- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
- LIVEcommunity
- Discussions
- Security Operations
- Cortex XDR Discussions
- Who rated this post
Who rated this post
Disable Protection Rule for Remote Initiated Behavioral Threat
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-22-2024 02:08 PM - edited 02-22-2024 02:12 PM
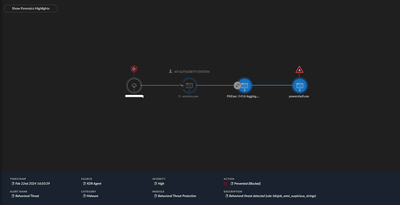
We are creating a custom service to handle automatically checking and updating programs (similar to PDQ Deploy, or an RMM tool).
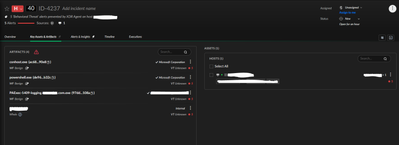
We've signed the the created service and tried several ways to disable it from being blocked. The problem is, we are very limited in what we can target with the disable prevention rules.
Has anyone run into this and actually allowed it through. We could change the commands to not trigger the alerts as we can see what triggered them by getting the alert data.
The point is that if we signed what is running, we'd like to be able to build it out without worrying about coding around XDR's every changing (and hard to extract behavioral rules).
We've already attempted to:
- allow our signature in a disable prevention rule
- allow the ending powershell process with a wildcard cmd line argument
The problem seems to be that the point where the block is triggered happens before the signer is considered. The artifacts show our service as being signed.
Screenshot of causality chain nodes below.
Disable Prevention Rules does not give us any way to address this.