- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Authentication Policy Use Case
- LIVEcommunity
- Discussions
- General Topics
- Authentication Policy Use Case
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Authentication Policy Use Case
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-22-2020 08:14 AM
Here use case and wondering if this is feasible.
1. User Bob is already authenticated and connected(tunnel VPN) to firewall A with GlobalProtect with his account "Bob".
2. User Bob need to access critical ressource behind the same firewall A with, however, his privilege account "Bob-Priv".
Problem, its look like the authentication policy is never triggered because user Bob is already authenticated with account "Bob".
Is there a way to achieve this ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-25-2020 06:31 AM
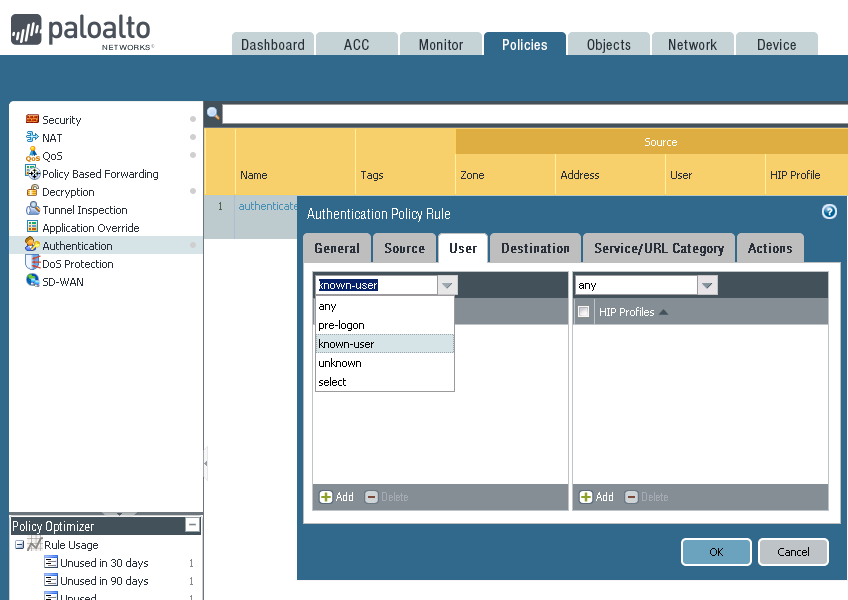
set up an authentication policy for 'known-user' which will trigger a new authentication window only if the user is already known through app-id
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-25-2020 08:45 AM
It's not working.
The user is never triggered with the captive portal auth page. I think, this is because the firewall is already aware of Bob account that came from User ID Agent. However, I want that auth rule is triggered to let user login with his priviledge account.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-25-2020 09:13 AM
Is the rule matching the proper source zone/subnet, destination zone/subnet etc?
Have you tried setting set 'user' field to any?
If that also fails, try 'select' and set 'bob' as the user that needs to authenticate
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-28-2020 06:27 AM
Okay, Captive Portal was not triggered because the destination was HTTPS, and SSL decryption is required for Captive Portal to "redirect" HTTPS traffic.
Also, notice that UserID database is always updated with latest user account logged. That could cause problem in "big" environment where multiple accounts (normal, priviledge ..) are required to touch specific ressources. I think that dedicated firewall(s) or VSYS isolated from the "normal USERID Database" could be a solution to front specific secure environment, like critical database, PCI... etc.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-28-2020 01:49 PM
Hello,
Just allow user Bob and then he must authenticate with Bob-Priv. Unless the resource is does not have an authentication method available?
Regards,
- 5465 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Does Prisma Browser support device-based Conditional Access (device ID / compliance)? in Prisma Access Discussions
- Assign private IP address failed in GlobalProtect Discussions
- Prisma Access Explicit Proxy — Anti‑Spyware behavior when DNS bypasses Prisma (logging subtype + test methodology) in Prisma Access Discussions
- Assistance with LDAP Authentication in General Topics
- Prisma Browser conditional access issue with outlook app in Prisma Access Discussions