corresponds with Wildfire uploads of doc1.doc; subsequent attacks in your threat logs were prevented by signature 3092456 that was generated by upload from some firewall other than this one; therefore no logs and/or reports are available in WF submissions. That is why you are using WF subscription, even if someone else uploads malware you will get signature back as soon as they do.
Only thing that is not looking as usual is that you kept uploading same file between 13.43 and 15.24; USUALLY you would get WF signatures within one hour if your download-and-install interval is set to 15 minutes. Considering that you had larger window of previous malware (again uploading between 00.49 and 2.55) I would just make sure Wildfire signatures are on 15 minutes schedule, it looks more if you have it set in one-hour intervals.
Best regards,
Luciano
- 5723 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Is the unified RPC interface (MonitorDirect.enqueueLogRequest) supported for external use? in Next-Generation Firewall Discussions
- PA 445 setup in Next-Generation Firewall Discussions
- Reset admin cli password of wildfire appliance 500 in General Topics
- Wildfire False Positive on Detection of .XLSX extension in General Topics
- Cortex XDR Tenant Auto-Upgrade 3.17 → 5.0: UI mixed theme, AI pages stuck loading, Marketplace/Playbook Catalog empty + ingestion quota warning in Cortex XDR Discussions