- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Site to Site VPN from PA 200 to Juniper 5GT
- LIVEcommunity
- Discussions
- General Topics
- Site to Site VPN from PA 200 to Juniper 5GT
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Site to Site VPN from PA 200 to Juniper 5GT
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-21-2013 07:10 AM
Hi all,
Anyone have a guide on how to set site to site vpn between PA200 and Juniper 5GT?. I tried a luck but now enable to establish a connection. In Juniper the tunnel i created the status is ready.
A little help please.
thanks,
Jun
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-21-2013 08:51 AM
IPSEC on PAN-OS firewalls is Route Based .
For the ease of config and co-relation , configure Route-Based on the Juniper-5GT (Screen-OS ) firewall.
Proxy-IDs can be left blank (not-configured) at both ends as both Screen-OS and PA firewall in route-based mode use defaults (local 0.0.0.0/0 remote : 0.0.0.0/0 , service any)
Use security level of standard for both for the proposals on 5GT.
Config Guides :
Juniper 5GT- Juniper Networks - [ScreenOS] Juniper Firewall LAN-to-LAN Route Based VPN articles - Knowledge Base
Addtional Ref :
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-21-2013 09:34 PM
Hi Nadir,
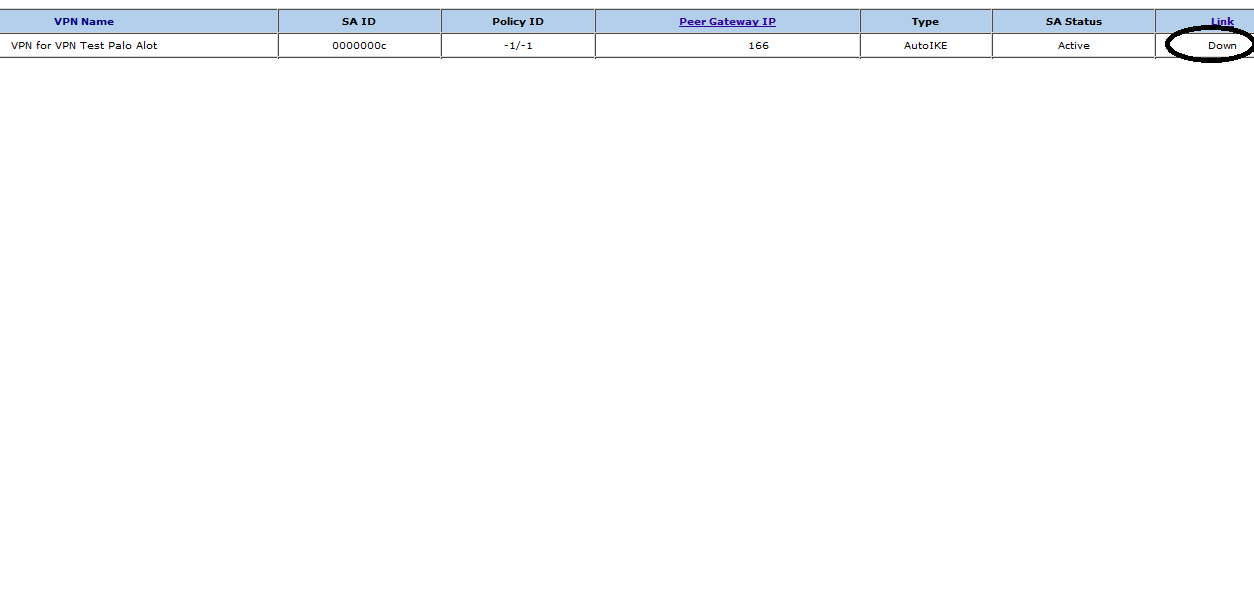
Thank you for help and i managed to up the link between the two sites half-way. Looking on my PA200 side the Ipesec Tunnel are up for both Phase 1 and Phase 2. But on my 5GT Juniper side the link status of the Tunnel is Down but its Active.
I can not ping any internal ip addresses from each from Firewall. But for the public IP addresses for each firewall i am able to reach them thru ping.
I have few attachment and hope it can guide you to give some advices that i miss out. I am not so sure if this is something to do on the PA200 policy.
regards,
Jun
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-22-2013 07:11 AM
On PA-200's end Make sure
1>You have configured a static route with tunnel.2 as an Interface and next-hop = None
2>Security rules (bidirectional if needed) between tunnel-zone and Inside zone.
# decap bytes are incrementing while encap=0 which suggests that PA firewall is receiving traffic for tunnel from Juniper's End but not sending any traffic for the tunnel.
Juniper Link Down -Could be related to Tunnel Monitoring.
Try to allow PING on the Tunnel Interface (PA-200) using Interface-Managment profile .
- 3344 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Existing traffic stops suddenly, and changing of interface MTU resolved it. in General Topics
- PA 445 setup in Next-Generation Firewall Discussions
- Foward Trust Cert and MacBook Pro in General Topics
- Palo Alto Global Protect clients failing to connect intermittently in GlobalProtect Discussions
- site to site VPN between Palo Alto Firewall and Cisco ASA Power fire firewall communication issue in Next-Generation Firewall Discussions




