- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
How to...(VPN globalprotect)
- LIVEcommunity
- Discussions
- General Topics
- How to...(VPN globalprotect)
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-13-2019 02:40 AM
Hello guys,
I'm trying to do something and i'm not really sure if it's possible. Let's get into...
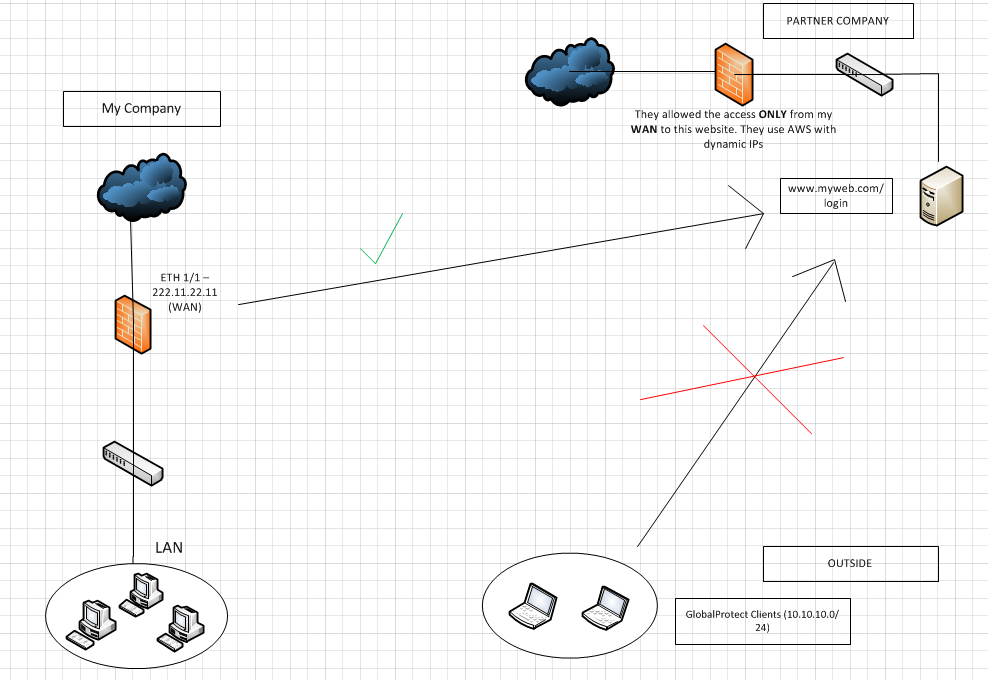
I have an url that is for example: "www.myweb.com". Our partner is hosting that web and with his firewall is just allowing us the access through our IP WAN.
Everything works fine, we can access, but the problem comes when we tried to do it through our VPN (globalprotect). Our clients going through the VPN are not having the same IP WAN so our partner firewall is blocking it and obviously they cannot allow all traffic.
I'm just trying to think in a solution but my mind is blocked. Any suggestions?
Thank you!
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-16-2019 02:48 AM
@PedroPablo: right:
Obviously, your view is different - which PAN-OS are you using? Which GP-Client Version?
Chacko
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-13-2019 03:04 AM
Hi @PedroPablo,
you can define a policy based routing rule to route traffic through another firewall interface for that specific address.
In addition to that, you will need another Hide-NAT rule to use the other public IP for that session.
If the other public IP is not managed by the VPN-Palo Alto, you need to route that traffic (with PBF) to the other gateway.
Best Regards
Chacko
Chacko
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-14-2019 01:27 AM - edited 05-14-2019 02:07 AM
Hi @Chacko42,
I defined a pbf rule to route the traffic for the object "globalprotect clients" to one of my interfaces (the one that my partner allowed in his firewall). Also i defined a nat rule doing the same but when i connect the globalprotect client is not routing the traffic where i want. It routes the traffic through my carrier o wherever i'm connected to.
I don't know if this is what you meant, if not, i think i didn't understand really well you solution.
Thank you for your support though.
Kind Regards
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-14-2019 02:12 AM
@PedroPablo: okay, I don't know your network setup, but maybe you can upload a small network topology with your network, interfaces, ip's and routes - then we can try to help you with the routing issue
Chacko
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-14-2019 03:18 AM
Hi @Chacko42
I made a little quick diagram to help:
So, what i did is:
- I defined a nat rule where the source is the object GlobalProtect Clients ( 10.10.10.0/24) and the source translation (dynamic ip and port) the interface wan ( eth1/1 - 222.11.22.11)
- I also defined a pbf rule where the source is the object GlobalProtect Clients (10.10.10.0/24) and the next hop is the GW of the IP pool where 222.11.22.11 is included.
My problem is that people connected through GlobalProtect client is using the wan that the carrier is giving them so they cannot access to the website i want due to the security rule that my partner company defined only allowing traffic from my interface WAN 222.11.22.11.
I was thinking in the globalprotect configuration, in the split tunnel conf, include the IP of my partner server where the website is hosted but that won't work due to the dynamic Ips.
I've tried to explain myself the best i can sorry if something does not make sense to you.
Kind Regards.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-14-2019 05:59 AM
@PedroPablo: okay, which ip routes do the GP clients receive?
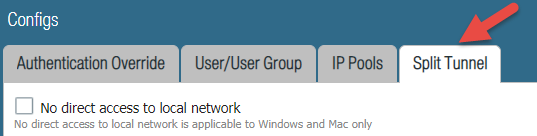
External GW > Agent > Client Settings > Split Tunnel
Chacko
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-16-2019 02:07 AM
I have define some routes of some branch offices that i need my GP clients to access to. I was thinking to define routes to access the servers where the website is hosted at but with dynamic IPs is not gonna work. 😞
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-16-2019 02:09 AM
@PedroPablo: in this case, you can use a domain-based route - just create an entry <target-website-fqdn>:443
Chacko
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-16-2019 02:20 AM
Hi @Chacko42
First of all, thank you for your help.
I tried that before, but i can't include the address object with the target-website-fqdn.
It's like the fw just let me include objects with IP addresses because when i'm going to include the object with the fqnd i can't see it
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-16-2019 02:24 AM
@PedroPablo: in the client-settings where you configure the ip-routes. There is a second tab with domain and application.
There you can say sample.com with port 443 will be routed through the tunnel. that doen't work?
Chacko
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-16-2019 02:41 AM
In the client settings (GP settings?). Where i define the IP routes is here:
I don't follow you, sorry.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-16-2019 02:48 AM
@PedroPablo: right:
Obviously, your view is different - which PAN-OS are you using? Which GP-Client Version?
Chacko
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-16-2019 02:53 AM
Ohh okay, sorry. I was so confused.
PAN-OS: 8.0.12
GP: 4.1.0
I guess i need to upgrade the GP version, don't i? 😕
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-16-2019 04:02 AM
@PedroPablo: okay, that seems to be the issue.
If your environment is fine with it, you can go to 8.1.7 and got that domain-based split-tunnel feature.
GP is the current version 4.1.11/12 - there are a few fixes, that may help you.
Chacko
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-16-2019 04:46 AM
Okay , thank you so much for your help @Chacko42
Then for sure i have to go with a recent version. I'll keep you updated to see if this will solve my problem.
And also for everyone with a similar situation.
Kind Regards.
- 1 accepted solution
- 13506 Views
- 15 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GlobalProtect, Release Notes, Build Numbers, CVE ?!?! in GlobalProtect Discussions
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- [SOLVED] GPUDATE /FORCE DOESN'T WORK WITH GLOBAL PROTECT in GlobalProtect Discussions
- Globalprotect Client 6.2.7 disconnects multiple times in GlobalProtect Discussions
- Global Protect count current users not match statistics in GlobalProtect Discussions