- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Vulnerability wrong action Palo
- LIVEcommunity
- Discussions
- General Topics
- Re: Vulnerability wrong action Palo
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Vulnerability wrong action Palo
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-14-2021 04:19 AM
Hi,
We are having a weird issue in Palo. We have a FTP server and we can not access because Palo detects this vulnerability:
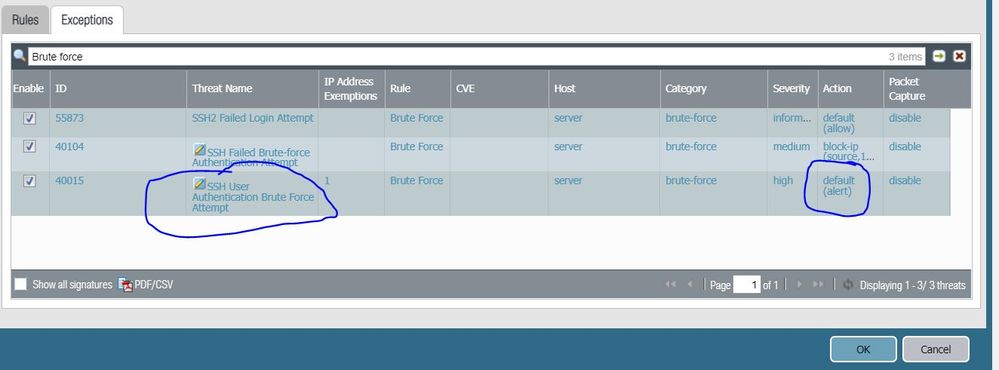
Name: SSH User Authentication Brute Force Attempt
Unique Threat ID: 40015
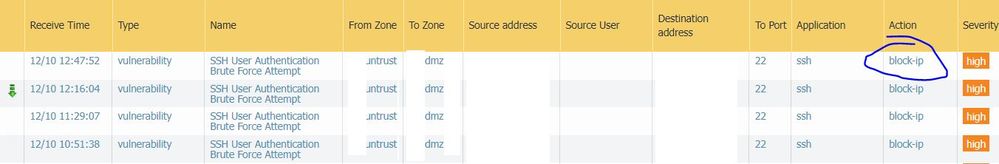
The Palo action is "alert" for this vulnerability but its being blocked "block-ip". I attach the screenshots:
why Palo is detecting a normal access as a vulnerability?
why Palo is not permitting this traffic if the action is alert?
any idea?
thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-14-2021 06:07 AM
Hi @BigPalo , below are my opinions on your questions -
why Palo is detecting a normal access as a vulnerability?
A- Palo Alto triggers this signature when there are multiple requests in specified time from same source to same destination. e.g. 20 attempts in 1 min then it will consider it as brute force. In this case the signature is triggered and actions set against it will be followed.
why Palo is not permitting this traffic if the action is alert?
A- I would ask you to verify the profile where you are looking the action against the profile mapped on the security policy. It may be the case that you are looking at wrong profile.
Check out my YouTube channel - https://www.youtube.com/@NetworkTalks
- 2497 Views
- 1 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- How to Patch Vulnerability - Plugin 43160 (CGI Generic SQL Injection) on GlobalProtect in Next-Generation Firewall Discussions
- Policy destination field when using URL filtering in Next-Generation Firewall Discussions
- Global Protect brute force config. in GlobalProtect Discussions
- How to trigger a "Response page" on Palo Alto NGFWs using URL filtering & Decryption in Next-Generation Firewall Discussions
- Brute Force Attack protection on GlobalProtect Portal Page isn't getting triggered in GlobalProtect Discussions