- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Does the HA Passive PA-VM Firewall forwards the logs to syslog server
- LIVEcommunity
- Discussions
- Network Security
- VM-Series in the Public Cloud
- Does the HA Passive PA-VM Firewall forwards the logs to syslog server
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Does the HA Passive PA-VM Firewall forwards the logs to syslog server
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2021 04:20 AM
Team,
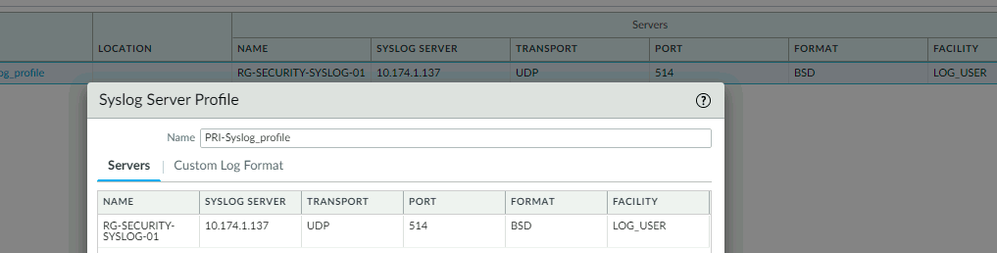
We have the pair of PA-VM deployed in HA A-P mode. The log-forwarding facility is enabled and the logs are being forwarded to the external Syslog-Server.
It is noticed that the Passive node is not sending any logs to the Syslog-Server. Only the Active node is sending the logs.
I am trying to understand that all the configurations are identical, and the communication to the Syslog-Server is directed from MGMT NIC directly to the servers on both the firewalls. So the Passive node must be sending the logs (system-log, config-log etc.).
Please let us know the behavior.
Thanks,
SPM
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2021 05:11 AM
Thank you for your post @Muruganandham.SP
Since passive Firewall is not passing any traffic, you will not see any Traffic Log, Threat Log,.. etc, however System Log as well as Configuration Log will be generated and if configured correctly sent to external syslog server.
Since you mentioned that configuration is identical and active Firewall is sending logs to external syslog server as a next thing I would check settings that are not HA synchronized, for example DNS server IP address. If you have configured Syslog as FQDN make sure that passive Firewall can resolve the IP address.
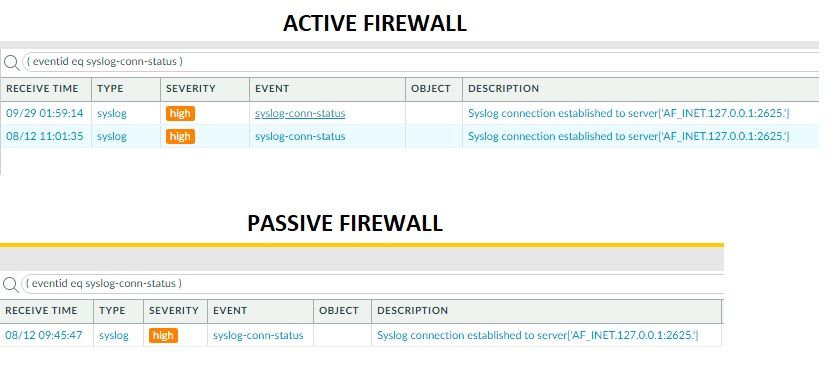
Also check System logs to see any related events: ( eventid eq syslog-conn-status ).
Kind Regards
Pavel
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2021 05:25 AM
@PavelK Yes, the Passive node cannot write any Traffic/Threat logs unless he becomes an active. So it is expected not to see Traffic/Threat logs.
The concern here is, system-log config-log etc.
Yes, we do have the proper reachability to the Syslog server, FQDN works fine, DNS settings are made correctly and works fine. HA status is 'In-Sync'.
The system-log in Passive node states that the syslog-server is 'connected' (it shows the old date though, while the Active node shows two different dates with newer date)
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2021 05:54 AM
Thank you for quick reply @Muruganandham.SP
Sorry if I ask silly question, but based on your screen shot, the destination IP address is: 127.0.0.1 which is reserved loopback IP address. It looks like it is sending logs to itself?
Kind Regards
Pavel
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2021 06:04 AM
1. Passive firewall will not forward logs until failover
2. However, this looks like you have configured transport protocol as TCP in syslog server profile and an internal connection is established to syslog-ng on port 2625 and this keeps popping up in system logs.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2021 09:31 AM
I have the Syslog configured with UDP only. And I believe the Passive node should forward the system-log, config-log kind of logs to the Syslog-Server.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-05-2021 03:45 PM
Thank you for update @Muruganandham.SP
I am running in my environment the same setup where Passive Firewall is sending System logs to syslog server and I can confirm that I can see logs on server side, so this should be definitely working.
As next step to troubleshoot, I would advice to check detailed output from: less mp-log syslog-ng.log and take packet capture on management interface: tcpdump filter "port 514" (https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000CleECAS).
Kind Regards
Pavel
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-01-2021 07:52 AM - edited 11-01-2021 07:55 AM
Hi Team,
I've just opened the ticket with the TAC. Also on the other hand I'd performed all the above steps mentioned by @PavelK prior coming to this live-community forum.
The behavior is, no packets were observed at the Passive device. Had a multiple sessions with the TAC. Even on a remote-session, the TAC couldn't see any packets being forwarded at the Passive unit.
Restarted the management-server, device-server, vardata-receiver, log-rcvr, Also restarted the syslog-ng. The Passive unit's tcpdump and debug log-receiver statistics didn't show any clue about the packet-forward to syslog-server. So none of the above activities has helped.
Post couple of weeks, TAC has again joined the call. And interestingly, without doing anything on Passive Unit, now the tcpdump output show that the packets are being forwarded to the syslog-server. While the debug log-receiver statistics command doesn't show any numbers incrementing.
Regards,
Muruganandham SP
- 8715 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Active Passive Failover in AWS in VM-Series in the Public Cloud
- OSPF process crashes after manual HA Failover in Next-Generation Firewall Discussions
- Why would an active firewall in an active-passive HA configuration broadcast gratuitous ARPs every 60 seconds? in Next-Generation Firewall Discussions
- Panoarama M-300 Log Storage in Panorama Discussions
- Upgrading Active/Passive pair, pause in between upgrades? in Next-Generation Firewall Discussions