- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Exclusion process cortex?!
- LIVEcommunity
- Discussions
- Security Operations
- Cortex XDR Discussions
- Exclusion process cortex?!
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-04-2024 05:04 AM
Hi,
How can I create an exclusion in Cortex XDR to stop it from scanning a specific executable??
We have a critical software in our company, and we've noticed that Cortex is constantly analyzing it, causing the machine high CPU and MEM.
How can we exclude this file from the analysis? We want to maintain protections such as Ransomware, just excluding the process monitoring.
It's possible?
Tiago Marques
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-04-2024 05:36 AM
Hi @tlmarques, thanks for reaching us using the Live Community.
You need to create a Disable Prevention Rule.
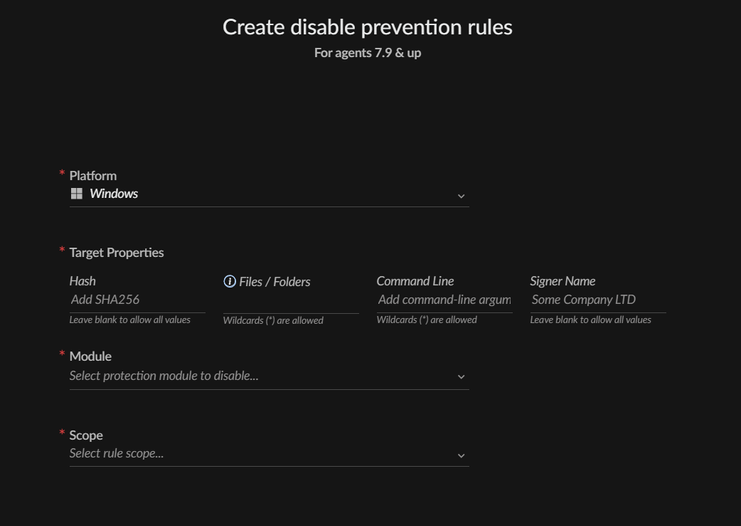
Go to Settings - Exceptions Configuration - Disable Prevention Rules, create a new one, set the name and fill the parameters:
- Set the target properties, folder location and executable name, command line, or you can use the signer. Only one is enough.
- Module: try with the Local Analysis and check how it goes, if it is an in-house software it is probably "Unknown" for Wildfire and the agent tries to analyze it locally, consuming CPU and RAM to do it.
- Scope: select the applied profile to the Endpoints with the issue.
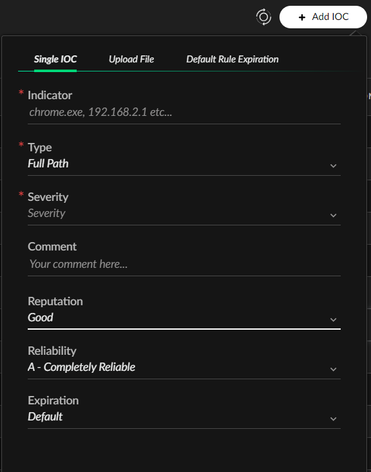
You can also go to Detecion Rules - IOC and add an IOC with the application path and/or executable hash (ni the "Type" field):
Let me know how it goes.
If this post solved your question, please mark it as the solution.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-04-2024 05:36 AM
Hi @tlmarques, thanks for reaching us using the Live Community.
You need to create a Disable Prevention Rule.
Go to Settings - Exceptions Configuration - Disable Prevention Rules, create a new one, set the name and fill the parameters:
- Set the target properties, folder location and executable name, command line, or you can use the signer. Only one is enough.
- Module: try with the Local Analysis and check how it goes, if it is an in-house software it is probably "Unknown" for Wildfire and the agent tries to analyze it locally, consuming CPU and RAM to do it.
- Scope: select the applied profile to the Endpoints with the issue.
You can also go to Detecion Rules - IOC and add an IOC with the application path and/or executable hash (ni the "Type" field):
Let me know how it goes.
If this post solved your question, please mark it as the solution.
- 1 accepted solution
- 301 Views
- 1 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Automation rule to add IP address to EDL in Cortex XDR Discussions
- Python Script isn't being executed completely in Cortex XDR in Cortex XDR Discussions
- Need a clarity about CGO , Initiator details and Target details in XDR Alerts / Incident Section in Cortex XDR Discussions
- how I add exclusion based on for an specific process (license.exe) for specific endpoint in Cortex XDR Discussions
- cortex XDR add SHA1 detection in Cortex XDR Discussions