- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
USER-ID policies + FULL azure ad
- LIVEcommunity
- Discussions
- Network Security
- VM-Series in the Public Cloud
- Re: USER-ID policies + FULL azure ad
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-02-2023 06:08 AM
Hello everyone ,
I'm having a problem that I can't solve.
I'll explain the context.
I am in full AZURE AD.
My computers are enrolled via INTUNE
I would like to be able to set up user-based firewall rules.
I set up the "cloud identity engine" (linked to azure ad), I can see my groups and my users in the palo alto.
When I create a firewall rule and I associate a user to it, the rule has no effect on this user.
Do you have an idea ?
Thanks in advance
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-05-2023 02:38 PM
I have some questions, but I think you are missing the User-IP mapping as the cloud identity engine won't provide IP. So far I heard only GP always one can help
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-04-2023 02:55 PM
Hello,
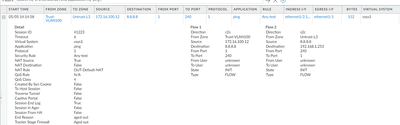
I would check the policy you created against a traffic log to see if you accidentally missed something. Also check how the users names are displayed in the logs vs how they are in the policy.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-05-2023 05:16 AM
HI @OtakarKlier
Thank you for taking the time to look at my question?
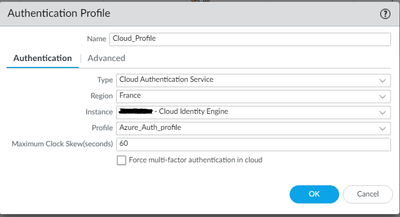
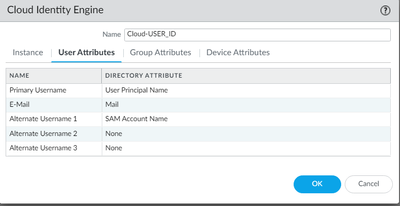
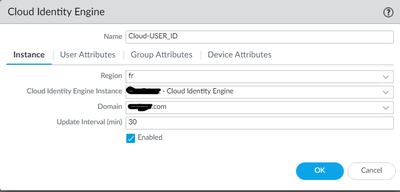
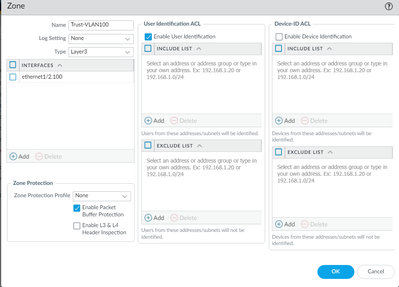
Here is some screenshot of my configuration
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-05-2023 07:32 AM
Hello,
Honestly I never had to deal with Azure AD, bt something is off. I would open a case with PAN support on this one. Also just a few suggestions:
- I would recommend having a zone protection profile for you inside zones as well as external zones.
- Hopefully you are using a secure DNS. I understand that the google DNS was just ICMP only.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-05-2023 02:38 PM
I have some questions, but I think you are missing the User-IP mapping as the cloud identity engine won't provide IP. So far I heard only GP always one can help
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-09-2023 01:58 AM
Good morning
I simply did a test with a ping to 8.8.8.8
But the configuration is not finalized yet
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-03-2023 04:37 AM
Hi @LCutman
Do you have an authentication rule that uses the auth profile in your first sceenshot? Your users need to authenticate to CIE before it can map users to IPs. The documentation is not particularly clear but I'm willing to lab it up as I'm doing a GP deployment for a customer in the same situation and looking at this it may be a better option...
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-05-2023 05:18 AM
@mb_equate
Thanks for the video but I had seen it before.
If I understand correctly the only way to be able to use the cloud engine (with azure ad) to map the IP addresses is to use Global protect
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-05-2023 05:51 PM
Looking into this further, it appears to be the captive portal that actually does the mapping rather than CIE - an authentication rule steers the client to the captive portal which authenticates the user (presumably via a CIE auth profile), once the user is authenticated the portal provides the mapping data as it would in any other case. In theory you could do this without CIE if you used AzureAD as your authentication source in the rule.
I've found the documentation rather sketchy when it comes to this, e.g. this KB article states CIE does not have the functionality to learn user to IP mapping which is correct - CIE itself does not provide the mapping however the documentation suggests you run show user ip-user-mapping all after configuring CIE which wouldn't work until you have a mapping source which CIE does not provide.
The best I could find is this video https://youtu.be/_ppC2H8Ta_M?t=452 which loosely shows the auth flow to CIE via a captive portal which is a standard method for mapping users to IPs when you don't have a Windows event log source (e.g. non-domain joined / BYOD): Map IP Addresses to Usernames Using Authentication Portal (paloaltonetworks.com)
So no, you don't need GlobalProtect, but I'm yet to be convinced this is reliable method that would be transparent to users without understanding the SSO methods (which will need to be either certificate based or dependent on existing authentication tokens).
It would be great if PAN could demonstrate a working end-to-end solution for this.
- 1 accepted solution
- 7735 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Security Policy Disappears After Commit – Palo Alto in Azure with Panorama in Next-Generation Firewall Discussions
- GlobalProtect Name Normalization issue in GlobalProtect Discussions
- Azure to OnPrem Connectivity issue in Next-Generation Firewall Discussions
- Help Needed: NAT & Security Policy Configuration for Azure LB → Palo Alto → DMZ Webserver (Public IP) in VM-Series in the Public Cloud
- UserID mapping for users usings Azure VPN Gateway and AzureAD in Next-Generation Firewall Discussions