- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
GlobalProtect - Block internet access if user does not authenticate
- LIVEcommunity
- Discussions
- Network Security
- GlobalProtect Discussions
- GlobalProtect - Block internet access if user does not authenticate
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-22-2021 01:56 PM
Is it possible to block internet access if user does not authenticate through the GP client? We don't want any access to the web on the laptop unless they fully authenticate through Okta/GP (SAML). Would Pre-logon solve this?
Thanks
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-23-2021 06:19 AM
Sounds like you're just looking for the "Enforce GlobalProtect Connection for Network Access" feature in your agent.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-23-2021 05:40 AM - edited 03-23-2021 05:42 AM
Hi PPerrotta,
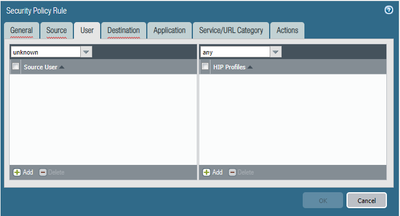
You can setup a policy denying unknown users in the security policy with the action of block:
Using Global Protect your user identification should work just fine so no need to worry about users not being identified when connecting to the vpn.
Make sure your source zone and source addresses are from the VPN otherwise you might block traffic like printers etc unless you use the api to identify those devices.
++ Edit
You might have to allow your users to go to your okta tenant <domain>.okta.com above the deny policy to allow them to authenticate if you are using internal gateways as well
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-23-2021 06:14 AM
Thanks for the feedback.. but that is all post-authentication. We are in a locked-down environment so we cant use SSO or Always on, maybe pre-logon is an option. What we want is if a user doesn't authenticate on the VPN they shouldn't be able to browse the web. Users now just skip the authentication and use it for personal browsing then connect when they need access to the corporate network. So ultimately we want to stop that behavior.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-23-2021 06:19 AM
Sounds like you're just looking for the "Enforce GlobalProtect Connection for Network Access" feature in your agent.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-23-2021 06:21 AM
BPry is correct, you can configure this in the Portal settings under the Agent Configurations.
- 1 accepted solution
- 11352 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Global Protect is having issues with newer MACOS version. in Next-Generation Firewall Discussions
- Global Protect Internal Detection in GlobalProtect Discussions
- GlobalProtect 6.1.11-175 Connection Issues in GlobalProtect Discussions
- New cert GP cert prompt for people testing Yubikeys for windows logon in GlobalProtect Discussions
- User ID mapping works on DC but not/intermittent on branches for Intune internal users. in GlobalProtect Discussions