- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
vulnerability id 31327
- LIVEcommunity
- Discussions
- General Topics
- vulnerability id 31327
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
vulnerability id 31327
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-22-2016 07:19 AM
Hello,
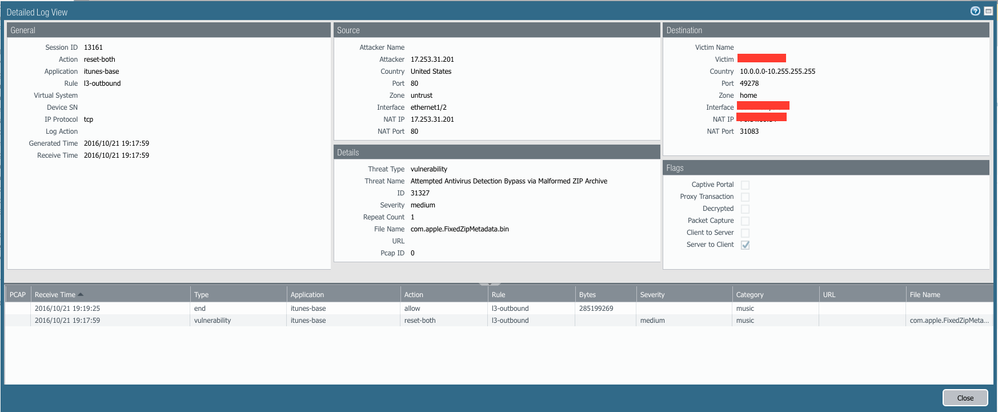
Start 10/13, I have been getting medium threat alert for vulnerability id 31327 (Attempted Antivirus Detection Bypass via Malformed ZIP Archive). I beleve it is my iOS devices connect to apple store to download app updates. Anyone else sees these? It is using the action is reset-both, but I still able to complete the download and install without any problem.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-22-2016 08:19 AM
I have the same problem. I ended up making a "permit itunes-base" security policy that points to a vulnerability protection profile with that specific signature disabled.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-22-2016 04:46 PM
@jvalentine Thanks for confirming it. The strange part that I don't understand is the app update is still successful. Also, the file that is alerting are all from Apple Itune app store. I will think " I can trust Apple?!?". I just want to know if this is a false positive or something real.
E
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-22-2016 06:46 PM
I'm willing to bet it's a false-positive, because it's Apple, right? I'd recommend opening a case with TAC.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-14-2016 05:44 PM
Reply from TAC
We have released the modification to signature (TID: 31327/ Attempted Antivirus Detection Bypass via Malformed ZIP Archive) in content version 646 on 12/13/2016.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-14-2016 09:32 PM
My firewall installed that content version yesterday, but today I'm still getting false-positive hits for 31327 via itunes-base. I count 15 hits just today. Looks like the signature needs some additional work still.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-15-2016 08:01 AM
Same here, TAC told me to use CLI to reinstall the 646 update again. If it still does not work, perform another packet captures and update the case. I don't understand why TAC can't test it? It is just iOS / Itune download app update from apple itune store. It is easy to replicate.
E
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-30-2016 11:03 AM
The signature is disabed on 650-3771. According to TAC, there are too many false positive. Not sure what is the future plan of this specific signature will be.
E
- 4335 Views
- 7 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Prisma Cloud defender agent unable to identify Red Hat back ported patches causing false positives in General Topics
- DHCP vulnerability error false postive content version 9104-10068 in General Topics
- CVE-2026-0261 PAN-OS_ Authenticated Admin Command Injection Vulnerability in Next-Generation Firewall Discussions
- I have a question CVE-2026-0256 PAN-OS in VM-Series in the Public Cloud
- without overwhelming in Advanced Threat Prevention Discussions