- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Shared gateway and BGP setup problem ?
- LIVEcommunity
- Discussions
- General Topics
- Shared gateway and BGP setup problem ?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Shared gateway and BGP setup problem ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-15-2015 11:20 PM - edited 09-15-2015 11:28 PM
Hello all,
This is the first time I post to the community. Before posting this message I've read a lot of information and I only can thanks everyone for all the interesting information found here.
We have some difficulties to set up a "working" shared gateway with our Internet connection with BGP. I'm not sure where the problem is from, if it's a BGP setup problem or a limitation of the shared gateway. Perhaps someone can give me the correct information that will help me to understand why it's not working.
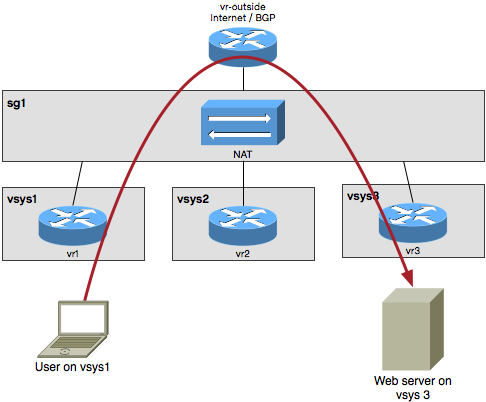
As shown in the figure, we're using three vsys for different entites in our organization. A shared gatway is set up to share the ISP. Each vsys has it own virtual router and I added a fourth virtual router for the BGP (vr-outside). The vr-outside and the shared gateway use the same interface, but nothing it configured on the shared gateway for this interface (I don't know if the SG will work without interface and only by routing).
The NAT rules are installed on the shared gateway and this is where my problem starts. With this setup every thing seems to be working fine. BGP is working, shared gateway and NAT are working and each vsys can reach Internet without difficulties.
The problem is that each vsys has natted servers. These servers are working fine from Internet but not from my different vsys. vsys can't access public address on other vsys and I don't want to add inter-vsys communication using zone. It is not the goal if everything was separated from scratch. I only want that public resources using public IP where available to each vsys without difficulties from Internet/public addressing (if it's possible :-).
On the figure 2 the user has a private IP and the web server has natted public IP. The web server will never be reachable by the user if it's from an internal vsys.
Perhaps the source of the problem can be that the same interfaces are used for the vr-outside and the sg1? Removing the BGP from the PA and putting it to Cisco device will solve my issue? ... an idea how to solve this issue?
All comments are welcome!
- Labels:
-
Configuration
-
Network
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-19-2015 07:00 AM
Our setup is slightly different than your,
- We only have one VR among all the VSYS
- We have a shared gateway 1 (sg1) connected to the Internet, and we have used OSPF, OSPFv3 and BGP in different setup.
- We don't have NAT setup in SG1, my guess is it will be the same
- In virtual systems, all vsys are included in the visible virtual system
- In each vsys, the untrust zone is an external type and sg1 and all vsys are included in the virtual systems.
For example, we have 3 vsys, each has their trust-vsysX zone.
From Internet to trust-vsys1, the security policy in vsys1 will be from untrust to trust-vsys1.
If trust-vsys1 zone needs to reach trust-vsys2 zone. You will need to have security policy in vsys1 trust-vsys1 -> untrust and vsys2 untrust -> vsys2.
Hope this helps,
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-30-2015 05:01 AM
Thanks for the information, but it's not really my question.
- 5021 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- PA-445 lost management access in General Topics
- GlobalProtect 6.1.11-175 Connection Issues in GlobalProtect Discussions
- PA1420 IKE packet disappear between receive (ingress) and firewall session state in General Topics
- Windows Clients – Captive Portal Not Triggering with GlobalProtect Always-On Enabled in General Topics
- Unable to establish tunnel during Service Connection configuration (Details Added with Screenshot) in Prisma Access Discussions