- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Forcing TLS/SSL decryption to cipher suite PAN can decrypt?
- LIVEcommunity
- Discussions
- General Topics
- Forcing TLS/SSL decryption to cipher suite PAN can decrypt?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Forcing TLS/SSL decryption to cipher suite PAN can decrypt?
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-30-2017 10:16 AM
We're on 7.1.x and use SSL decryption on traffic coming in to sites we host.
Is there a way to force the SSL traffic to a (strong) cipher suite(s) that the PAN can decrypt please?
I found this KB but I'm not entirely clear if this lets you mandate only cipher suites that can be decrypted?
https://live.paloaltonetworks.com/t5/Configuration-Articles/PAN-OS-Supported-ciphers/ta-p/71969
Thank you 🙂
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-30-2017 10:51 AM - edited 05-30-2017 10:55 AM
You could use a decryption profile which you have to attach to your decryption rule: https://www.paloaltonetworks.com/documentation/71/pan-os/web-interface-help/objects/objects-decrypti...
But in 7.1.x your very limited with the use of strong ciphers. Beginning with PAN-OS 8 PaloAlto also supports PFS for TLS Inbound inspection: https://www.paloaltonetworks.com/documentation/80/pan-os/newfeaturesguide/decryption-features/perfec...
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-30-2017 10:57 AM
I meant to post this link https://live.paloaltonetworks.com/t5/Featured-Articles/Tips-amp-Tricks-Cipher-suite-enforcement-in-d...
I guess I'm not sure how a decryption profile interacts to force the traffic to something that can be decrypted.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-30-2017 01:04 PM
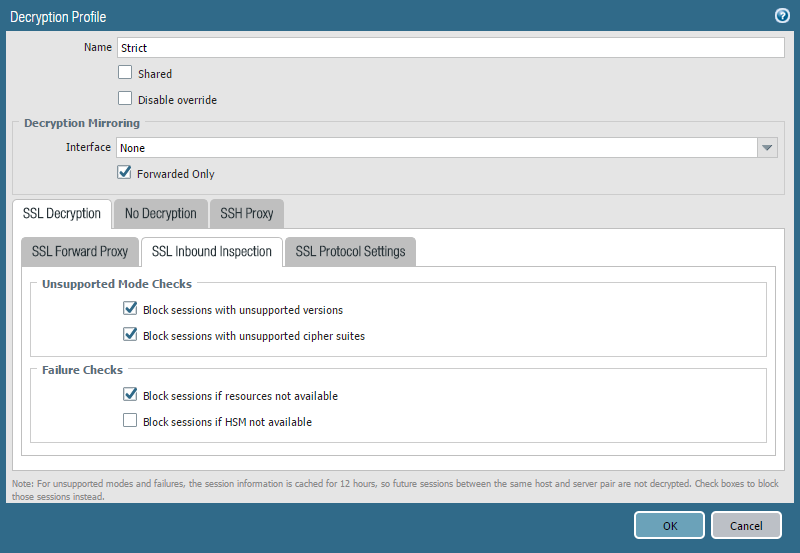
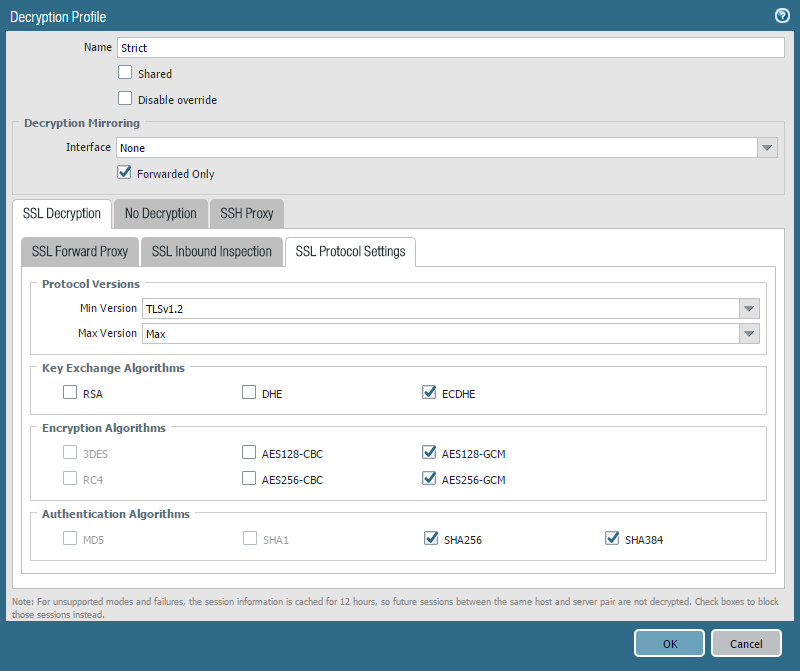
Create a decryption profile with the following settings:
After that you simply attach this profile to your decryption rule and your done. The firewall will only allow ciphers which it is able to decrypt and everything else will be dropped.
(these are screenshots from PAN-OS 8. in PAN-OS 7.1 you HAVE TO SELECT RSA as Key Exchange Algorithm because DHE and ECDHE are not supported for inbound inspection)
- 4465 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- SSL certificate has expired end date after PA decryption in General Topics
- Multi-VSYS 11.2.8 - How to assign a dedicated Forward Trust Certificate per VSYS for SSL Decryption in Next-Generation Firewall Discussions
- Decryption policies and Short-Lived Certificates in Next-Generation Firewall Discussions
- Question about ECH and its effect on URL filtering (without decryption) + how to block it in General Topics
- Unable to block download and upload for chatgpt and messengers in Next-Generation Firewall Discussions