- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
how to block Tor browser this like browsers and vpn tools?
- LIVEcommunity
- Discussions
- General Topics
- how to block Tor browser this like browsers and vpn tools?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-30-2017 01:08 AM
Hi !
I have question for you. I use PA-3020 Firewall. how to block Tor browser, opera vpn browser and this like browsers.
I also want to block proxy VPN tools.
Example: express vpn, nord vpn etc.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-30-2017 02:40 AM
Hi @Bahruz
The easiest way to accomplish this if you want to cover a 'type' of application, is to build an application filter for subcategory proxy and encrypted-tunnel
This will cause the 'group' to be autonatically populated with all the applications that have the behavior you selected.

You can then create a security policy to block these applications

here's some more information on how to leverage application filters : What are the recommended applications for internet access?
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-30-2017 04:19 AM
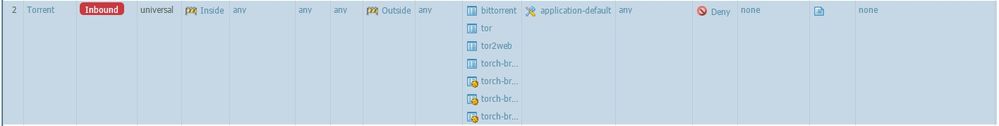
for test i do write this rules but tor is still work
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-30-2017 05:59 AM
did you allow ssl in a different policy and enable ssl decryption ?
this is needed to look inside encrypted ssl sessions and identify some applications
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-30-2017 01:15 PM
If you are not decrypting the traffic then it's likely that the PA just can't identify the traffic. Make sure that you verify what rule the traffic is actually hitting in the security policy rulebase though; it could be that there is a rule above this one that allows the traffic or that the rule that allows the traffic isn't being limited upon application at all.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-30-2017 11:54 PM
no i didnt. how i will do
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2017 01:27 AM
Hi @Bahruz
This article is a good guideline (it has a tutorial video also) to get your SSL decryption set up: How to Configure SSL Decryption
PANgurus - Strata & Prisma Access specialist
- 1 accepted solution
- 8672 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Does Prisma Browser support device-based Conditional Access (device ID / compliance)? in Prisma Access Discussions
- False Positive Report in VirusTotal
- Release notes Prisma Browser in Prisma Access Browser (PAB) Discussions
- Prisma browser extension for Google Chrome does not auto or force sign in in Prisma Access Agent Discussions
- Questions about cookie control in Prisma Browser? in Prisma Access Browser (PAB) Discussions