- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Globalprotect check operational system on the portal/gateway without collecting HIP data and using HIP profiles/HIP objects?
- LIVEcommunity
- Discussions
- General Topics
- Globalprotect check operational system on the portal/gateway without collecting HIP data and using HIP profiles/HIP objects?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-14-2021 09:58 AM - edited 05-14-2021 09:59 AM
I found out that you can use the operational system without a HIP object/profile to do things on the Gateway/Portal even if the collection of HIP data is stopped on the Portal.
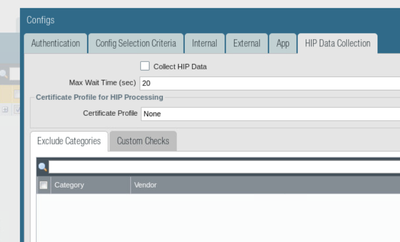
Portal config:
Gateway Config:
Can someone tell me why when I try to check if the operational system is Linux in a HIP object/profile and I attach it to security policy I get blocked? I see that even without HIP checks the Gateway knows the operational system of the client even when Portal HIP data collection is stopped?
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-14-2021 02:32 PM
I think that the gateway knowing what operating system the client using and then using that information to block or allow are 2 different things. The client is clearly announcing to the gateway what it is because of the software being used.
Was this working for you and then stopped?
Stay Secure,
Joe
Don't forget to Like items if a post is helpful to you!
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-17-2021 02:55 PM
Hi @nikoolayy1 ,
I believe you need HIP data collection for HIP checks.
- Data collection will tell the client to generate XML report and submit it to the gateway. It will also tell it what information to add in the report
- Once FW receives the report it will run it agains the configured HIP profiles and check what is matching
- It will then cache/associate that username/soure-ip with all matching HIP profiles.
You can see all matching HIP profiles for given user with:
> show user ip-user-mapping ip <ip-address>
I agree with @jdelio that OS type, that is used as match criteria for gp client config is not data submitted by host, but it is information that FW is detecting by identifying what application is used to connect. If you have noticed the same way you can configure different authentication method based on the client OS. If you think about it, this means that FW needs to know what OS used even before the user has authenticated. In this case it make sense client OS to be determed by HTTP User-Agent or any banner that GlobalProtect application sent when is trying to connect. But this information is not kept and it is not used for HIP check. Information submitted by the client as HIP report is used for that.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-14-2021 02:32 PM
I think that the gateway knowing what operating system the client using and then using that information to block or allow are 2 different things. The client is clearly announcing to the gateway what it is because of the software being used.
Was this working for you and then stopped?
Stay Secure,
Joe
Don't forget to Like items if a post is helpful to you!
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-15-2021 03:14 AM - edited 05-15-2021 03:17 AM
Nothing my idea is that I am testting the general HIP checks as a new design/project but we have stopped the HIP data collection option on the portal and it does not work but as I mentioned outside the HIP checks like making split tunnel just for Linux or Windows or Mac etc. devices on the Gateway seems to work in my lab even without the HIP data collection option being enabled on the portal.
So even without HIP data collection being enabled on the portal the gateway can do some rules based on the workstation OS or domain but not for a HIP object/profile attached under security that checks the operational system. Is this how it works?
For any HIP check do I need to enable the option for HIP data collection on the portal even if it is just the OS that the gateway seems to know even before the HIP checks?
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-17-2021 02:55 PM
Hi @nikoolayy1 ,
I believe you need HIP data collection for HIP checks.
- Data collection will tell the client to generate XML report and submit it to the gateway. It will also tell it what information to add in the report
- Once FW receives the report it will run it agains the configured HIP profiles and check what is matching
- It will then cache/associate that username/soure-ip with all matching HIP profiles.
You can see all matching HIP profiles for given user with:
> show user ip-user-mapping ip <ip-address>
I agree with @jdelio that OS type, that is used as match criteria for gp client config is not data submitted by host, but it is information that FW is detecting by identifying what application is used to connect. If you have noticed the same way you can configure different authentication method based on the client OS. If you think about it, this means that FW needs to know what OS used even before the user has authenticated. In this case it make sense client OS to be determed by HTTP User-Agent or any banner that GlobalProtect application sent when is trying to connect. But this information is not kept and it is not used for HIP check. Information submitted by the client as HIP report is used for that.
- 2 accepted solutions
- 4003 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Issues with Norton 360 in GlobalProtect Discussions
- auth override cookie in Globalprotect in GlobalProtect Discussions
- GlobalProtect, Release Notes, Build Numbers, CVE ?!?! in GlobalProtect Discussions
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- [SOLVED] GPUDATE /FORCE DOESN'T WORK WITH GLOBAL PROTECT in GlobalProtect Discussions