- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
[Closed] Join the Discussion: LIVEcommunity Cyber Elite Experts
- LIVEcommunity
- Get Started
- News & Events
- Events
- Ask Me Anything (AMA) Event Discussions
- [Closed] Join the Discussion: LIVEcommunity Cyber Elite Experts
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-16-2022 10:07 AM - edited 06-30-2022 09:55 AM
Ask your questions now through June 30 as the LIVEcommunity Cyber Elite Experts will be available in a Q&A session for an opportunity to learn, join in, ask questions, and meet our experts! The Ask Me Anything (AMA) Event will be an opportunity to ask our Cyber Elite Experts questions about a range of technologies, solutions, and how they can help you find what you need.
Post your questions below Thursday, June 16 through Thursday, June 30, 2022!
To participate in this event, please use the Reply button below to ask your questions. Come back on Thursday, June 30 from 8 a.m. to 10 a.m. PT to join the event as our experts answer your questions!
Please be sure to click Like if a post is helpful to you and to "Accept as Solution" to let everyone know that the answer to your question hits the mark!
Want to learn more details about the event? Check out this article.
- Labels:
-
Cyber Elite Program
-
Cyberelite
-
events
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-18-2022 04:13 AM - edited 06-18-2022 04:19 AM
As your question is more than a issue than a general tech question I will provide some feedback even before the session, just for example.
It could be what you said as you did a deep investigation and if this is the issue then better raise a feature request to palo alto to add this as an option in the Globalprotect portal app settings.Also most of the Cyber Elites don't work directly for Palo Alto as we are community members just like you and we love playing with Palo Alto 🙂
Still as I have not used globalprotect on Linux I can't say if you have to also check the Globalprotect SSL gateway certificate if it is valid and the CA certificate that signed it is imported as a trusted cert on your linux system as newer version of the globalprotect agent want this. Also you can check your globalprotect's version and firewall version for "Known Issues" or "Addressed Issues" with the Linux globalprotect agent as Palo Alto has public articles for this.
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClixCAC
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA14u000000HCF4CAO&lang=en_US
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-30-2022 08:33 AM
@rtsedaka wrote:
What a great opportunity for us to get another source of info! Thank you for that.
I have some very specific config questions. I would like to know the best way to get some expert help. Is there a suggested action I should take?
TIA
Hello @rtsedaka ,
As security professionals, its best to make sure we dont give out too much information publicly. If you can obfuscate or change the data I would say go ahead and post it into the community.
Example:
My public ip is 1.1.1.1 and want to nat to an internal server ip 192.168.1.1, how would I do that? Just make sure these are not your ip's, or use use x.x.x.x, y.y.y.y., etc. Or if you screen capture, you can block out certain parts. What I do is do a screen capture, open in paint, then block out the bits I dont want public, then screen capture again. This way you cannot de-obfuscate the blocked out bits.
If its a question that you cannot truly change or obfuscate, I would say support is the best method.
That said we are here to help!
Cheers!
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-30-2022 08:44 AM
@AVaidya1 wrote:
Hello Cyber Elite Experts,
Your posts are extremely helpful.
My question: What is the best way to connect with peers in this community? How do you connect and stay connected?
Thank you for all you do to help the community!
Hi AVaidya1
I think the first thing I need to do, is to THANK YOU for the contributions that you have posted and links to various PANW related configuration tips/tricks. It is impressive and supportive to see the breadth of youtube videos and other great events/communications that are posted on the LiveCommunity.
To answer your question about how to connect with peers, I really find that the messaging platform within the LiveCommunity to send direct messages to various users or CyberElites, has been rewarding for me. I have communicated a few times with @BPry , @reaper,@OtakarKlier via direct messages. Likewise, I have ask community members to contact me and I assisted in resolving their issues, giving high value customer support. From there, we could always connect up at a 2022 Palo Alto Ignite in Dec 2022 😛
Thanks for the message.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-30-2022 08:49 AM
@vsharma1 wrote:
Could you please share how Best Practice Assessment (BPA) delivered actionable insights?
The Best thing about BPA is it gets you results based on your Industry.
Also other thing I like was to compare the BPA with any other Industries.
That way you can see how to config PA with more Security Posture.
Also it tells us how to more lock down the security profiles and the firewall configuration etc.
It is great tool to compare your current config with BPA results and do the needful.
Regards
Help the community: Like helpful comments and mark solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-30-2022 08:59 AM
@PavelK wrote:
I would like to ask Cyber Elite members their suggestion/opinion/advice how to approach a network segmentation in an organization with below scenario:
- 100+ sites (mixture of MPLS L2 VPN, MPLS L3 VPN, DMVPN).
- up to 1500 servers globally.
- Mixture of on-prem Data Centers with 100G DCI and also all major Public Cloud Providers.
- Different business units, some of them with a strict change control and reluctant to make changes.
Would you opt for hw or sw based segmentation / micro segmentation?
Thank you in advance!
BTW, because of time zone, I will not be able to attend live, but would still love to hear from you.
Good Day @PavelK
There are many different directions that this conversation could go through. Suffice to say, communication with your reseller and PANW Sales Engineers should definitely be part of the conversation. Generally speaking, from a security posture and enforcement perspective, Prisma Access is the BEST solution for that. It allows remote sites (and Global Protect users) to communicate to the Prisma Access cloud, with programming via the Panorama, to manage the policies and security profiles to sure communication.
At the remote sites, there should be conversations about the proper FW sizing (PA410 at smallest sites, to perhaps PA52xx series at larger campuses. The Panorama can manage the security policies for the branch offices, yet the real question, about segmentation is about designing the network to have the FW be the inspection point for east/west traffic (i.e, the default gateway for network,with limited L3 switches in the design). Again, because this is a large oppotunity a HLDS (high level design session) with PANW Professional Services, may be a reasonable first step towards narrowing down the focus and scope of your generalized question.
Thank you.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-30-2022 09:32 AM
@vsharma1 wrote:
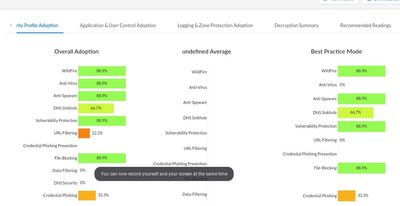
What's one feature that you like about Best Practice Assessment (BPA)? And, how does it help you to achieve greater security posture?
Hello @vsharma1 ,
I personally like the 'Security Profile Adoption', it lets me know which security policies may not have proper security profiles applied. While there are cases where you might not want to apply any, ie, Palo Alto updates, its still a good overview. Also upper managemt likes charts and graphs :).
Example:
Hope this helps,
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-30-2022 09:41 AM
@AVaidya1 wrote:
Hello Cyber Elite Experts,
Your posts are extremely helpful.
My question: What is the best way to connect with peers in this community? How do you connect and stay connected?
Thank you for all you do to help the community!
Hello @AVaidya1 ,
I start off by asking those in the local area and see what groups are around. Internet searches are also a good method. BSides is a good example of a group that are local. Also the Fuel user group has local chapters, https://www.fuelusergroup.org/. I try and follow some twitter folks but it tough at times to muddle through the minutia. Once you break into one of the groups, ask around to see what other groups are in the area or that others follow. Black Hills Infosec is a company that puts on a conference and has weekly/daily free videos related to security, etc. They also have discord channels you can join and chat around. There are many out there, I hope this gives you a bit of a start.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-30-2022 09:57 AM
@PavelK wrote:
I would like to ask Cyber Elite members their suggestion/opinion/advice how to approach a network segmentation in an organization with below scenario:
- 100+ sites (mixture of MPLS L2 VPN, MPLS L3 VPN, DMVPN).
- up to 1500 servers globally.
- Mixture of on-prem Data Centers with 100G DCI and also all major Public Cloud Providers.
- Different business units, some of them with a strict change control and reluctant to make changes.
Would you opt for hw or sw based segmentation / micro segmentation?
Thank you in advance!
BTW, because of time zone, I will not be able to attend live, but would still love to hear from you.
Hello @PavelK ,
That's an easy one, kidding of course 😉. The bigger the company the more 'it depends' are the answers. Obviously I would recommend Palo Alto devices at all the sites and have as much traffic flow through them as possible. One thing I know companies are shying away from are VPN's. That is my biggest pet peeve since they are tried and true, thanks marketing 😉, not saying Prisma is not worth it. If you use a Palo Alto then you can achieve zero trust for your endpoints. All traffic between the end users machines is encrypted, logged, analyzed, so proxies are taken care of and zero trust on the endpoint. This is also true for the inside of your network, instead of allowing whatever device to connect to your network to be allowed access, only allow limited access to the internet and have all users VPN in. Now you have NAC (posture validation of endpoints so no one sneaky can VPN in with a non corp asset) and zero trust to other workstations and servers. This makes your compliance a lot easier and no additional need to additional products, additional proxies or NAC products. I'm a huge fan of maximizing what you already have or using one technology to do it all, well almost :). Best part to get the exes to go for it, cost savings 😁, less purchasing, etc.
The servers are the toughest, but you ca group them by feature and put them into vlans anchored at the PAN so you can put policies of what can flow in and out.
Definitely a long roll out but once you have then overall vision of what you want it to look like, its just a matter of rolling up your sleeves and getting to it. Sorry no easy button ☹️.
Hope this helps. I love talking and thinking about this stuff so feel free to keep addition specifics to the post and let the community chime in!
Cheers!
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-30-2022 01:14 PM
Hi @PavelK
That's a tough one. So ...
Wherever possible I would use VM series firewalls for the segmentation. You simply have more flexibility with the sw based approach than with hw. In case you need more throughput you simply extend the HA to a HA cluster with up to 16 nodes per cluster. Of course if you need 100G throughput for single sessions, then there is no other option than the big HW firewalls from paloalto.
For a recommendation for the rest of the situation I would need some more information. As there are quite a few locations with different MPLS lines, I assume there is no additional internet access at these locations and all traffic including internet traffic needs to go to HQ. This makes it easier as you have less firewalls to control. Also here it really depends on the security requirements of the company. From routing all locations together up to separate even different subnets at these locations there are more than one recommended setups - it all depends on the budget and the security requirements.
Regarding the different business units: if there are such different units I would make sure that their systems are located behind dedicated firewalls so unit a will not have access to unit b. In order to keep at least some control I would recommend to use panorama with pre rules and the units only have access to post rules or only rules local on the firewall. With that you at least have aome control with a company policy.
At least on prem I would go the "old" way with the network segmentation and not do micro segmentation as I think in a lot of cases there is no need to have everything sent over a firewall. Of course it is also for blocking connection as near as possible to the source systems but this can be done easily with the host firewalls or with Cortex XDR which has even way more advantages regarding the security standard in your network.
With more informations about the requirements the answer might be better if you ask the live community but this can be time-intense for the ones that reply to queations here - but we are all in this together and happy if we can help. I hope you are not disappointed with the answer.
Cherrs,
Remo
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-01-2022 10:16 AM - edited 07-01-2022 10:28 AM
Thanks @S.Cantwell as I had emergency call to join the session in the last moment. @darrin.goodman I also think the firewalls may also need an upgrade the firewalls not only globalprotect as the issue with the linux was that the globalprotect on Linux did not like the firewall using " unsecure renegotiation" if I remember so also the firewalls can be upgraded and maybe if nothing helps try also switching to ipsec if the VPN is using SSL.
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000PPY1CAO
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-01-2022 10:43 AM - edited 07-01-2022 10:58 AM
As @S.Cantwell mentioned Prisma Access and they now have the nice option for Inbound applications that does not need an n-prem firewall for every site where you have public Internet applications as most SASE offerings don't have that. Still for your big setup on some big Data Centers you will probably need on-prem firewalls for the Public Applications, so I see it as Steve mentioned with better going with Prisma Access Panorama Managed that Cloud Managed Prisma Access that does not support on-prem firewalls. Also Prisma Access is having a new ZTNA broker/agent that could be a better way to build the ipsec tunnels to the Prisma Access cloud than on-prem router/firewall ipsec/gre tunnel but you can book a free Palo Alto Virtual Hands-on Workshop for Prisma Access and see it for yourself as Palo Alto has many free workshops/trials/demos on their site.
Provide Secure Inbound Access to Remote Network Locations (paloaltonetworks.com)
Also for zero trust east to west sever traffic @PavelK can consider also Prisma Cloud in some cases especially containers and Kubernetes or the Palo Alto CN series Firewall but better compare to see which is better as I had asked before this question and I got help in this same forum, but basically as I see it Prisma Cloud is better as filtering the access between containers and processes with its machine learning (the so called zero trust) while CN-Series firewalls is a firewall in a container that does more scanning like malware on already allowed traffic and in youtube there are a lot of videos by the palo alto live channel.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-16-2022 12:52 PM - edited 06-16-2022 12:54 PM
This seems to be a catch-all for technical questions, so my apologies if I am not posting in the right location. It's been difficult to figure out how to obtain support as an end-user.
The university I am employed by has recently moved from its old VPN to using GlobalProtect. While previously using a derivative of Ubuntu 20.04, I was able to successfully launch and use the GlobalProtect VPN client. I have recently upgraded to the latest Ubuntu 22.04 operating system, and I am no longer able to use the GP VPN client due to a change to the latest version of OpenSSL.
When launching the VPN client, the associated app's icon would blink on and off in my task bar, but nothing would ever happen. After implementing this workaround, I was able to launch the gui VPN client, input my gateway, launch the authentication browser, successfully authenticate, and send a push to my phone (2FA). After that, a window would open indicating the following error:
SSL handshake failed
Failed to load URL [gateway address]
QtNetwork Error 6
This is a known issue and is described in this bug report. Comment #28 in the bug report indicates that the OpenSSL developers have made a deliberate decision disable unsecure renegotiation. It seems to me that a possible fix could be for the GlobalProtect VPN client to offer an option to enable unsecure renegotiation in OpenSSL. You can see this change to OpenSSL in the commit as well as in the upstream migration guide.
In order to access work-related electronic systems remotely, it's essential that the GlobalProtect VPN client is working properly for me, although as a Linux user I realize that I am in the minority unfortunately. The VPN client worked just fine prior to upgrading my OS to the latest version so it didn't occur to me that there would be any issues after upgrading. Could you please look into applying a fix so that the GlobalProtect VPN client is compatible with the current version of OpenSSL? I would be happy to serve as a test subject for you if needed. I am running OpenSSL 3.0.2 15 Mar 2022.
Thank you!
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-18-2022 04:13 AM - edited 06-18-2022 04:19 AM
As your question is more than a issue than a general tech question I will provide some feedback even before the session, just for example.
It could be what you said as you did a deep investigation and if this is the issue then better raise a feature request to palo alto to add this as an option in the Globalprotect portal app settings.Also most of the Cyber Elites don't work directly for Palo Alto as we are community members just like you and we love playing with Palo Alto 🙂
Still as I have not used globalprotect on Linux I can't say if you have to also check the Globalprotect SSL gateway certificate if it is valid and the CA certificate that signed it is imported as a trusted cert on your linux system as newer version of the globalprotect agent want this. Also you can check your globalprotect's version and firewall version for "Known Issues" or "Addressed Issues" with the Linux globalprotect agent as Palo Alto has public articles for this.
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClixCAC
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA14u000000HCF4CAO&lang=en_US
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-26-2022 01:44 AM - edited 06-26-2022 01:44 AM
What a great opportunity for us to get another source of info! Thank you for that.
I have some very specific config questions. I would like to know the best way to get some expert help. Is there a suggested action I should take?
TIA
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-27-2022 10:44 AM
Could you please share how Best Practice Assessment (BPA) delivered actionable insights?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-27-2022 10:45 AM
What's one feature that you like about Best Practice Assessment (BPA)? And, how does it help you to achieve greater security posture?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-28-2022 03:58 PM
Hello Cyber Elite Experts,
Your posts are extremely helpful.
My question: What is the best way to connect with peers in this community? How do you connect and stay connected?
Thank you for all you do to help the community!
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-28-2022 05:00 PM
Hello Cyber Elites,
This is a question from @jsalmans. He is having issues with FTP inbound decryption.
"
I've had inbound decryption set up for our FTP server for some time. We noticed an issue after updating to 10.0.8 (we're now on 10.1.5-h1 ) where people seemed to not be able to connect anymore. After investigating, it appears that in Filezilla they are actually able to connect but it looks like they aren't because a TLS error occurs and the LIST command fails. Right-clicking on the remote side and hitting Refresh several times will often eventually complete the directory listing. This is with FTPS set to "Require explicit FTP over TLS" and with the Transfer Method set to Default (which I think may be Passive). This issue appears to be intermittent and sometimes it seems to connect fine.
Further investigation also showed the following:
- The TLS error mentioned above when the LIST command fails is "GnuTLS error -110: The TLS connection was non-properly terminated." followed by "Server did not properly shut down TLS connection" followed by "The data connection could not be established: ECONNABORTED - Connection Aborted" and then followed by "Failed to retrieve the directory listing". Decryption logs GUI shows "General TLS Protocol Error" when this happens.
- Error showing: "Server sent unsorted certificate chain in violation of the TLS specifications" at the start of each connection attempt
- Changing the Transfer Method to Active seems to make it more reliable as far as connecting without a TLS error and getting the directory listed automatically (it still complains about the certificate chain)
- Even with Active set, we then sometimes get a message indicating that the connection isn't secure because the server previously was detected as supporting TLS session resumption (I'm assuming this was either working before through the Palo and now it isn't or it's because when we've tested we've connected directly to the server which supports it)
- Trying another client, WinSCP also doesn't list the directory on Passive.. it works when changed to Active. I have no idea if it is getting any errors/warnings as I haven't noticed if there is a log view in that software.
- Turning off the decryption rule resolves all of the issues.. the FTP connection is also a lot less verbose (in another words, when decryption is turned on there is a lot more chatting with commands/responses between the client and the firewall/server)
It looks like someone else has run into an issue like this before with Passive FTP and it was related to an issue with the content packs
https://live.paloaltonetworks.com/t5/general-topics/passive-ftp/td-p/11573
Anyone else having any issues or have any experience in what I can do to resolve this?
Thanks! "
Stay Secure,
Jay
Don't forget to Like items if a post is helpful to you!
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-28-2022 05:22 PM
I would like to ask Cyber Elite members their suggestion/opinion/advice how to approach a network segmentation in an organization with below scenario:
- 100+ sites (mixture of MPLS L2 VPN, MPLS L3 VPN, DMVPN).
- up to 1500 servers globally.
- Mixture of on-prem Data Centers with 100G DCI and also all major Public Cloud Providers.
- Different business units, some of them with a strict change control and reluctant to make changes.
Would you opt for hw or sw based segmentation / micro segmentation?
Thank you in advance!
BTW, because of time zone, I will not be able to attend live, but would still love to hear from you.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-30-2022 08:33 AM
@rtsedaka wrote:
What a great opportunity for us to get another source of info! Thank you for that.
I have some very specific config questions. I would like to know the best way to get some expert help. Is there a suggested action I should take?
TIA
Hello @rtsedaka ,
As security professionals, its best to make sure we dont give out too much information publicly. If you can obfuscate or change the data I would say go ahead and post it into the community.
Example:
My public ip is 1.1.1.1 and want to nat to an internal server ip 192.168.1.1, how would I do that? Just make sure these are not your ip's, or use use x.x.x.x, y.y.y.y., etc. Or if you screen capture, you can block out certain parts. What I do is do a screen capture, open in paint, then block out the bits I dont want public, then screen capture again. This way you cannot de-obfuscate the blocked out bits.
If its a question that you cannot truly change or obfuscate, I would say support is the best method.
That said we are here to help!
Cheers!
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-30-2022 08:44 AM
@AVaidya1 wrote:
Hello Cyber Elite Experts,
Your posts are extremely helpful.
My question: What is the best way to connect with peers in this community? How do you connect and stay connected?
Thank you for all you do to help the community!
Hi AVaidya1
I think the first thing I need to do, is to THANK YOU for the contributions that you have posted and links to various PANW related configuration tips/tricks. It is impressive and supportive to see the breadth of youtube videos and other great events/communications that are posted on the LiveCommunity.
To answer your question about how to connect with peers, I really find that the messaging platform within the LiveCommunity to send direct messages to various users or CyberElites, has been rewarding for me. I have communicated a few times with @BPry , @reaper,@OtakarKlier via direct messages. Likewise, I have ask community members to contact me and I assisted in resolving their issues, giving high value customer support. From there, we could always connect up at a 2022 Palo Alto Ignite in Dec 2022 😛
Thanks for the message.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-30-2022 08:48 AM
@nikoolayy1 wrote:
As your question is more than a issue than a general tech question I will provide some feedback even before the session, just for example.
It could be what you said as you did a deep investigation and if this is the issue then better raise a feature request to palo alto to add this as an option in the Globalprotect portal app settings.Also most of the Cyber Elites don't work directly for Palo Alto as we are community members just like you and we love playing with Palo Alto 🙂
Still as I have not used globalprotect on Linux I can't say if you have to also check the Globalprotect SSL gateway certificate if it is valid and the CA certificate that signed it is imported as a trusted cert on your linux system as newer version of the globalprotect agent want this. Also you can check your globalprotect's version and firewall version for "Known Issues" or "Addressed Issues" with the Linux globalprotect agent as Palo Alto has public articles for this.
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClixCAC
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA14u000000HCF4CAO&lang=en_US
Hello there. Thanks for the messaging. I am certain the Linux endpoints, regardless of OS are experiencing this issue and PANW dev team is more than likely working on a newer version of the Global Protect for Linux. As an customer of PANW technologies, we would recommend that you contact your regional Palo Alto Networks SE (sales engineer) and confirm that there is a FR# (feature request) that has been assigned to resolving this issue.
Thank you again for your comments.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-30-2022 08:49 AM
@vsharma1 wrote:
Could you please share how Best Practice Assessment (BPA) delivered actionable insights?
The Best thing about BPA is it gets you results based on your Industry.
Also other thing I like was to compare the BPA with any other Industries.
That way you can see how to config PA with more Security Posture.
Also it tells us how to more lock down the security profiles and the firewall configuration etc.
It is great tool to compare your current config with BPA results and do the needful.
Regards
Help the community: Like helpful comments and mark solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-30-2022 08:59 AM
@PavelK wrote:
I would like to ask Cyber Elite members their suggestion/opinion/advice how to approach a network segmentation in an organization with below scenario:
- 100+ sites (mixture of MPLS L2 VPN, MPLS L3 VPN, DMVPN).
- up to 1500 servers globally.
- Mixture of on-prem Data Centers with 100G DCI and also all major Public Cloud Providers.
- Different business units, some of them with a strict change control and reluctant to make changes.
Would you opt for hw or sw based segmentation / micro segmentation?
Thank you in advance!
BTW, because of time zone, I will not be able to attend live, but would still love to hear from you.
Good Day @PavelK
There are many different directions that this conversation could go through. Suffice to say, communication with your reseller and PANW Sales Engineers should definitely be part of the conversation. Generally speaking, from a security posture and enforcement perspective, Prisma Access is the BEST solution for that. It allows remote sites (and Global Protect users) to communicate to the Prisma Access cloud, with programming via the Panorama, to manage the policies and security profiles to sure communication.
At the remote sites, there should be conversations about the proper FW sizing (PA410 at smallest sites, to perhaps PA52xx series at larger campuses. The Panorama can manage the security policies for the branch offices, yet the real question, about segmentation is about designing the network to have the FW be the inspection point for east/west traffic (i.e, the default gateway for network,with limited L3 switches in the design). Again, because this is a large oppotunity a HLDS (high level design session) with PANW Professional Services, may be a reasonable first step towards narrowing down the focus and scope of your generalized question.
Thank you.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-30-2022 09:32 AM
@vsharma1 wrote:
What's one feature that you like about Best Practice Assessment (BPA)? And, how does it help you to achieve greater security posture?
Hello @vsharma1 ,
I personally like the 'Security Profile Adoption', it lets me know which security policies may not have proper security profiles applied. While there are cases where you might not want to apply any, ie, Palo Alto updates, its still a good overview. Also upper managemt likes charts and graphs :).
Example:
Hope this helps,
- 11 accepted solutions
- 25661 Views
- 21 replies
- 7 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- AMA June 30, 2022: LIVEcommunity Cyber Elites in Ask Me Anything (AMA) Events
- AMA Oct 27: Education Services Training and Credentialing Opportunities for All Things Cortex in Ask Me Anything (AMA) Events
- (Ended) Join the discussion: LIVEcommunity Cyber Elite Experts in Ask Me Anything (AMA) Event Discussions
- AMA July 28, 2021: LIVEcommunity Cyber Elite Experts in Ask Me Anything (AMA) Events