- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
PAN OS 5.0 and AD authentication problem
- LIVEcommunity
- Discussions
- General Topics
- Re: PAN OS 5.0 and AD authentication problem
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-29-2012 04:46 AM
Hello
I have a little problem with my PA-5020. After upgrading OS to a 5.0 version my user authentication to log on as an administrator from ldap and kerberos doesn`t work. I had user mapped to an allowed list by AD group:
cn=administratorzy paloalto,ou=urzĄdzenia,ou=grupy zasobÓw,dc=my,dc=domain,dc=name,
it was working fine with os 4.X but after updating to a 5.0 i got errors:
User 'my.domain.name\myuser' failed authentication. Reason: User is not in allowlist From: x.x.x.x
After adding user directly ("my.domain.name\myuser") to allow list it works perfectly.
At first i thought it was problem with my OU names containing ó,ą which are polish letters, but i moved that group to a different OU without theme and it still doesn`t work.
It looks like PA doesn`t see members of my groups.
Weird thing is that I also have policy based on user belonging to a different groups and that mapping works fine.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-29-2012 05:09 AM
I've had exactly the same problem - I worked through it with Palo support and we discovered we had to put the netbios domain name back in the LDAP query (the one we had to remove in 4.1.8) and then the group name had to be in the format domain\groupname rather than the full LDAP path. I also had spaces in the OU name for the account I was doing the LDAP lookup with and found we had to move this to a OU without a space in.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-29-2012 05:09 AM
I've had exactly the same problem - I worked through it with Palo support and we discovered we had to put the netbios domain name back in the LDAP query (the one we had to remove in 4.1.8) and then the group name had to be in the format domain\groupname rather than the full LDAP path. I also had spaces in the OU name for the account I was doing the LDAP lookup with and found we had to move this to a OU without a space in.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-29-2012 06:26 AM
Thank You it worked but its pretty annoying that i have to change my OU to let PA work properly i hope they will fix it.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-03-2012 07:40 AM
Making OUs with spaces is just asking for trouble 😉
Few CLI commands for debuging user/group mapping:
debug user-id reset group-mapping all
show user ip-user-mapping ip <IP address>
show user user-IDs match-user <user name>
show user group list
show user group name <group name>
General rule is: use NetBIOS style user/group names.
Run into problems myself when using FQDN (groups were retrieved in FQDN-style but not matched to users which were mapped to group in NetBIOS-style).
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-07-2012 07:32 AM
Hi Albert
can you post a picture of your LDAP config from your firewall. I've having some logon issues with pre-logon and I think it might be related.
Thanks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-07-2012 08:00 AM
djrodb - I could not paste a picture, would have to obfuscate it and that would not help you ![]() But I exported the config to xml and edited it:
But I exported the config to xml and edited it:
<ldap>
<entry name="AD-DCs">
<server>
<entry name="AD-PDC">
<port>389</port>
<address>10.10.10.10</address>
</entry>
<entry name="AD-BDC">
<port>389</port>
<address>10.10.10.11</address>
</entry>
</server>
<ldap-type>active-directory</ldap-type>
<timelimit>30</timelimit>
<bind-timelimit>30</bind-timelimit>
<ssl>no</ssl>
<base>DC=imagine,DC=local</base>
<bind-dn>pa500@imagine</bind-dn>
<bind-password>Hashed_Password</bind-password>
<domain>imagine</domain>
<retry-interval>3</retry-interval>
</entry>
</ldap>
That is a working configuration for Active Directory domain imagine.local with Primary and Backup Domain Controllers.
Could you say more about your difficulties? What do you mean by "pre-logon"?
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-10-2012 12:22 AM
Hi Albert
pre-logon is a feature of the GP VPN client. The pre-logon function uses certificates and ldap authentication to lo the user into the laptop before you actually press crt alt del to log on. This allow you to run login scripts and patches on all remote laptops that come in via the VPN.
My problem is the pre-logon feature isn't working 'pre logon' as I get user authentication errors. When I actually log onto the box and log in as normal the GP client logs me onto the network. So it works post-logon but not pre-logon.
My ldap setting match yours so it doesn't seem to be that.
Thanks for your help.
Rod
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-10-2012 01:28 AM
djrodb - Oh, it is a PAN-OS 5.0 feature (just checked it). I currently do not have any box on it in production so can not help you with any experience. However:
1. Have you configured pre-logon according to: https://live.paloaltonetworks.com/docs/DOC-4209 ?
2. Have you tried configuring Kerberos authentication in place of LDAP?
3. What entries are in the log of the Global Protect client on the machine failing authentication?
I think you have problems related to certificates, as you can establish VPN using only LDAP credentials (method you use post-logon).
Please keep me updated on your progress, this feature is interesting.
I will try to implement it in lab if time allows.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-10-2012 01:49 AM
Hi Albert.
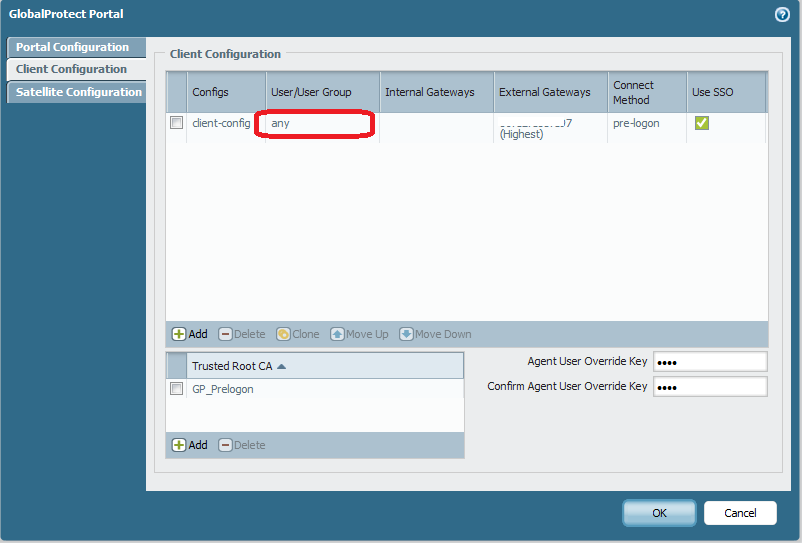
I've finally got this working. The problem was me settings in the GP portal config. I originally selected the LDAP group I'd configured under the user/user group setting in the GP portal client config.
I changed this to any and it resolved the problem. This feature works really good.
Thanks for you help.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-18-2013 12:40 PM
Hi Albert_C,
Could you show an example of how to specify the group you want to list with the command "
show user group name <group name>" ?
thanks
Art
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-23-2013 07:35 AM
ArtBahrs - sorry for the late replay, I was swamped with work.
Easiest is to type: show user group name and press TAB - PAN CLI will show available choices (groups).
You can specify short and long format:
show user group name example\bu-personal
is identical as:
show user group name cn=bu-personal,ou=general,ou=groups,dc=example,dc=org
If group contains spaces (or other unwanted characters) you will have to enclose it in double quotes:
show user group name "cn=domain admins,cn=users,dc=example,dc=org"
show user group name "example\domain admins"
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2013 11:03 AM
Refer to djrodb Dec 10, 2012 1:50 AM
I would like to know logon script working on our GP Pre-logon. We had an issue that logon script is not working if we put group either domain\user group or LADP format cn=network_tech,ou=groups,dc=domain,dc=com but if we put any in source user in security rule and authentication profile it will works. For LADP config. We leave domain name empty which is suggested by Tech. GP user can authenticate without problem and go to network resource and map drive manually but logon scripts is not working. Please share your experience if possiable
Thank you
Daniel
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2013 11:40 AM
daniel.li@tcdsb.org - if I understand you correctly Windows' logon scripts are not working when you put specific user or group in security rule?
Please refer to: https://live.paloaltonetworks.com/docs/DOC-2020 for comprehensive information about configuring GlobalProtect.
Reason why scripts are not working with specific user/group in security rule is:
All pre-logon VPN connection will report a generic “pre-logon user” to User-ID. Username
is not known at the time the connection is established. Username is reported to gateway
once the user logs in to machine.
Taken from GlobalProtect Configuration Tech Note.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2013 12:58 PM
Thanks Albert. There are two places to add user/group (authentication profile and security policy)
If both place are Any. logon script will NOT work in our case. I have not tried one Any one user/Group. Basically we only allow staff to get authenticated not Students. We followed Doc 2020 for setup. Is there fix to get logon script working with pre-logon SSO setting. My understanding for pre-logon with SSO
1. User (not in office network) with pre config wired or wilress internet connection, power up machine without logon window. Pre-logon is already established between user laptop GP client to PA portal
2. user login with AD user and GP starts to connect using AD user (SSO) and then user starts logon corp domain/scripts/drive mapping
Not sure if Palo Alto staff use pre-log feature to get home drive mapped at home. We use Juniper/Cisco and it works well.
- 1 accepted solution
- 14499 Views
- 25 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- macOS and slow download speeds after GP 6.0.10 in GlobalProtect Discussions
- compatibility issue between GP and IOS18.2 in General Topics
- Cortex XDR login issue in Cortex XDR Discussions
- GlobalProtect blocks access to internet when connected in GlobalProtect Discussions
- User VPN Global Protect with MFA as Code or Authenticator App in GlobalProtect Discussions



