- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
QoS Methods, Design & Configuration
- LIVEcommunity
- Discussions
- General Topics
- QoS Methods, Design & Configuration
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
QoS Methods, Design & Configuration
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-28-2019 10:39 PM
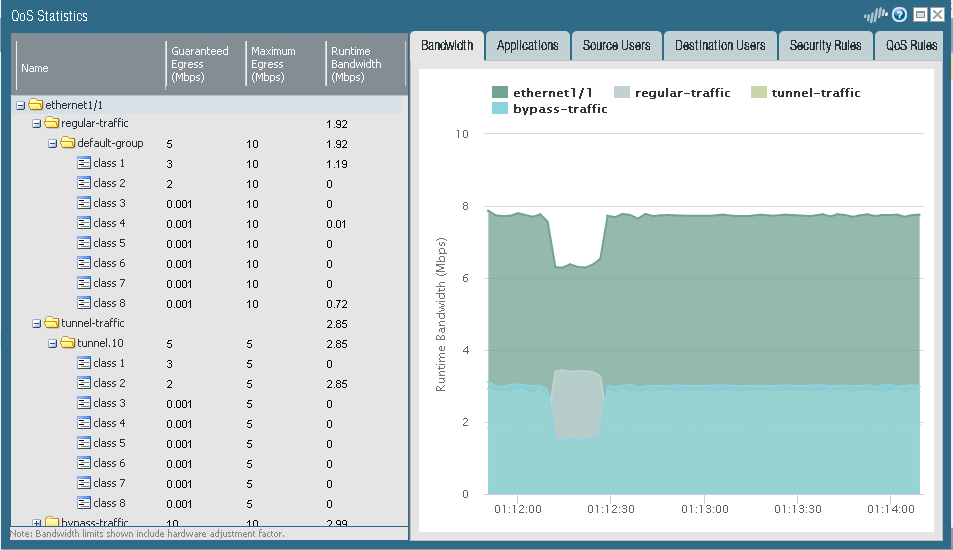
I have a site that only has 5 megs of upload speed and its constantly getting fully utilized. I know I should probably get more bandwidth from the ISP but thats simply not an option right now. Anyway here is my goal. I would like to make the firewall perform strict allocations of gaurenteed bandwidth for 3 different classes I have configured but it is not doing what I have configured it to do. QoS rule 1 should get 3 megs of guarenteed bandwidth (class1), QoS rule 2 should get 2 megs of guarenteed bandwidth (class 2) & QoS rule 3 should get no guarenteed bandwidth (class 8). In addition to this structure I would like all non priority traffic (QoS rule 3/class 😎 to be able to use the full 5 megs of traffic if class 1 & 2 are not currently being used so that all 5 megs are available when higher priority traffic is not egressing the WAN interface. I am using the default QoS profile & have configured the following guarenteed bandwidth amounts into classes 1, 2 & 8...
class 1- 3 megs guarenteed
class 2- 2 megs guarenteed
class 3 to 8- 0 megs guarenteed
In order to configure this structure of QoS I needed to set the interface bandwidth (egress max) to 10 so that I can allocate my desired gaurenteed bandwidth values. There were no errors after configuration & the values do show accordingly in all menu's how ever when I test I notice that the firewall is not strictly enforcing the gaurenteed bandwidth that I have configured for each class. I see that all 3 QoSpolicies are getting hit & in the QoS interface statistics I see the test traffic crossing the right class. Am I missing something? This seems like an easy configuration to make but the palo is just not strictly enforcing the configuration of the QoS profile & policy. See the statistics in the pic...
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-02-2019 02:11 AM
you're allocating 10 mbps of total bandwidth while only 5 is available
the interface limit should be set to 5 and then split up between classes 1,2,8 and ipsec
your ipsec is taking up 2.85 mbit, so the system can already no longer provide more than 2,15 physical mbps while the profile promisses there's 5 more guaranteed for the regular sessions
PANgurus - Strata & Prisma Access specialist
- 2626 Views
- 1 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Active Passive Failover in AWS in VM-Series in the Public Cloud
- Does Prisma Browser support device-based Conditional Access (device ID / compliance)? in Prisma Access Discussions
- SBAC limitations: Delegation of full control (profiles and exceptions) for a specific group of endpoints. in Cortex XDR Discussions
- Regarding the Operational Specifications for HA Mode in Next-Generation Firewall Discussions
- Cannot Access Primary in HA Pair – Need Failover & Recovery Advice" in Next-Generation Firewall Discussions