- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Extending VLAN through IPSEC + GRE
- LIVEcommunity
- Discussions
- General Topics
- Extending VLAN through IPSEC + GRE
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Extending VLAN through IPSEC + GRE
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-27-2024 08:27 AM - edited 04-27-2024 08:38 AM
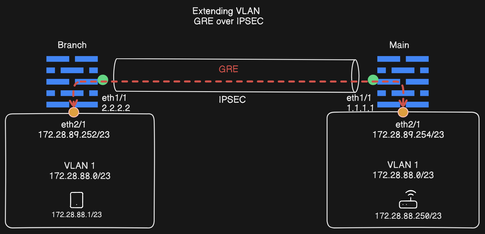
I am trying to extend the VLAN from main site to branch site using a combination of GRE and IPSEC.
Below is a quick representation of the architecture, the objective is to enable remote communications between the main and the branch sites for all devices within VLAN-1.
I am aware that PA does not natively provide L2 tunnels, and VXLAN would be the more appropriate solution for this kind of need, but right now just wondering if this is even possible with only 2 PA firewalls ?
What i've achieved so far is a ping from 172.28.89.252 to 172.28.89.254 and vice-versa, which is a good start, but whenever i try to route towards 172.28.88.250 through the GRE or IPSEC tunnel, i either get a TTL exceeded indicating a loop somewhere, or no response at all.
I'm also exploring other avenues at the same time such as redistributing static routes with OSPF or BGP over IPSEC, but to no avail so far.
Any insight would definitely be greatly appreciated !
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-14-2024 02:39 AM
This is not supported with PA unfortunately.
GRE is limited to L3.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-14-2024 11:49 AM
@O.ELHANCHI wrote:
I am trying to extend the VLAN from main site to branch site using a combination of GRE and IPSEC.
Below is a quick representation of the architecture, the objective is to enable remote communications between the main and the branch sites for all devices within VLAN-1.
I am aware that PA does not natively provide L2 tunnels, and VXLAN would be the more appropriate solution for this kind of need, but right now just wondering if this is even possible with only 2 PA firewalls ?
What i've achieved so far is a ping from 172.28.89.252 to 172.28.89.254 and vice-versa, which is a good start, but whenever i try to route towards 172.28.88.250 through the GRE or IPSEC tunnel, i either get a TTL exceeded indicating a loop somewhere, or no response at all.
I'm also exploring other avenues at the same time such as redistributing static routes with OSPF or BGP over IPSEC, but to no avail so far.
Any insight would definitely be greatly appreciated !
To me this would really be reliant upon the 2 independent networks and how the PA would route to those networks.
The branch fw would have a route that points 172.28.88.0/23 to eth 2/1 and a route for 172.28.88.0/23 to eth1/1 and vice versa at the main location. You will want ECMP on both firewalls as well.
At this point it would be "luck" as to the path the packet took from the firewall.
I don't really think this scenario would functionally work very well, but it could get you what you wanted.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-14-2024 03:14 PM
@Brandon_Wertz wrote:
The branch fw would have a route that points 172.28.88.0/23 to eth 2/1 and a route for 172.28.88.0/23 to eth1/1 and vice versa at the main location. You will want ECMP on both firewalls as well.
Hi and thank you for your contribution to this topic,
I assume from this sentence, that you meant directing 172.28.88.0/23 to eth1/1 on both sides, as branch fw can not directly point to remote eth2/1, except through the tunnel interface which is eth1/1 in this case.
In which case yes, this is something i've already tried of couple weeks ago, i had a static route on each firewall directing subnet 172.28.88.0/23 through the tunnel interface with a metric of 1.
What happened in this case was that i could see the ping reaching all the way from the branch fw to the main fw, to the host natted behind the main fw.
I did a wireshark on 172.28.88.250 and was able to see the echo requests all the way from the branch fw, but no reply. I believe the exact reply packet showed a "No response found", if my memory serves me right.
This seemed to indicate that ARP on main site wasn't capable of going through the tunnel, however what i did not try is setting up ECMP.
Obviously would love to give this solution an other try, as it is from my perspective, the most simple to implement, and while it's for many many reasons not ideal to opt for most scenarios, in this particular use case, the pros outweighs the cons in a pretty substantial manner (geographic proximity < 5km, no duplicate addresses etc., simplicity, L2 traffic)
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-15-2024 08:50 AM
More than likely your experience here:
is because you didn't have ECMP enabled. The setting is in your VR setup:
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-16-2024 06:17 AM - edited 05-16-2024 06:18 AM
Hey @Brandon_Wertz , thank you again, took off some time today to try this out, as I was very curious.
Here are the screenshots if you would still be interested in landing me some more insights :
Below are the results of a ping from branch fw 172.28.89.252 to a natted host behind main fw, 172.28.89.248
Logs from Main FW (172.28.89.254). As you can see the ping arrives well through the tunnel.
And below the wireshark results on the natted host 172.28.89.248, with the infamous no response found icmp packets even with ECMP enabled on both sides quite unfortunately :
For completeness sake here are the related routes left in my VR configuration on Main FW ... technically you can disregard the last 2 routes, they are remainings from previous tests, only the first one really matters in this.
And VR on the branch FW looks like this:
As a side note the packet wouldn't reach branch FW without the last explicit route ... Strange.
Both sites have ECMP enabled on their VR like so :
Any suggestion ? 😇
- 4213 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Palo Alto Site to Site VPN ipsec tunnel up but unable to ping Source to destination in Next-Generation Firewall Discussions
- PAN-308564 Known Issue in Advanced SD-WAN for NGFW Discussions
- GlobalProtect Gateway behind reverse proxy in GlobalProtect Discussions
- IPSEC to Azure establish but cannot use traceroute in General Topics
- Stealth Rule Question in Next-Generation Firewall Discussions