
- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Palo Alto Networks dives into how your firewall can perform Geolocation and Geoblocking to help you keep your network safe in different regions. Learn how to set security policies, decryption policies, and DoS policies for your firewall.
Geolocation is the estimation of the real-world geographic location of an object. In our specific use case, I am referring to the physical location of your PC, laptop, mobile device, or from the servers you are trying to reach.
Geoblocking is when you start restricting or allowing access to content based on the geolocation.
The next-generation firewall supports creation of policy rules that apply to specified countries or regions. The region is available as an option when specifying source and destination for security policies, decryption policies, and DoS policies. You can choose from a standard list of countries or use the region settings described in this section to define custom regions to include as options for security policy rules.
As a very simple example, let's assume you are located in the United States and would like to only allow access to addresses that are located in that country. First, you'll need to allow this access through a security rule.
You do this simply by adding the desired region or country to your security rule with an allow action.
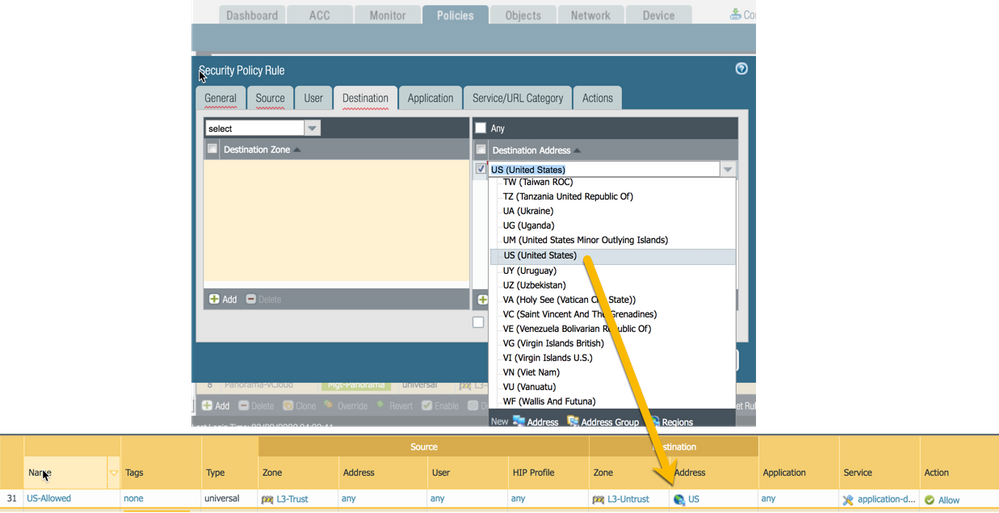
Through geolocation, the firewall will identify that the IP address you are trying to access is located in the US, and the policy will grant you the access.
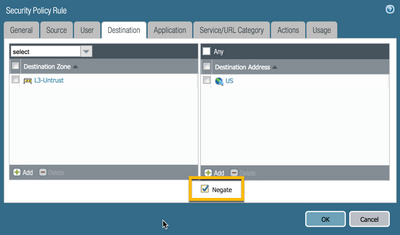
If you want to deny access to all other regions, then you can just let the default-deny rule handle it. Alternatively, if you want to catch it earlier, then you can add a rule that excludes all the US traffic and blocks it. The negate option is very useful in this specific use case. Any IP address that isn't part of the US region will hit this rule and follow the configure Action Setting (Deny for example).
Sounds very simple doesn't it? It is indeed very easy to set up.
With that said, did you know that there's a way to trick certain devices into believing you are from a totally different region?
You can easily do this through online proxies and/or anonymizers. These are tools that are freely available online, and as the name indicates, proxies or anonymizers anonymize your traffic.
What happens is that you connect to these servers and they in turn make a connection in your name to the destination server. This destination server sees an incoming connection from the proxy server, not knowing the request is actually coming from you.
Often, these tools are used for shady practices or to hide what you're doing. Don't want your users to use these tools? Just block the access to them by blocking the URL-category 'proxy-avoidance-and-anonymizers'.
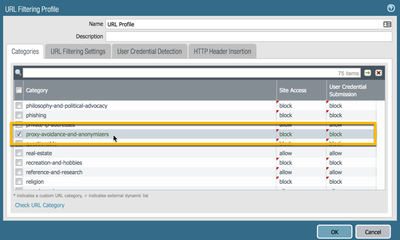
NOTE: This URL-category is only useful for outbound sessions and will not protect you from inbound connections using these proxies. I recommend researching EDL (External Dynamic Lists) for this instead.
Check out the links below if you want to know more about geolocation or geoblocking on the Palo Alto Networks firewall!
How to Block Traffic Based Upon Countries
How to Verify PAN-OS IP Region Mapping
Thanks for taking time to read the blog.
If you enjoyed this, please hit the Like (thumbs up) button, don't forget to subscribe to the LIVEcommunity Blog.
As always, we welcome all comments and feedback in the comments section below.
Stay Secure,
Kiwi out!
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
| Subject | Likes |
|---|---|
| 5 Likes Likes | |
| 5 Likes Likes | |
| 4 Likes Likes | |
| 4 Likes Likes | |
| 2 Likes Likes |




