- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Radius authentication with Clearpass for Firewall Webgui
- LIVEcommunity
- Discussions
- General Topics
- Re: Radius authentication with Clearpass for Firewall Webgui
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Radius authentication with Clearpass for Firewall Webgui
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-04-2021 04:49 AM - edited 09-04-2021 04:52 AM
Followed this KB
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClS6CAK
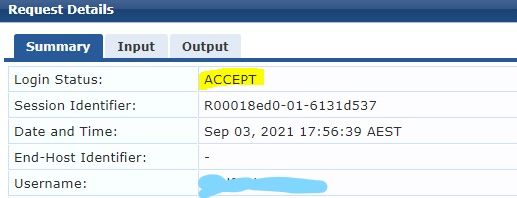
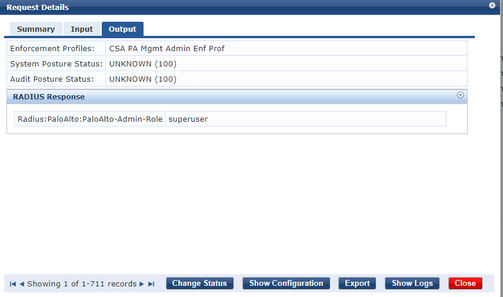
The authentication shows successful on the inbound to Clearpass and meets all the policies required for successful login.
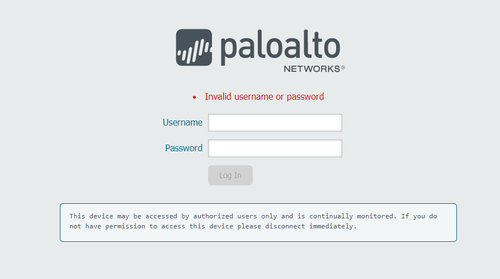
However the Palo sits at the login then eventually fails after about 5-10 seconds and indicates incorrect login credentials.
Palo System logs indicate Authentication failure
failed authentication for user 'test.user'. auth profile 'PALO-CLEARPASS', vsys 'shared', server profile 'PALO-Clearpass', server address '10.x.x.x', auth protocol 'PAP', From: 10.x.x.x.
Auth d logs shows
2021-09-03 17:55:44.886 +1000 debug: pan_authd_radius_create_req_payload(pan_authd_radius.c:230): username: test.user
2021-09-03 17:55:44.886 +1000 debug: pan_make_radius_request_buf(pan_authd_radius_prot.c:390): RADIUS request type: PAP
2021-09-03 17:55:49.886 +1000 debug: auth_svr_timeout_sent_request(pan_auth_svr.c:272): timeout: authd id=6842217317271730159, username=test.user, protocol req id=123, retries=3 (max allowed retries #: 3), elapsed sec=13
(max allowed secs: 180)
2021-09-03 17:55:49.886 +1000 debug: pan_auth_response_process(pan_auth_state_engine.c:4290): auth status: auth timed out
2021-09-03 17:55:49.886 +1000 debug: pan_auth_response_process(pan_auth_state_engine.c:4529): Auth FAILED for user "test.user" thru <"PALO-CLEARPASS", "shared">: remote server 10.x.x.x.x of server profile "PALO-Clearpass" is down, or in retry interval, or request timed out (elapsed time 13 secs, max allowed 180 secs)
2021-09-03 17:55:49.886 +1000 debug: pan_auth_response_process(pan_auth_state_engine.c:4571): Authentication failed: <profile: "PALO-CLEARPASS", vsys: "shared", username "test.user">
2021-09-03 17:55:49.886 +1000 Error: pan_set_admin_user_stat(pan_auth_admin_login_stat.c:260): Admin user "test.user" home dir "/opt/pancfg/home/test.user" has NOT created yet
2021-09-03 17:55:49.886 +1000 Error: pan_auth_send_auth_resp(pan_auth_server.c:646): pan_set_admin_user_stat("test.user", False)
2021-09-03 17:55:49.887 +1000 failed authentication for user 'test.user'. auth profile 'PALO-CLEARPASS', vsys 'shared', server profile 'PALO-Clearpass', server address '10.x.x.x.', auth protocol 'PAP', From: 10.x.x.x.x
What could be causing this issue?
Also another question is
When using RADIUS authentication for management(GUI/SSH) of firewall do you add the administrator test.user manually in administrators of GUI and specify the authentication profile for RADIUS on a per-user basis???
- GUI > Device > Administrators > adding the user there??
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-04-2021 08:10 AM
Your error is still on Last Pass:
Auth FAILED for user "test.user" thru <"PALO-CLEARPASS", "shared">: remote server 10.x.x.x.x of server profile "PALO-Clearpass" is down, or in retry interval, or request timed out (elapsed time 13 secs, max allowed 180 secs)
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-04-2021 06:30 PM - edited 09-06-2021 01:59 PM
@Jatin.Singh To answer your "another question," you have 2 options:
1. Configure the administrator under Device > Administrators and specify the Authentication Profile, in your example - RADIUS.
2. Configure the Authentication Profile under Device > Setup > Management > Authentication Settings if you do not want to create a local account for every administrator. Only RADIUS, TACACS+ and SAML methods are supported. With this method you will need to create an attribute on the authentication server that defines the role of the administrator. You should also restrict the users as well.
- 5229 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GP with saml authentication always redirects to idp in General Topics
- Global Protect Internal Detection in GlobalProtect Discussions
- SAML authentication with cookies won´t work in General Topics
- Assistance with LDAP Authentication in General Topics
- Global Protect Portal / Clientless VPN does not recognize SAML username after update to 10.1.14-h20 in GlobalProtect Discussions