
- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Each year, after Ignite, we have a whole bunch of great questions, a handful of strange ones, and usually a few unanswered ones. We feel that we owe it to the community to get as close as we can to a 100% reply rate, so here are a few unanswered questions and my attempt at answering to the best of my ability.
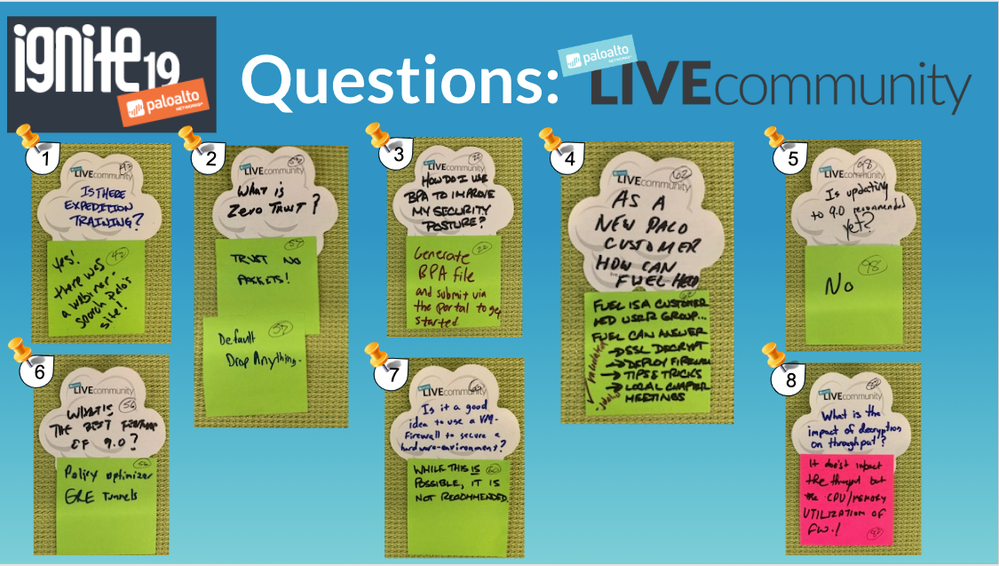
1. Is there Expedition training?
YES! There was a webinar. Check the Palo Alto Networks website.
Actually, the webinar page currently doesn't have any Expedition webinars.
That said, make sure to bookmark our webinar page. You never know when an Expedition webinar might pop up there. In the meantime, there's plenty of information and guides on our Expedition portal page: Welcome to Expedition.
2. What is Zero Trust?
Trust no packet!
Default drop anything.
Where to start... There is plenty of information on this topic!
Check out Zero Trust information here to get you started:
Zero Trust - Never trust, always verify
Reducing Risk with Zero Trust and Best Practices
What is a Zero Trust Architecture?
5 Steps to Zero Trust
3. How do I use BPA to improve my security posture?
Generate a BPA file and submit via the portal to get started.
Run the Best Practice Assessment (BPA) to evaluate your security posture and prioritize improvements. Use technical documentation to take the next steps to implement those improvements and transition safely to a best practice state without risking the availability of critical applications. Run the BPA again to measure progress and prioritize the next set of security improvements, use the documentation to implement the improvements, and repeat the cycle until you reach your security goals. Security best practices reduce the attack surface, increase visibility into network traffic, prevent known and unknown attacks, and protect what’s most valuable to your business—proprietary source code, sensitive company and customer data, critical infrastructure—whatever gives your company a competitive advantage.
Check out our transition to best practices :
Reach Your Security Goals with the BPA
4. As a new Palo Alto Networks customer, how can Fuel help?
Fuel is a customer-led user group. Fuel can answer questions about topics such as:
With Fuel membership, you’re plugged into a community of thousands of Palo Alto Networks users with endless opportunities to advance your knowledge and your career.
Don’t miss your chance to join Fuel User Group at its upcoming Spark User Summits where you’ll hear directly from Palo Alto Networks about the latest product updates, share lessons learned with fellow Palo Alto Networks users, and get in-depth discussions on the industry’s hottest topics like mobile and cloud security.
Visit the FUEL User Group for more information.
5. Is updating to PAN-OS 9.0 recommended yet?
No.
Let me nuance this answer a little bit. PAN-OS 9.0 hasn't reached the maturity level of some of our other software branches yet. If you absolutely need some of the new PAN-OS 9.0 features, then you can, of course, go ahead and download and install it. With that said, as with any new software versions, you might be experiencing some early bugs. There have been some discussion and blogs about why you should or should not upgrade to the latest (greatest?) software version.
Check out the following links on this topic:
DOTW: PAN-OS UPGRADE
BEST PRACTICES FOR PAN-OS UPGRADE
Customers only may access this resource: PAN-OS Software Release Guidance
6. What is the best feature of PAN-OS 9.0?
Obviously, this depends on the actual feature that you need. With that said, the above answers are indeed awesome new features. ^_^
Check out what's new in PAN-OS 9.0:
WHAT’S NEW IN PAN-OS 9.0
PAN-OS® New Features Guide
7. Is it a good idea to use a [VM-Series] firewall to secure a hardware environment?
While this is possible, it is not recommended.
Can it be done? Yes.
Is it a good idea? That's an opinion, I guess. 🙂
Hardware can leverage hardware offloading and purpose built chipsets, which equals speed gains. If you don't have room for hardware, you could use a VM-Series solution.
8. What is the impact of decryption on throughput?
It doesn't impact the throughput but CPU/memory utilization of the firewall.
It also depends on your hardware. For some models, decryption is being done in software as compared to hardware on the bigger Palo Alto Networks firewalls.
- Kiwi out!!
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
| Subject | Likes |
|---|---|
| 5 Likes Likes | |
| 5 Likes Likes | |
| 4 Likes Likes | |
| 3 Likes Likes | |
| 2 Likes Likes |
| User | Likes Count |
|---|---|
| 7 Likes | |
| 5 Likes | |
| 5 Likes | |
| 4 Likes | |
| 1 Likes |




