- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
VPN Tunnel between static Palo Alto and dynamic Fortigate
- LIVEcommunity
- Discussions
- General Topics
- VPN Tunnel between static Palo Alto and dynamic Fortigate
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
VPN Tunnel between static Palo Alto and dynamic Fortigate
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-30-2015 01:45 AM
What is the exact settings in order to establish a VPN tunnel between a Palo Alto firewall that has static WAN IP address and a Fortigate that has Dynamic WAN IP address?
If both has static IP address, the tunnel works.
If Fortigate has dynamic WAN address, I cannot get the VPN working. I tried aggressive mode on both sides. Palo Alto log keeps saying IKE phase-1 negotiation failed. Couldn't find configuration for IKE phase-1 request for peer IP X.X.X.X[500], ID ipaddr:X.X.X.X.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-30-2015 06:27 AM
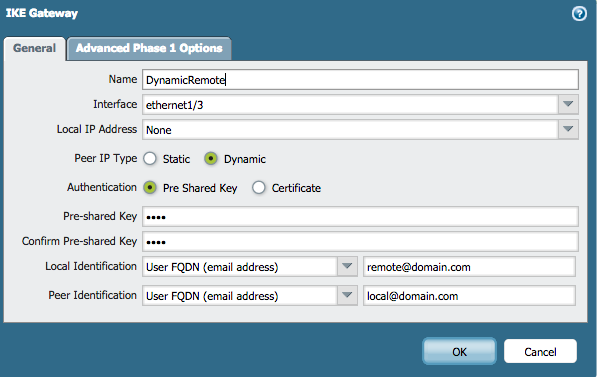
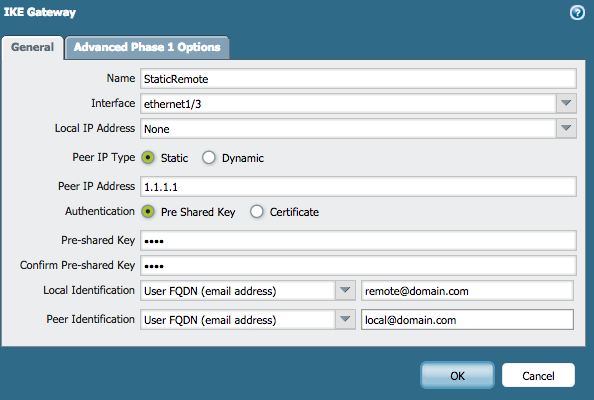
Check your gatway configurations. In addition to selecting aggressive mode on both sides. Your gateways need to be configured to use dynamic on one side and static on the other. And you should have local and peer identity configured. This is used as the alternative to knowing the static ip address to match the IKE phase 1. These are not necessrily real email address just matching strings in the form of email addresses, they need to be the same on both sides as a kind of "password" check.
ACE PanOS 6; ACE PanOS 7; ASE 3.0; PSE 7.0 Foundations & Associate in Platform; Cyber Security; Data Center
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-30-2015 07:35 AM
Ok.. Got the tunnel up. However, traffic is only one way. I already checked my policies on both side, seems to be correct. Plus, these are the same policies that I used for both side static scenario that worked two ways. When I was troubleshooting the static scenario, I had the same issue and fixed it by rebooting the Fortigate and Palo Alto. However, this time reboot did not help.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2015 04:31 AM
What do the logs say about the traffic that is not working?
Also be sure to have a a logging final deny rule so we can see if the traffic is hitting this rule.
ACE PanOS 6; ACE PanOS 7; ASE 3.0; PSE 7.0 Foundations & Associate in Platform; Cyber Security; Data Center
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2015 11:34 PM
It sounds like a routing issue in your case.
Don't think it matters in this case but in such scenarios I always set IKE gateway in passive mode.
- 11273 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Is there an API to add IPs to Cortex XDR EDL programmatically? in Cortex XDR Discussions
- HealthCheckServerConfiguration fails with TypeError on XSOAR Cloud v8.13.0 in Cortex XSOAR Discussions
- EDL Capacity Reached but Lists Show Empty / Default Entry (0.0.0.0/32) – Panorama Multi-VSYS Setup Post: in General Topics
- EDL Scalability & Platform Limits – Best Practices in Next-Generation Firewall Discussions
- [SOLVED] Panorama's SAML-Based Administrator Cannot See Other Administrators And Generate TSFs in Panorama Discussions




