- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Cisco ASA VTI not importing ipsec or gateway info
- LIVEcommunity
- Tools
- Expedition
- Expedition Discussions
- Cisco ASA VTI not importing ipsec or gateway info
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Cisco ASA VTI not importing ipsec or gateway info
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-04-2022 09:49 AM
We have a healthy mix of VTI and Crypto Map tunnels on our firewalls and when checking the import, the policy maps are all there as expected (outside of the naming). However the VTIs only show up as tunnel interfaces with no IPSec tunnel or IKE Gateway association.
Does Expedition support migrating VTI ipsec tunnels to the equivalent Palo config? This seems as though it should be pretty straightforward and included since the config is only slightly different between the two.
Am I missing something, is this a known issue, or is this transition simply not supported?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-04-2022 10:44 AM
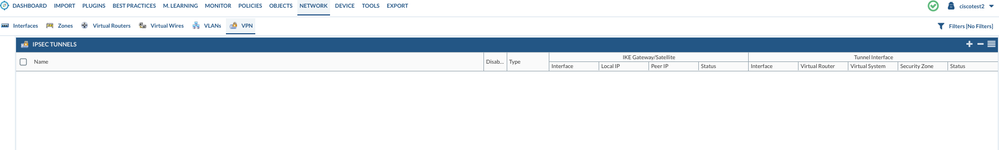
When I look at the imported VPN configs, the only VPN tunnels I see there are the policy map tunnels.
Under Interfaces, I see both the VTI and policy map configs:
tunnel.100 is a VTI interface
tunnel.4 is a policy map interface
the IPsec tunnel for tun.4 exists
but the last configured tunnel is for tun.42, which is also a policy map
So it appears that the tunnel-group and group-policy ASA settings are not being imported for VTIs as they are for the policy maps.
- 2825 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!