- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
VPN access can be made without credentials After GP 5.2.9 version update
- LIVEcommunity
- Discussions
- Network Security
- GlobalProtect Discussions
- VPN access can be made without credentials After GP 5.2.9 version update
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-05-2022 11:54 PM
Connection problem without credentials in version 5.2.9
We switched from GP 5.2.4 version to 5.2.9 version with transparent update. Windows users report that they can connect directly without entering a password when making vpn connections.
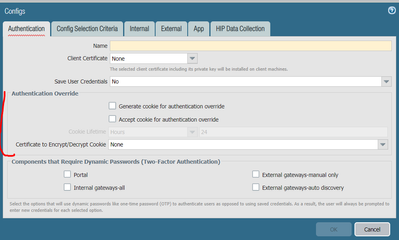
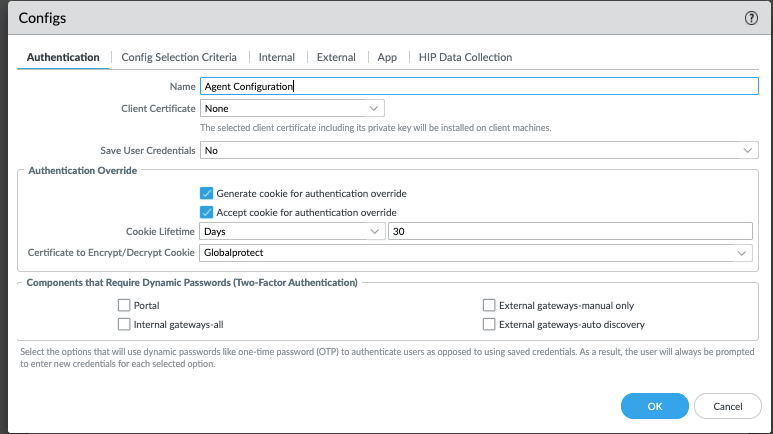
In the global protect > portal > agent configuration, save user credentials section is selected as no.
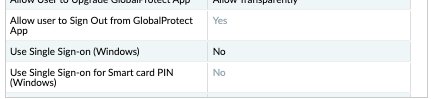
In the Globalprotect >portal > agent> app configuration, the option to save Windows SSO information is selected as no.
However, windows users using version 5.2.9 can connect directly without entering a username and password.
Anyone have this problem or have a solution ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-06-2022 12:55 AM - edited 01-06-2022 12:59 AM
Hi Blilal,
Ive tested this on 5.2.9 and do not see the same problem.
Kindly can you confirm if you have authentication override setup?
Network> Portal/Gateway > Agent > Relevant Agent Config > Authentication > Authentication Override:
If you have this setup it could be that the agent has a cookie and is using the cookie to authenticate.
If you do not have this on the portal and gateway I would recommend opening a case with PANW to investigate.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-06-2022 01:59 AM
Hi,
yes, I override authentication.
The strange thing is that this problem is fixed in authentication, only when I register with the username.
At the same time, when I uninstall the global protect application and reinstall it, it is temporarily fixed and after a while it happens again.
All windows machines that have this problem are in the company domain. I guess somehow it uses global protect by taking the credentials on windows machines from the cache.
I created a case for this situation. I haven't received an answer yet
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-06-2022 07:18 AM
Do you see SSO login in the agent logs?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-06-2022 01:22 PM - edited 01-06-2022 01:25 PM
From the system logs, are the users authenticating against the portal or the gateway when reconnecting (or both)? And also what method was the authentication?
Monitor -> Logs -> System -> filter: ( eventid eq globalprotectportal-auth-succ ) or ( eventid eq globalprotectgateway-auth-succ )
"GlobalProtect portal user authentication... Auth type: ????"
Also, I see you that you do not have Components that Require Dynamic Passwords enabled. Seems like the GP client saves and reuses the user creds after a successful connection, regardless if the save creds option is set. If you forcibly logout a user after a period of time this is troublesome... You don't actually seem to need to have a dual auth setup, as the section would seem to imply, to use the dynamic password option. From the note attached "...to authenticate users as opposed to using saved credentials. As a result, the user will always be prompted to enter new credentials..."
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-06-2022 11:08 PM
Hi,
No, ı dont see, but I have already blocked using sso under agent>app
.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-06-2022 11:25 PM
Hi,
VPN Authentication is done with ldap. Windows users are included in the domain, they login with ldap.I guess it somehow gets this data from the cache.
Also even though the Auto Restore VPN Connection Timeout duration is selected as 0 min. When these users change wi-fi, they can establish a direct connection without entering a username and password.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-26-2022 12:52 AM
Have you solved this issue? We have same issue.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-06-2022 03:05 AM
No, unfortunately we couldn't. After gp update the problem has not recurred so far.
- 1 accepted solution
- 8926 Views
- 8 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Active Passive Failover in AWS in VM-Series in the Public Cloud
- [FIREWALL] - Commit Issue in Next-Generation Firewall Discussions
- OSPF process crashes after manual HA Failover in Next-Generation Firewall Discussions
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- Palo Alto 820 - Software Update for CVE-2026-0300 in Next-Generation Firewall Discussions