- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Upgrade to 7.1.0
- LIVEcommunity
- Discussions
- General Topics
- Re: Upgrade to 7.1.0
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Upgrade to 7.1.0
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-05-2016 06:25 AM
I upgraded our lab palo to 7.1.0 last night. Has anyone else upgraded anything in their enviornment yet? I don't plan on doing anything in our production enviornment until at least 7.1.1 or 7.1.2.
Not really having much time yet I don't have much to say other than I'm looking forward greater awareness from things like the SaaS reports as well as the extra 10 or 12 cipher suites that are supported in 7.1.0 over prior versions.
Gotta say though I'm not digging the new look/feel of the GUI. The sharp lines/edges make the view feel "old."
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2016 03:05 PM
don't even install 7.1 on your panorama unless you want your configuration wiped by panorama templates when committing...
yay for bugs
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2016 06:23 PM
Upgraded to 7.1 friday night to test over the weekend and ran into multiple problems with rule processing and URL filtering. sites being blocked that should be allowed. sessions failing to be recognized and blocking on final rule.
We are reverting. 😞
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-09-2016 09:12 PM
PAN-OS 7.1.0 has a change in default behavior with respect to security policy processing. Check out the release notes and see if this might be what you experienced:
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-11-2016 05:41 AM
We upgraded to 7.1 in test and ran into a number of issues with Linux IPsec clients (and some mobile clients not using GlobalProtect app) being unable to negotiate with the VPN and not establishing connection.
While there are some nice feature additions, this was pretty show-stopping and we probably won't go any further until a cause is identified (we're still testing various configurations to determine if anything about our setup was causing the issue.)
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-11-2016 01:47 PM
Also ran into the Linux IPSec clients issue.
Error on the linux clients is showing:
configuration response rejected: (ISAKMP_N_ATTRIBUTES_NOT_SUPPORTED)
Hopefully a resolution is in the works.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-11-2016 02:27 PM
Rollback or upgrade to?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-11-2016 04:09 PM - edited 04-11-2016 04:09 PM
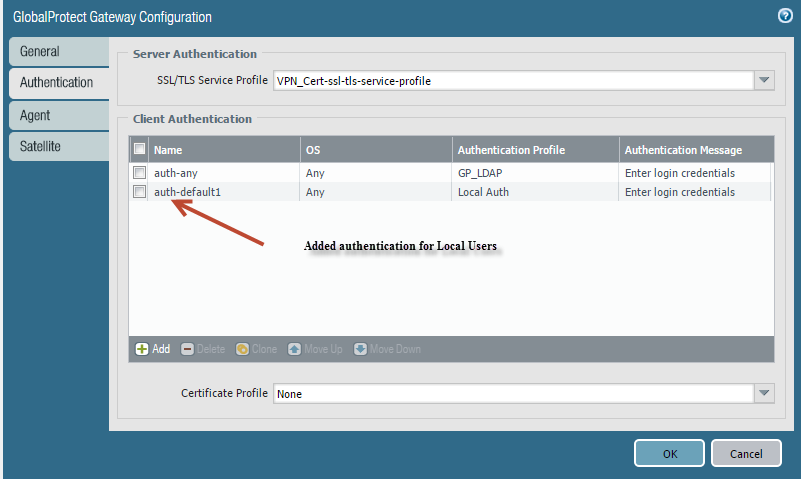
I got around the Linux Clients not connecting with VPNC but it is only working for Local Users.
I had to create a new Client Authentication object and used Local Auth as the Authentication Profile.
Now I can connect from Linux VPNC using those credentials.
Still playing with getting LDAP users authenticated with Linux clients.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-12-2016 05:55 AM
rollback frome 7 to 6.1.10
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-12-2016 06:00 AM
@Brandon_Wertz Yessssir! haha 🙂
I'm agree with you I don't like this "style" .. Looks like a very OLD style.
😧
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-12-2016 06:46 AM
I 100% agree with the style. I tested it on our test system and it is beyond ugly. It's like going from WIndows 7 to 3.1.1 for Workgroups... I don't like the color choices, the sharp edges... bleh... I reverted back just because the UI is an eyesore. Maybe I'll give it a serious try after a few updates but for now I don't want to look at it in our test environment.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-12-2016 07:04 AM
@rmonvon helped me resolve an issue we were having with decryption. Due to the changes in how the any -> application-default is now treated, sometimes the App-ID for web-browsing is seen on port 443 within the encrypted stream. On recommendation, I had to create a special rule for allowing outbound web traffic for the App-ID web-browsing so that it included both service-http (80) and service-https (443) so that websites would work correctly. I'm unsure if there are other apps that could potentially get wrapped in SSL (say VPN, RDP, etc.) that could be affected due to this change.
Just a heads up on this one.
-Matt
- 14082 Views
- 26 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- DHCP vulnerability error false postive content version 9104-10068 in General Topics
- Has anyone upgraded to 11.1.10h25 or h26? in Next-Generation Firewall Discussions
- Paloalto (PA-440) Firmware upgrade from 10.2.7-h8 to 11.2.10-h3 in General Topics
- Upgrade PANOS and SDWAN Plugin in Prisma SD-WAN Discussions
- HA failover on Acitve Passive concerns in Next-Generation Firewall Discussions