- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
External Dynamic Lists not working
- LIVEcommunity
- Discussions
- General Topics
- External Dynamic Lists not working
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
External Dynamic Lists not working
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2016 08:46 AM
Hi all,
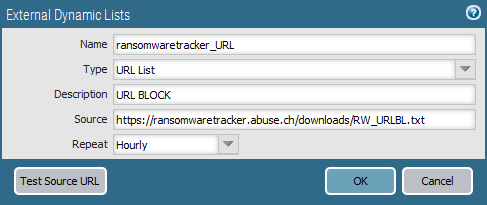
I have configured EDL of type Dynamic URL Lists with the next configuration
Then in URL filtering profile the ransomwaretracker_URL category is configured as BLOCK and the Profile is applied in the Security rule.
It seems configured correctly, I can list the EDL in CLI, but if I try to go to listed URL, it does not blocked.
PAN is working with 7.1.2 version.
Thanks,
Jordi
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2016 08:51 AM - edited 10-17-2016 08:55 AM
Hi Jordi,
Can you remove the 'https://' and try that? The documentation says not to use this prefix.
Can you also check your traffic logs and security policies and see if the allowed traffic is hitting a rule above or below the rule you have configured?
Try this command to see if your EDL has populated ok:
> request system external-list show type url (EDL name)
You can add your list to a URL filtering profile and add that profile to the policy:
hope this helps,
Ben
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2016 09:28 AM
Does it work as expected if you build a Deny rule with your EBL as the source address? This list is also 4992 entries which may be pushing the number of address objects you can push in one EBL. If you have anything less than a 3050, 3060, or a 5020 and up then you aren't going to be able to use this list.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2016 11:38 AM - edited 10-17-2016 12:07 PM
It is a bit away from the original post/question but I recall a discussion here about the limit of entries :
- IP address—The PA-5000 Series and the PA-7000 Series firewalls support a maximum of 150,000 total IP addresses; all other platforms support a maximum of 50,000 total IP addresses. No limits are enforced for the number of IP addresses per list.
- URLs and domain names—a maximum of 50,000 URLs and 50,000 domains are supported on each platform, with no limits enforced on the number of entries per list.
More info here:
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2016 12:01 PM
@TranceforLife I believe those limits only cover 7.1. I've always gone off of what's listed here https://live.paloaltonetworks.com/t5/Learning-Articles/Working-with-External-Block-List-EBL-Formats-... unless people actually point out that they are running 7.1.* since most people seem to be ignoring it for now.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2016 12:11 PM
the user is running 7.1.2 PAN-OS
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2016 01:20 PM - edited 10-17-2016 01:27 PM
l have just tested trying using http, getting redirected to https. If it is listed on firewall through the cli that is fine, should work. Also could run test button to see if you are connected successfully. Should just work. Please follow link posted by BPry:
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-18-2016 05:13 AM
Hi all,
Thanks for your opinions. The device is a PAN 3020 and I think that the list are supported, the number of entries is ok.
I have tried to configure the list without https but continues without block the URLs listed in file.
The test source URL is correct, the list can be oppened.
The traffic do match in rule with the profile applied.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-18-2016 06:06 AM
@COMIP I just tried to run that list on my own 3020 and while the link tests okay it wasn't able to actually pull anything from the list; I would assume because of the formatting. Can you run the command request system external-list show name (name) with the correct name of your list and see if there is actually anything within the list? You could also do a refresh instead of a show and monitor the specific job of the DBL refresh and see if it actually completes.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-18-2016 08:10 AM
The list is opened when the command is executed.
impala@FW_VM401(active)> request system external-list show type url name ransomwaretracker_URL
vsys1/ransomwaretracker_URL:
Next update at : Tue Oct 18 18:00:29 2016
Source : ransomwaretracker.abuse.ch/downloads/RW_URLBL.txt
Referenced : Yes
Valid : Yes
Total valid entries : 4992
Total invalid entries : 8
Valid urls:
http://01ad681.netsolhost.com/7j0jlq3
http://027tzx.com/lscpv
http://0793mobile.com/jetg2
http://108.174.196.88/8dpg3
http://109.73.234.241/dgq01p
http://11011020.web.fc2.com/ets19pre
http://111.86.142.67/~h_fujii/95hdienf
http://121.83.206.211/~ftp-yama/9z6nu
http://125ru.web.fc2.com/09u9jn87
http://12hourenergy.com.au/ty6yhd
http://151.ru/4GBrdf6
http://158.195.68.10/87hcrn33g
http://158.195.68.10/g76gyui
http://158.195.68.10/porirue
http://158.199.158.185/e2ti07
http://178.78.87.8/spyra2
http://178.78.87.8/xjzhm
http://18901350711.com/ll0wdsu
http://18vek.spb.ru/HJghjt872?FqRolfwcFC=ubcMhkMNCX
http://18vek.spb.ru/p3isx
http://194.28.172.166/~triera/95osasmx
http://198.1.95.93/~deveconomytravel/cache/binstr.php
http://1express.com.sg/cpmr1pt
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-18-2016 08:29 AM
@COMIP Do you know if your URL Filtering is working at all?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-18-2016 08:45 AM
Yes, URL Filtering is working.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-18-2016 08:55 AM
@COMIP If URL is working and you have the rules setup for both incoming and outgoing traffic then I think the next step would be a TAC case. I would question how your rules are setup however, as you are going to need both one incoming and one outgoing if you are trying to test it by going to those websites.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-19-2016 02:26 AM
Yes the profiles are applied in both directions.
Thanks for your answers, I'm going to open a case.
- 19932 Views
- 16 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Is there an API to add IPs to Cortex XDR EDL programmatically? in Cortex XDR Discussions
- Is the unified RPC interface (MonitorDirect.enqueueLogRequest) supported for external use? in Next-Generation Firewall Discussions
- EDL Capacity Reached but Lists Show Empty / Default Entry (0.0.0.0/32) – Panorama Multi-VSYS Setup Post: in General Topics
- EDL Scalability & Platform Limits – Best Practices in Next-Generation Firewall Discussions
- What certificate to use for Palo Alto-provided EDL validation in General Topics