- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Could use some help with Azure SSO for community edition Cortex XSOAR
- LIVEcommunity
- Discussions
- Security Operations
- Cortex XSOAR Discussions
- Could use some help with Azure SSO for community edition Cortex XSOAR
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Could use some help with Azure SSO for community edition Cortex XSOAR
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-26-2022 01:59 PM
Hello,
I have tried many settings and can't seem to quite figure out what text is to be entered into the setup section within Xsoar for the Azure SAML SSO setup. I keep getting this error:
" {"id":"errSAMLLogin","status":400,"title":"Failed to login via SAML","detail":"Failed to login via SAML","error":"","encrypted":false,"multires":null} "
I have tried many different names and mappings to Azure. Any insight as to what the entry should look like on the Xsoar side would be greatly appreciated.
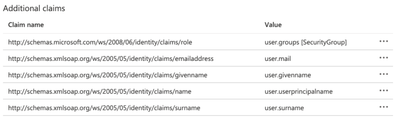
This is what I have currently made my entries in Azure to be, and have used the claim name in Xsoar and am still getting the error.
Thank you,
Richard
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-26-2022 06:36 PM
Hi Richard,
Your claim details don't look right for Azure. They should look like this.
Take a look at this documentation - https://docs.paloaltonetworks.com/cortex/cortex-xsoar/6-6/cortex-xsoar-admin/users-and-roles/authent...
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-27-2022 08:10 AM
Thank you very much for the reply, I have never removed the schema before and have tried it both ways. I have re-added the schema back and still get the same error. I think what I am in need of is what the entry should look like on xsoar side of things. I got the removal of the schema line by looking at the example above in the link that you gave me.
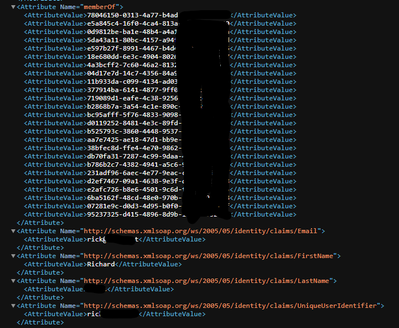
Here is a screen shot of my saml response with the schemas being sent to xsoar:
Any other ideas would be greatly welcomed.
Richard
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-27-2022 09:25 AM
can you share a screenshot of your integration settings as well please
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-27-2022 09:59 AM
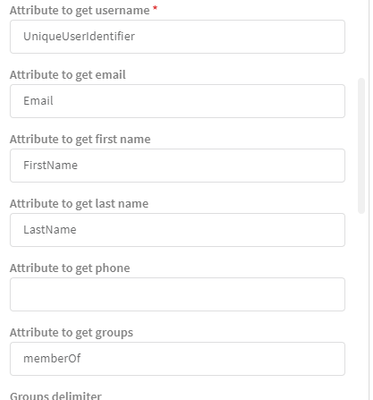
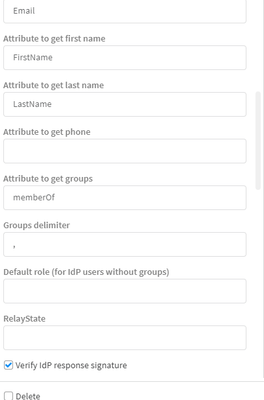
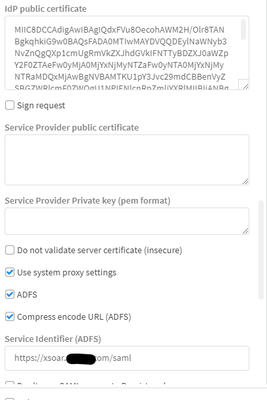
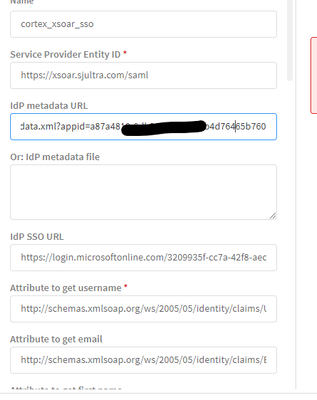
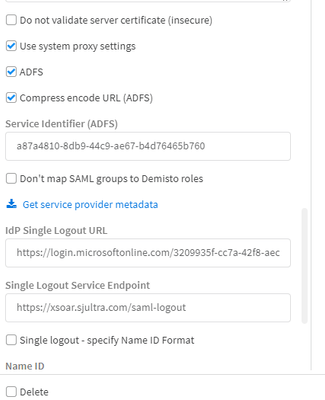
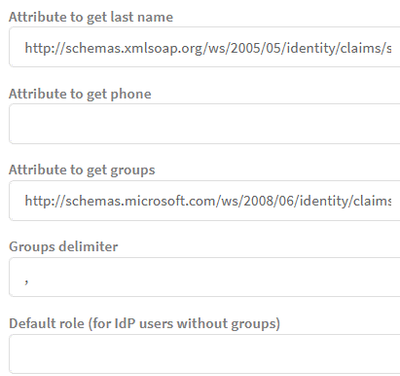
My current settings:
If you want to see all of the settings, please let me know. I can take additional screen shots.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-27-2022 10:22 AM
Thank you again for assisting.
Richard
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-27-2022 10:02 PM
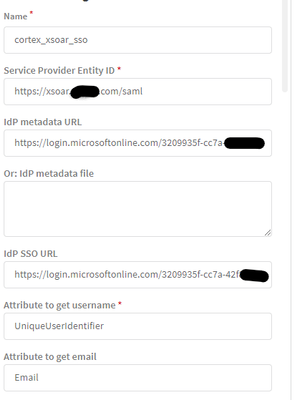
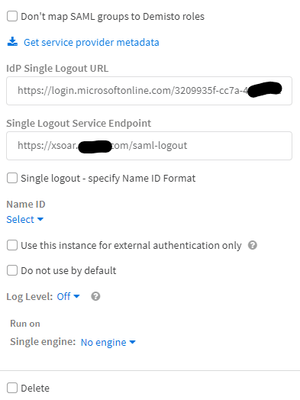
Hi @DriveYourAceOff, it should looks like this.
Also the last option should look like this. According to the documentation -
Let me know if this works for your.
Thanks, Jeremy.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-28-2022 05:43 AM
Is there any way that you can tell me what the fields say at the end of the attributes you used.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-28-2022 01:12 PM
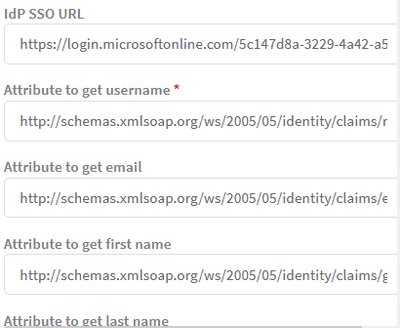
Thanks again, I am still getting the same error however. Here are my new settings, and I believe that they are correct. I am thinking that I may start fresh and try again, but here are my newest settings:
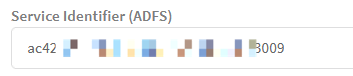
I se the appid section and copied that value to put in below:
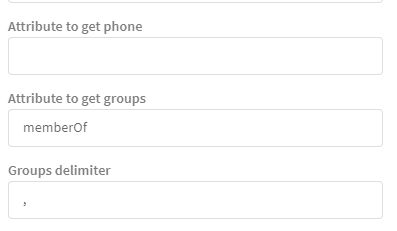
The only field in question is the group field. I feel like that may be wrong as there are several different ways to make the group throughout the instructions. I have used the below method, and it does look like it is getting the correct group from Azure in the saml response xml.
Thanks again for the help!
Richard
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-28-2022 08:35 PM
Hi Richard,
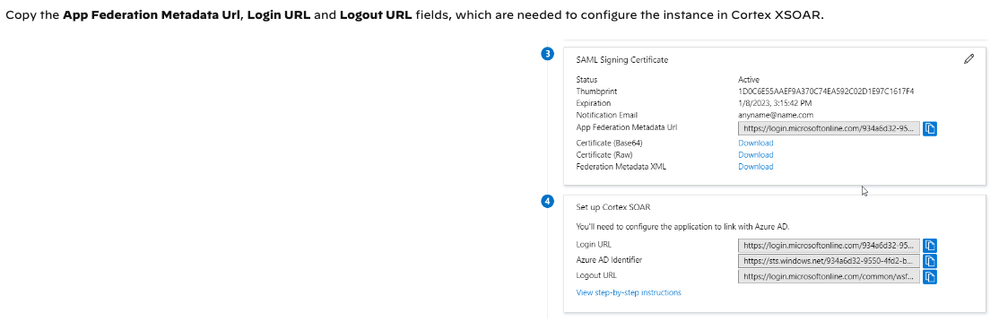
I'm not sure about the iDP Metadata URL. You can copy then from the below
Attribute to get group should be set in a similar way.
Thanks, Jeremy
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-29-2022 12:19 AM
In Cortex XSOAR, go to Settings > Integrations > Credentials and create a new credentials set.In the Username parameter, enter your registered app Application D.In the Password parameter, enter the secret value you created.Copy your tenant ID for the integration configuration usage.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-02-2022 08:03 AM
I updated the group to include the namespace, but am still getting the same error.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-02-2022 08:04 AM
Can you please send me the link to this documentation in xsoar so that I can follow it, this makes sense but I want to make sure that I get the values from the correct places. There is no secret with an Enterprise Application in Azure, so that is where I am getting a little bit lost.
Thanks!
- 11849 Views
- 15 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Is there an API to add IPs to Cortex XDR EDL programmatically? in Cortex XDR Discussions
- Application Fingerprinting in Cortex XDR Discussions
- Es posible bloquear una IP en cortex xdr pro in Cortex XDR Discussions
- USB SCANING in Cortex XDR Discussions
- Cortex XDR Playbooks – Most returning errors, looking for working use cases in Cortex XDR Discussions