- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Wrong user from access log
- LIVEcommunity
- Discussions
- General Topics
- Re: Wrong user from access log
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Wrong user from access log
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-07-2018 02:50 AM
Hello!
The local user Administrator is logged in on the desktop and he is not allowed to access the internet. But he can access.
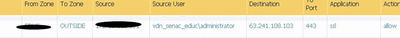
When checking in Monitor on PA220, I noticed that another user appears in the Source User column and not the Administrator user.
Has anyone ever experienced this?
Software version 8.0.10
Thank you!
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-07-2018 03:08 AM
Ok... but, do you know how we can solve this issue?
Thank you!
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-07-2018 03:16 AM
ooh... good point... not sure... I'm sure someone will jump in and advise..
to confirm..
are you using AD for user-ID.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-07-2018 03:17 AM
Yes... I am using AD server.
So, let´s wait...
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-07-2018 03:26 AM - edited 11-07-2018 03:27 AM
Have you tried this approach...
•Device > User Identification> User Mapping > Palo Alto Networks User-ID Agent Setup > Client Probing
You can configure the User-ID agent to perform WMI client probing for each client system that the user mapping process identifies. The User-ID agent will periodically probe each learned IP address to verify that the same user is still logged in. When the firewall encounters an IP address for which it has no user mapping, it sends the address to the User-ID agent for an immediate probe. To configure client probing settings, complete the following fields.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-07-2018 03:37 AM
This option is enabled...
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-07-2018 01:52 PM
You'll never get local admin accounts to actually show up as a user-id, unless you poll the machine in question which would be a really odd configuration. WMI client probing can help in this case, but your user-id configuration will ignore the user unless specifically set to allow it.
Best solution, admin accounts should be AD users that are granted administrative rights on the machine. If you are going to use local-user accounts for administrative purposes you'll have to grant at least basic tcp/80 and tcp/443 access for any unknown-user in your environement and just be sure to log it to fit in with your security needs.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-08-2018 05:02 AM
Hello Bpry,
we do not want local users to have access to the internet. The local administrator was able to access the internet by chance and we were surprised when we checked the PA220 log.
I think the problem is when the PA220 looks in the Domain Controller Audit log for the validation of the user who is logged into the machine. Because the local machine administrator is not registered in the Domain Controller Audit log, it takes the last user record that logged on the machine.
Thank you!
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-08-2018 06:16 AM
Correct; which is why WMI probing isn't going to help you here, as the firewall sees the old user-mapping and has no reason to immedately trigger a probe. You could potentially get around this by decreasing your timeout value, which still wouldn't eleviate the issue but would probably fit what you are aiming to do better than what you have already.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-09-2018 09:11 AM
Hello @BPry,
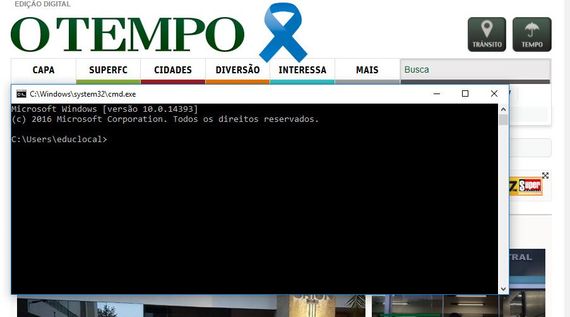
I logged with user "educlocal" (he doesn't has internet access and he is a local user in Windows 10.).
But he is accessing internet.
Here is the log showing the user showing by PA when local user "educlocal" access the internet.
this is one of my issue.
Thank you!
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-09-2018 09:22 AM
Just because a new user logs in doesn't mean the user-id information on the firewall will automatically clear, the firewall has 0 knowledge of this event if you're just reading AD logs. Depending on a number of different configuration options ( WMI Probing Interval, User Identification Timeout Value) the mapping will stay present until it is removed or updated.
So if I'm logged into a machine with 'DOMAIN\bpry' as my user-id and then log in with a local admin account, the firewall doesn't have any idea that this local-account was ever used. To account for this either the probe interval can be increased if using WMI, or the identication timeout value can be decreased. Each option has downsides:
WMI Probing:
- Some find it difficult to setup
- Setting a short WMI Probe interval will cause a large amount of network traffic to all devices.
User Identifcation Timeout:
- Depending on the source of the user-id logs a short timeout value isn't possible if you wish to maintain user-id mappings.
- Setting an artifically high value can also cause issues.
When you're using local accounts there isn't a good way to solve the issue that you are running into. You simply aren't providing the firewall with the required information to update the user-id mapping. This means that regardless of what you do, there is the possibility that for a certain period of time the old user-id mapping will stay active when you log in with a local account.
To properly fix this you need to get rid of local accounts; there isn't another way to get around this issue.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-09-2018 09:26 AM
could you not run a script on local group policy that mapped a network drive to an AD share with username
vdn_senac_educ\restricted.user
this would then update User-ID to a user that would be denied internet access...
a bit heath robinson but workable...
I favour the banning of local user accounts...
- 6473 Views
- 20 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Block privileged accounts from accessing the Internet in Next-Generation Firewall Discussions
- Problem with viewing and downloading 30-day logs on Panorama server in Panorama Discussions
- Community Edition in Cortex XSOAR Discussions
- Need clarification on URL Filtering logs in Next-Generation Firewall Discussions
- After Endpoint Traffic Policy Enforcement, client can not be access microsoft login portal for smal auth. in GlobalProtect Discussions