- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
GlobalProtect 5.0 for iOS 12 and User Certificates
- LIVEcommunity
- Discussions
- General Topics
- GlobalProtect 5.0 for iOS 12 and User Certificates
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-17-2018 02:43 PM
I have several customers (and my homelab) that leverage user certificates issued from Active Directory Certificate Authorities as a second authentication factor. Since upgrading to the new 5.0 client for iOS, the client errors out on connection to the portal, indicating that the required certificate cannot be found. If I attempt to connect to the same portal via the 4.1 client, it works flawlessly. Upgrading to iOS12 prevents me from using the 4.1 client, and I fear that many of my customers' users will upgrade their own devices to iOS12, not knowing the problems this may cause.
Is anyone else having problems with user certificates and the new 5.0 client?
Thanks!
Mark Rosenecker
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-04-2018 01:35 AM
Hello everyone,
i would like to implement IOS12 and GP 5 App on Apple Devices like it did with the IOS11 + GP Legacy app. In fact we're using AD-Authentication on Portal and AD Athentication as well as Certificate Profiles for the gateway. A machine certificate is deployed to the iOS device (also the Enterprise CA Root Cert). The Certificate Profile allows certificates from this CA.
This way was possible up to version 5 and also runs great with our windows machines. Is this a supported way? Do i have to use user certificates? Any experience or guidance?
Thanks,
Jochen
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-04-2018 08:51 AM
this will still work but you will need to re send the certificates to the devices via a profile from the apple configurator, this is explained in earlier posts.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-18-2018 11:50 PM
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-25-2019 04:12 PM
@APatel wrote:The steps from @MarkRosenecker above ended up working for me as well. Initially I skipped the VPN profile steps, but found out that it is needed to make it work. I am now seeing a new issue. I have my PA3020 configured to allow saved passwords, however in the new 5.0 app, its prompt me for a password each time i connect. Anyone else seeing the same behavior?
I am seeing this behavior. It prevents the app from reconnecting once the iPhone is disconnected from the internal network.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-14-2019 06:00 AM
Hello All,
I spent some time with this problem. All of the information here is correct, however there aren't a lot of correct examples of using Apple Configurator to generate a .mobileconfig file to install on iOS if using client certificate authentication. I have found the following guide gets you almost all the way there (Certificates loaded, and vpn profile, but missing the Provider Bundle ID):
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000boSUCAY
IMPORTANT NOTE, THE ABOVE DOCUMENT SEEMS TO BE MISSING THE FOLLOWING KEY CONFIGURATION:
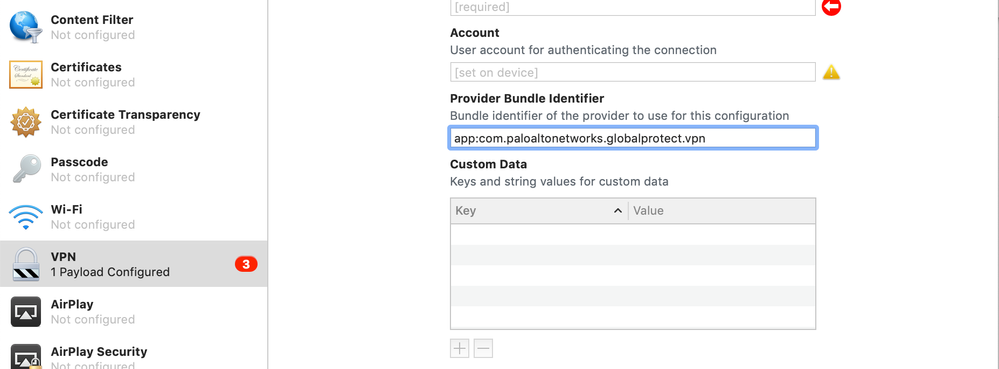
On Apple Configurator, there is a Provider Bundle Identifier that needs to have "app:com.paloaltonetworks.globalprotect.vpn" filled in, otherwise the iOS Global Protect App won't use the profile contents.
Hope this helps.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-03-2019 12:40 PM
Something else I've noticed when setting this up, is that the Provider Bundle ID and the Identifier seem to have to match in order for you to successfully install the profile.
ANOTHER IMPORTANT NOTE IS THAT FOR THE ACCOUNT FIELD IN THE APPLE CONFIGURATOR, THE NAME NEEDS TO MATCH THE COMMON-NAME ON THE CERTIFICATE.
- 28457 Views
- 20 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- SCM GP User Certificate Renewal Process in Strata Cloud Manager
- Slowness in a specific gateway in GlobalProtect Discussions
- We're encountering a GlobalProtect error stating 'Certificate is not within its validity period,' despite this being a newly configured Palo Alto setu in GlobalProtect Discussions
- Could you please tell me about the Embedded Browser Framework Upgrade, an enhancement of GlobalProtect version 6.3? in Prisma Access Discussions
- Global Protect 6.2.X, HIP Match and Fedora 41 in GlobalProtect Discussions