- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
How does DNS Sinkhole actually works?
- LIVEcommunity
- Discussions
- General Topics
- How does DNS Sinkhole actually works?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
How does DNS Sinkhole actually works?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-30-2021 01:20 AM
Hi Everyone,
i need your help to better undestand how DNS Sinkhole actually works.
I mean, i know how it works, how to configure it, but i'm facing a strange behaviour i cannot understand.
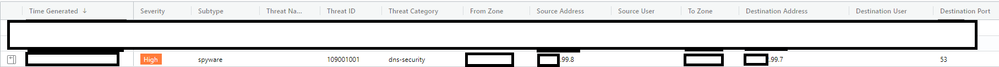
In the photo i have uploaded i have an example.
Both source and destination are in the same subnet (i have obscured the first two octects for privacy)
the destination of the log (99.7) should be the client trying to contact the C2 domain, but the source doesn't exists! It's not the interface IP of PA, nor a host in the subnet!
this is not the only log showing this, there are many of them, and every one have this particularity: the source is always a previous or following IP (for example, if the destination IP is 99.100, i can find sources 99.99 or 99.101, and so on).
Can someone who better knows this function heelp me understand what is happening?
Regards,
Daniele
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-30-2021 04:42 AM - edited 03-30-2021 11:49 AM
So you do not have LDNS server with an IP address as a source as if the clients are not directly connecting to the Palo Alto and using as a DNS proxy it could be a LDNS server https://docs.paloaltonetworks.com/pan-os/9-1/pan-os-admin/threat-prevention/use-dns-queries-to-ident... ?
Usefull things how to check the DNS sinkhole:
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000Clk2CAC
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClmFCAS
Also is the source zone the same as the destination zone as if the IP addresses are in the same network they should be but maybe the source IP address is spoofed (false) or you have some kind of asimetric routing?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-30-2021 10:22 AM
Just a quick reply.. if you want to learn more about DNS Sinkhole.. please check out the Learning Happy Hour that we have on the LIVEcommunity YouTube channel here:
If you liked any of that, please be sure to check out the other Learning Happy Hours here:
https://www.youtube.com/playlist?list=PLD6FJ8WNiIqUCHEz5r8KDmFFtE37PlZT_
Stay Secure,
Joe
Don't forget to Like items if a post is helpful to you!
- 3937 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Crowdstrike Integration to XSIAM in Cortex XSIAM Discussions
- resolve hostname in logs now working in panorama in Panorama Discussions
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- PA-445 setup on Mac in General Topics
- [SOLVED] GPUDATE /FORCE DOESN'T WORK WITH GLOBAL PROTECT in GlobalProtect Discussions