
Read about the new PAN-OS 9.0 Release Features for GlobalProtect. Learn more about GlobalProtect 5.0, Android UI/UX Overhaul, HIP Redistribution, HIP-Based Identification, Policy Enforcement for Managed and Unmanaged Device Mix, and more.
GlobalProtect 5.0 Android UI/UX Overhaul
This feature is focused on front-end visualization changes and applies to GlobalProtect 5.0 support Android 5.0 and later.
- The new client will provide a more intuitive, user-friendly and pro-active appeal aiming for better user experience and an improved error/warning system.
- The look and feel of the app is updated to reflect the modern trends and the idea is to give a more fluid user-interaction.
- Key features for the overhaul include color scheme improvement, layout and visibility.
HIP Redistribution
- Provides a mechanism to allow GlobalProtect gateways that receive HIP reports to distribute those reports to other gateways.
- The existing mechanism of User-ID redistribution can be leveraged for this feature, allowing admins to deploy HIP redistribution easily.
- Panorama, Log Collectors or Firewalls can all receive and redistribute HIP reports.
HIP-Based Identification & Policy Enforcement for Managed/Unmanaged Device Mix
- Support GlobalProtect Config selection criteria based on:
- Attributes of the machine certificate presented by GlobalProtect client after logging in to the portal.
- Serial number of the device sent by GlobalProtect client during login. The GP portal can query LDAP to check for a matching attribute defined by the admin. If it exists, consider it a managed device.
- plist and registry key sent by the GP client after portal login is complete.
- Gateway HIP Policy Enforcement based on:
- GP client will send machine certificates that match the cert CA and template specified in the GP portal config (HIP report section).
- Enhance HIP object to support match criterion of certificate attributes. HIP reports will be enhanced to show the certificate information as well.
Portal and Gateway Location Visibility for End Users
- Customers with GlobalProtect gateways located in different geographical areas need to put meaningful location-based names of the gateways in the portal configuration, so that the customers know where the gateway they connect to is located.
- When an end user reports issues with latency or with best gateway selection, GlobalProtect administrator wants to know the source region from which the user is connecting.
 GlobalProtect Gateway Visibility
GlobalProtect Gateway Visibility
Additional Resources
GlobalProtect resources on LIVEcommunity: GlobalProtect Discussions, Articles, and Blogs
All the new GlobalProtect features in PAN-OS 9.0: GlobalProtect Features
All the new features in PAN-OS 9.0: What's New in PAN-OS 9.0
Take a closer look at our take on PAN-OS 9.0 features:
PAN-OS 9.0 Release Features: DNS Security and Content Inspection
PAN-OS 9.0 Release Features: Policy Optimizer and App-ID
PAN-OS 9.0 Release Features: Panorama
PAN-OS 9.0 Release Features: User-ID
PAN-OS 9.0 Release Features: Networking and Virtualization
PAN-OS 9.0 Release Features: Management
PAN-OS 9.0 Release Features: PA-7000 New Cards
Then ask a question, join a discussion, or answer someone else's inquiry — that's community!
Not a member of the Live Community yet? It's simple and easy to join. Just sign up with an email address.
Follow us on Twitter.
Check out our YouTube channel and join more than 8,000 other subscribers learning about PAN-OS and more!
Feel free to ask questions in the comments section below!
@kiwi out.

 GlobalProtect Portal
GlobalProtect Portal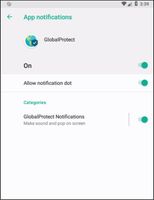 App Notifications
App Notifications


