- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Signature by hostname
- LIVEcommunity
- Discussions
- Custom Signatures
- Signature by hostname
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-23-2016 12:36 PM
Hello guys,
We recently discover that sometimes, ramdonly, host called "Windows7" trays to mount a shared folder from our fileserver/DC. We discover this because our SIEM correlated some events from de DCserver. Sadly this SIEM do not show us the Source IP Address so, we add a PAN in SPAM port mode to the switch to tray to capture the ms-smb fail logons.
We started by adding the default custome signature and setting up to triggers with 5 events in 120 seconds (just like the SIEM's alert) but that do not work. Now we are traying to make a custome signatere that triggers when any package with the string "jbonaldo" goes through the PAN (jbonaldo is the host name).
I already read the "creating customg signature rev b" and I can not find any reference to SMB2 for the context field, so i try to use the "unknown-req-tcp-payload". I also tray setting up the string in clear text and/or hexadecimal.
BTW, I already create a vulnerability profile and append that to the security rule (just to be clear 🙂 )
what i am doing wrong?
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-23-2016 01:35 PM
Juan:
Thank you for the packet capture.
I can confirm that we currently do not have a context available in the custom signature engine for the SMB hostname. If this is something you'd like to have added, you should reach out to your account team representative and file a feature request for inclusion in a future version.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-23-2016 01:22 PM
Good afternoon.
For requests of this nature, please try to provide a packet capture if it is possible, highlighting the traffic you wish to create a signature on. It will greatly improve our ability to help you.
It sounds like you want to trigger off something specific in SMB traffic, though based on your post above I'm not 100% certain what the actual offending traffic is. Would you mind elaborating slightly?
As far as SMB based signatures go, we currently have one context for SMB, which is "ms-ds-smb-req-share-name" detailed on page 27 of the creating custom signatures document referenced in the sticky of this forum.
Leveraging "unknown-req-tcp-payload" will not function as the traffic you reference will likely be caught by the SMB decoder. This would mean a custom signature is not possible with our current engine. "Unknown-req-tcp-payload" is for applications identified as "unknown-tcp" only, meaning we have no decoder for them.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-23-2016 01:30 PM
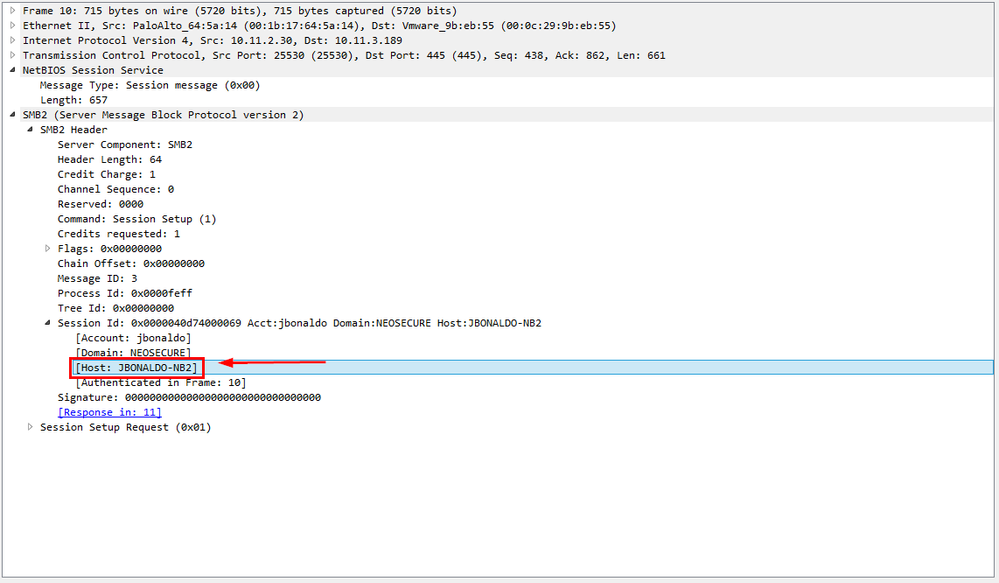
rcole, thanks for your answare. What im actually traying to do is capture in a pcap file every try of ntlm auth from a desktop machine with the hostname "jbonaldo". I attached you a pcap file with the capture and here it is a screenshot of what information im traying use to trigger my custom signature (and than, when the signature triggers capture this fail login).
In the pcap file (row 10) you can see that the hostname is actually in the package sended to the server so, in teory, we can see this information with the palo alto and trigger the custome signature and then, capture the traffic.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-23-2016 01:35 PM
Juan:
Thank you for the packet capture.
I can confirm that we currently do not have a context available in the custom signature engine for the SMB hostname. If this is something you'd like to have added, you should reach out to your account team representative and file a feature request for inclusion in a future version.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-23-2016 01:39 PM
OK, Cole thanks for your help.
BTW, do you know if there is any way to do what i need with the current PANOS?
THanks in advance.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-23-2016 01:43 PM
Juan:
As far as I am aware, no. This is due to the fact that we don't have a context for SMB hostname publicly available to customers to write signatures on, and would require a feature request be filed.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-23-2016 01:46 PM
Ok, Again, thanks for your help.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-23-2016 01:47 PM
Juan:
No problem, sir. Thank you for your patience and for providing the data you did.
- 1 accepted solution
- 10308 Views
- 7 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Username Generalization Playbook in Cortex XSIAM Discussions
- Can I filter on hostnames in an array? in Cortex XDR Discussions
- False Positive Report in VirusTotal
- Rapid7 Insight Agent not showing as vendor in HIP Object Anti-Malware tab despite OPSWAT V4 support in Next-Generation Firewall Discussions
- How to make Router BGP ping into IP inside Palo Alto in Next-Generation Firewall Discussions