- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
- LIVEcommunity
- Discussions
- Cloud Delivered Security Services
- Threat & Vulnerability
- Who Me Too'd this topic
Who Me Too'd this topic
Tcp flood
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-18-2017 08:51 AM
Hi,
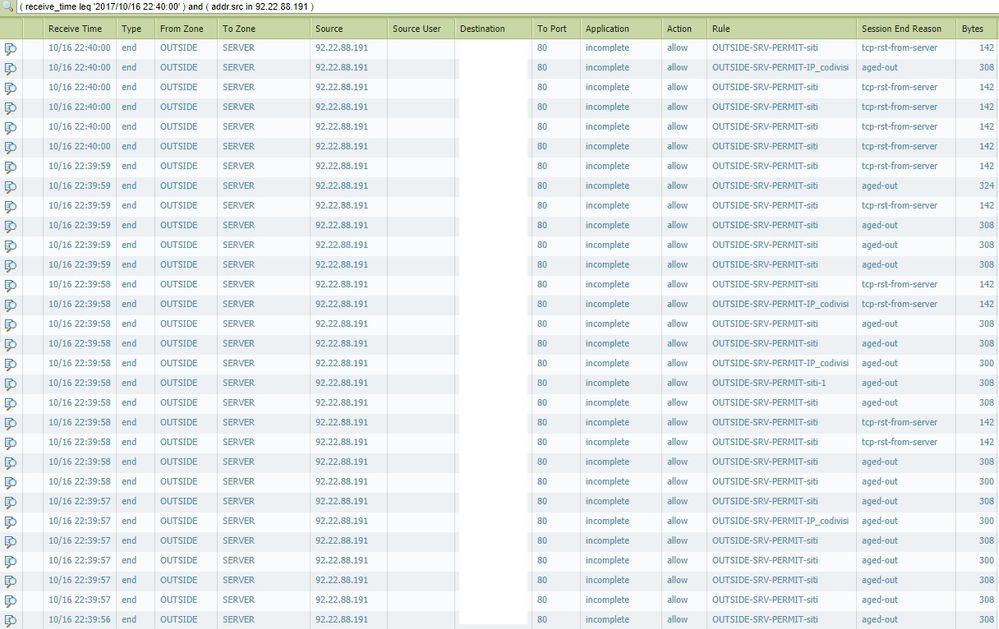
today from 15.10 to 16.10 I received more than 15600 calls from the same IP. The Windows 2012 server already has a function against SYN ATTACK and TCP FLOOD, and I see it on the tcp-rst-from-server log monitor, but they are very small compared to those aged-out. It's been a month since I get continuous attacks and this sends my web application down. These attacks always come from different IPs. Block an IP but then a new one will appear even after days.
Here an example with some hidden fields for privacy.
I need to understand what kind of limit apply to DoS Protection rules. Have I to apply Aggregate or Classified type?
Actually I apply the rule to Aggregate mode with these settings:
SYN FLOOD
Action: SYN Cookies
Alarm Rate 30
Activate Rate 100
Max Rate 1000
Block Duration 300
UDP Flood
Alarm Rate 100
Activate Rate 1000
Max Rate 4000
Block Duration 300
ICMP Flood
Alarm Rate 100
Activate Rate 1000
Max Rate 4000
Block Duration 300
Other IP Flood
Alarm Rate 100
Activate Rate 1000
Max Rate 4000
Block Duration 300
I did not enable Zone Protection on the interface but I created a rule in Policies -> DoS Protection. I did a test by setting the rule in Protect and I find many logs but I'm afraid it's too restrictive and blocking even those who really need to connect to websites.
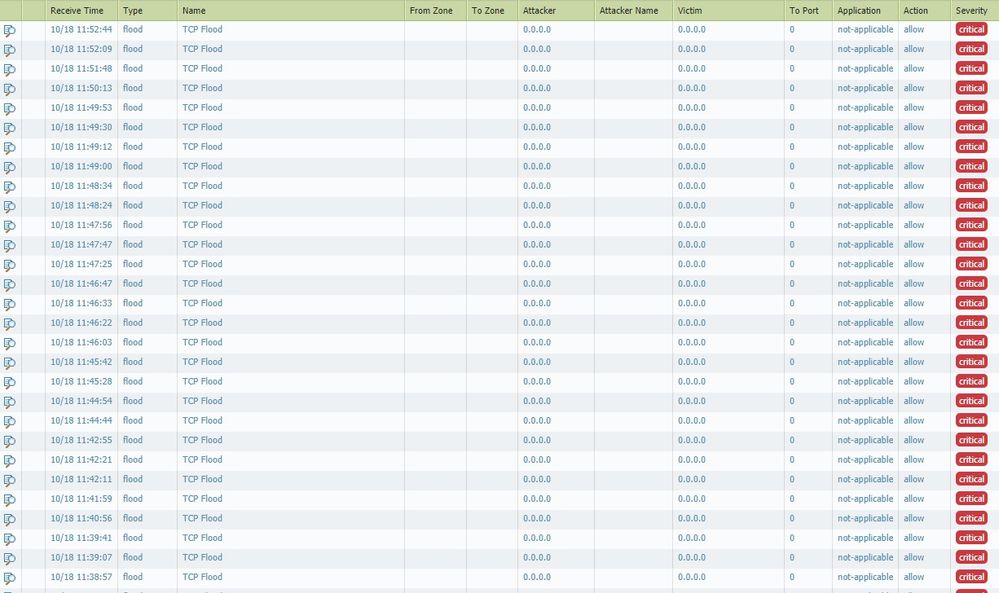
Here the screen
I match one only syncookie-sent and this maybe restarted my application!
Besides, I can not understand what the firewall is blocking because TCP FLOOD makes not visible attacker and victim.
Please help me!