- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
split DNS
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
split DNS
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-23-2020 12:48 AM
Hello
We need to test MS-Teams. hence I did a few tests with split DNS. The published manuals (e.g. https://live.paloaltonetworks.com/t5/general-articles/globalprotect-optimizing-office-365-traffic/ta...) are fine, as long as the VPN gateway is "near". In our case the user is located in South Africa, and the VPN gateway is in northern Europe. The DNS requests are sent to the DNS server in northern Europe, and the reply does not provide the nearest entry-point into the Microsoft backbone.
To fix that issue, I want to send some DNS requests to the users DNS server in his/her home network. Adding "*.skype.com" to Split Tunnel -> Domain and Application -> Exclude Domain and setting App -> Split-Tunnel Option to "Both Network Traffic and DNS" enabled the function. Unfortunately the experienced time for the DNS resolution will become much higher.
"ping www.paloaltonetworks.com" starts immediately
"ping www.skype.com" takes ~12 seconds to start
I guess that GP simply blocks the DNS requests for www.skype.com (wireshark didn't show these DNS requests via the GP tunnel), so the client has to wait for the DNS timeout until it asks the local DNS server.
Is this the expected behavior?
PAN-OS 9.1.7
GP 5.2.4
Windows 10
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-29-2020 09:18 AM
I’m not experiencing this on our vpn.
i dont use split dns but just thought i would take a look as was not aware of this setting before reading your post.
perhaps flushdns may show different results as it could be cached... hence wireshark not seeing much...
all seems a bit odd though as when split dns is disabled and access to local net denied i still get the odd local dns request when browsing... strange...
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-06-2021 12:15 AM
I did a few more tests.
- add a bogus DNS entry (bogus-host.skype.com) to my DNS server (pi-hole)
- verify DNS resolution on the DNS server itself (outside of my GP-controlled notebook)
- apply "ipconfig /flushdns" before every ping request
ipconfig /flushdns & ping www.skype.com & ipconfig /flushdns & ping bogus-host.skype.com & ipconfig /flushdns & ping www.skype.com
- ping www.skype.com --> delay of ~12 seconds until ping starts
- ping bogus-host.skype.com --> ping starts without delay
The same happens with another domain. pinging www.something starts after ~12 seconds, other hosts start without any delay.
The issue is gone once I disable GlobalProtect.
I'll raise a ticket w/ Palo Alto and see if there is an explanation for this.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-06-2021 05:14 AM - edited 01-06-2021 05:35 AM
taken a look at this and am getting same results for skype.com....
I have noticed though that as soon as i ping www.skype.com a DNS request and response is seen immediately in wireshark from my local (WiFi) DNS as expected because *.skype.com is in domain exclude and app is set to traffic and DNS.
However.... I have found a few sites that work OK with this setting.... perhaps it may also work for you.
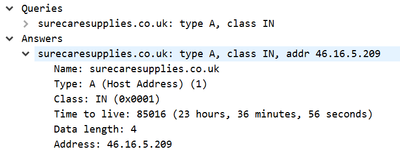
As a test I added *.co.uk to the "split tunnel domain exclude" and then tried both ping and http to surecaresupplies.co.uk and both worked as expected.
It may be caused by the different DNS responses.
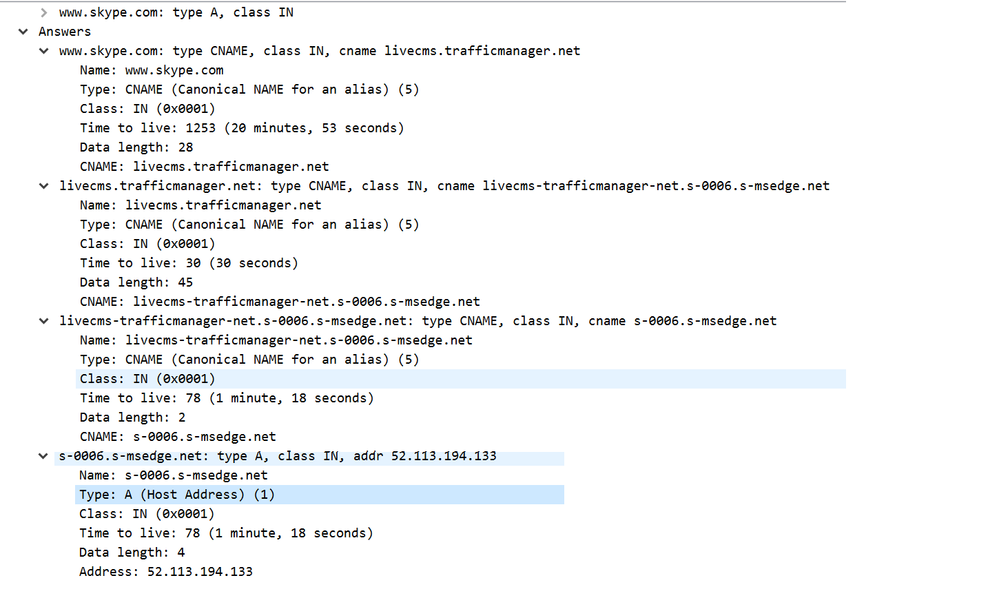
skype returns....
but surcaresupplies returns...
So... the return content of the DNS response may be causing GlobalProtect some issues...
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-15-2021 11:02 PM - edited 01-15-2021 11:06 PM
After upgrading to GP 5.2.5 (guess it's related to GPC-12066) the issue is no longer happening, waiting for confirmation from PA (case is open),
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-16-2021 12:29 AM
Bingo...
GPC-12066 Fixed an issue where, when split tunnel was configured based on the destination domain and Both Network Traffic and DNS was selected, users experienced a delay when accessing the exclusions applied to the DNS traffic and the associated network application traffic for that domain.
- 5819 Views
- 5 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Global Protect Internal Detection in GlobalProtect Discussions
- Get Application Tags via API in Strata Cloud Manager
- SPlit tunneling issue on GlobalProtect in GlobalProtect Discussions
- Azure Virtual Desktops integration with Global Protect nightmare in GlobalProtect Discussions
- GP Split Tunnel in Windows 11 Issue in GlobalProtect Discussions