- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
TLS 1.3 support
- LIVEcommunity
- Discussions
- General Topics
- TLS 1.3 support
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
TLS 1.3 support
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-25-2019 12:13 PM
Hi everybody,
any news regarding change of decryption from passive to proxy mode to support TLS 1.3 decryption?
Thank you,
Jan
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-25-2019 11:40 PM
Hi @Jan_Linhart ,
Is below document addresses your query?
Added to above, As of my knowledge, PA will be doing proxy by default for all connections matching with forward proxy rule,
But inbound inspection is different, it was passive eveasdropping till PanOS 8.0, so if key exchange is DH/ECDH, the decryption fails before 8.0. But after 8.0 they changed the behaviour, so that PA will be active in MITM. if key exchange is RSA, PA wont be proxying the connection, but if key exchange is DH/ECDH, PA will involk the proxy module.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-26-2019 01:05 AM
Hi Abdul,
unfortunately, there is no answer for my question. PAN-OS has support for TLS1.3 now, but not support for decryption.
Please look at this link:
Most important part is:
With TLS 1.3, this passive mode decryption (the one PANW is using - transparent for clients) will no longer be possible since the RSA key exchange has been removed.
Jan
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-26-2019 05:13 AM
Hi @Jan_Linhart ,
PA is doing proxy for DH/ECDH key exchange now also. so if you have a PanOS version supports TLS 1.3, things should work i feel.
Do you have a trustable source which says 'Pan OS wont support decryption for TLS 1.3' ?.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-26-2019 05:24 AM
23.10.2018:
Dear valued Palo Alto Networks customer,
Please take the action recommended below if you have enabled SSL decryption forward proxy. This is required for users to access Gmail and other websites and applications using web browsers that implement strict TLS 1.3 compliance. We have been informed that Google Chrome is planning to implement strict TLS 1.3 compliance in their upcoming version 72. The stable build of Google Chrome version 72 may be available in January 2019, and if your users use a pre-stable build of Google Chrome, they will experience the issue outlined below earlier.
Applies to
All supported PAN-OS releases
Action Required
If you run PAN-OS 8.1:
- Upgrade to PAN-OS 8.1.4 (available now)
Chacko
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-26-2019 05:39 AM
@Abdul_Razaq @Chacko42 I think what @Jan_Linhart is asking is not so much about the ability for PAN-OS to just merely support the protocol, but rather the ability to actually DECRYPT the TLS1.3 session.
I think that it something that is being targeted for PAN-OS 9.1, but who knows if it'll actually make it in the release...
BTW this is another reason I bet Palo came out with the X2XX hardware. I doubt the legacy HW would have been able to handle TLS1.3 decryption.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-26-2019 05:43 AM - edited 02-26-2019 05:44 AM
@Abdul_Razaq wrote:Hi @Jan_Linhart ,
Do you have a trustable source which says 'Pan OS wont support decryption for TLS 1.3' ?.
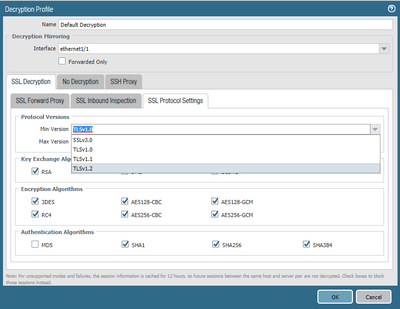
Yeah PAN-OS software itself.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-26-2019 07:30 AM
So it's important to note here the difference between supporting the protocol and actively being able to decrypt TLS 1.3.
- Palo Alto has now added support for TLS1.3 and has made the required changes so that the firewall will no-longer attempt to decrypt TLS 1.3 traffic, which was causing issues for customers with decryption enabled running PAN-OS versions prior to 8.0.14 in the 8.0 code branch or 8.1.4 in the 8.1 code branch.
- Palo Alto can't actually decrypt TLS1.3 traffic just yet and as @Brandon_Wertz mentioned it's something being targeted for a future update. Whether or not it actually makes it into 9.1 or not we'll have to wait and see.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-26-2019 12:14 PM
Hi guys,
as you wrote before - I'm aware of protocol support, but I was asking about plans for decryption support. It is not going to be easy at all and PANW will have to completely change decryption concept from "passive" to real proxy.
Jan
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-08-2019 07:02 AM
ok, so did this one ever get answered?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-09-2019 09:03 AM - edited 07-09-2019 09:08 AM
@BPry-Thank you for the quick reponse. I didn't completely understand the fact that palo was supporting but not decrypting on this as of yet. I think it was mentioned in this post, but I'm guessing most are eagerly awaiting hearing how this will work in the future, being transparent/explicit, or however it will work/if it will work...
From a pure security perspective, do you forsee more and more dependence on the endpoint logging and detection, and less and less from the firewall perspective moving forwared? Without decryption, it seems like the ACC would be a block of SSL and dns.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-09-2019 09:22 AM
I'm running under the assumption that there will be a break in time in which we need to follow current guidance and disable TLS1.3 on endpoints to ensure it only utilizes something that can be decrypted.
From a pure fundamental standpoint decrypting TLS1.3 doesn't actually change, it's still very possible. The ability to passively decrypt the connection with a private key however does. PAN just needs to make some adjustments to the way they are decrypting traffic and this will function from a firewall level perfectly fine. This is already targeted for a public release in 9.1 (that could get pushed back), so until the time comes that you can install whatever release TLS1.3 decryption is enabled in, simply force your clients to fall back to 1.2.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-12-2019 01:36 AM - edited 08-12-2019 02:24 AM
@kiwi Can you post a statement to the current TLS 1.3 decryption situation?
Chacko
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-12-2019 08:08 AM
@Chacko42 wrote:@kiwi Can you post a statement to the current TLS 1.3 decryption situation?
Nothing has changed.
Support of decrypting TLS versions will only come in the release of new PAN-OS versions other than patch updates (so X.X). It wasn't supported on 8.0.X, it's not supported on 8.1.X nor is it supported on 9.0.X. The community is currently waiting on a public release as to if it'll be support in 9.1.X or if even somtime in a future release.
- 23966 Views
- 14 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Request to locate account or transfer asset for S/N 023209008637 in Custom Signatures
- Paloalto (PA-440) Firmware upgrade from 10.2.7-h8 to 11.2.10-h3 in General Topics
- PA-1420 Support in GlobalProtect Discussions
- Active Passive Failover in AWS in VM-Series in the Public Cloud
- [FIREWALL] - Commit Issue in Next-Generation Firewall Discussions