- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Is it possible to enable url redirection in PaloAlto?
- LIVEcommunity
- Discussions
- General Topics
- Is it possible to enable url redirection in PaloAlto?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Is it possible to enable url redirection in PaloAlto?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-30-2014 10:00 PM
Hi All,
Scenario: We have the web server for example.com in trust zone, Any person can access it by anywhere due to destination NAT in firewall with public IP for example.com.
Problem : As we don't have internal DNS server which resolves the example.com, due to this all the request from LAN to example.com is going to internet(public DNS) and coming back to our DMZ, huge traffic.
Is it possible ? : When the request traffic for example.com hits the LAN interface then that traffic should get redirected back to the server hosted internally through the same LAN interface.
Thank you in advance,...
Guru
- Labels:
-
Configuration
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-30-2014 10:51 PM
Hello Guru,
As per my understanding, the Palo Alto Networks firewall cannot be used as a DNS Server. The firewall can, however, point to DNS server as a DNS Proxy.:
Can the Palo Alto Networks Firewall be Configured as a DNS Server?
How to Configure DNS Proxy on a Palo Alto Networks Firewall
How to Configure Caching for the DNS Proxy
The primary problem is, the end user machine will directly send the DNS request to the external server ( not to the PAN firewall).
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-31-2014 06:08 AM
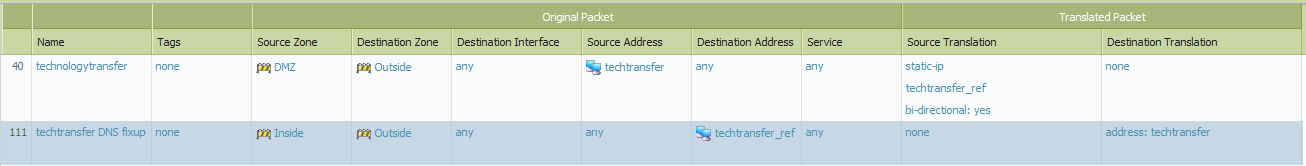
You can add a NAT rule so that the traffic from an internal network to one of your public IP addresses is translated to an internal address.
Name: Example DNS Fixup
Source zone: Inside
Destination zone: Outside
Original packet:
Destination address: (specify the public IP address)
Translated packet:
Destination translation: (specify the internal IP address)
You can specify multiple source zones. And, good management practices would also use address object names rather than bare IP addresses. For us, we also append "_ref" to the names of our public addresses. That provides a quick sanity check on internal versus external addresses.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-31-2014 09:51 AM
With the help of U-turn NAT, actual traffic can be redirected to the internal server: U-Turn , but still DNS query will go to the internet for DNS resolution.

Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-31-2014 01:16 PM
Hello Gururaj,
Just for testing, could you please configure DNS proxy on the PAN firewall and add a static entry for www.example.com.
Ref doc: How to Configure DNS Proxy on a Palo Alto Networks Firewall
Hope this helps.
thanks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-31-2014 02:29 PM
The feature you really want is called DNS doctoring. With DNS doctoring when you configure a nat the firewall with "doctor" the DNS response from internal clients to present your internal ip address instead of the public one. DNS doctoring is not yet a feature on the Palo Alto. Contact your sales team and ask if there is a Feature Request pending you can add a vote for.
In the mean time, if you setup DNS proxy from the link Hulk provided, you can perform the following steps to have your setup act as desired.
1-configure the DNS proxy
2-add static entries (step 5 in the documentation) with the internal address for all your server resources
3-change you DHCP server to present the PA as the DNS server for your LAN
4-update any static computers to use the PA for DNS
ACE PanOS 6; ACE PanOS 7; ASE 3.0; PSE 7.0 Foundations & Associate in Platform; Cyber Security; Data Center
- 11546 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- SSL certificate has expired end date after PA decryption in General Topics
- Redirect URL for Cortex XSOAR integration with DocuSign in Cortex XSOAR Discussions
- Where to begin in General Topics
- Paloalto (PA-440) Firmware upgrade from 10.2.7-h8 to 11.2.10-h3 in General Topics
- EDL MS Intune All URL misses an entry in General Topics




