- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
What services are used by the Management port?
- LIVEcommunity
- Discussions
- General Topics
- What services are used by the Management port?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
What services are used by the Management port?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-16-2017 08:03 AM
We have been tasked to follow the CIS benchmark for our Palo Alto firewalls. One item is to limit access to specific IP addresses for the Management port. That is easy enough if the only thing using the management port was users connecting to manage the firewall itself. My question is what other services use the management port (Panorama, User-ID agents on other servers, HA configurations, external monitoring systems, automation)?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-16-2017 12:11 PM
Hello,
Of the list you proved, they all use the management port, HA to a lesser extent on the larger models. May be this will help[ answer your questions?
Panorama, User-ID agents on other servers, HA configurations, external monitoring systems, automation
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-16-2017 12:32 PM
Hi @kjsocher
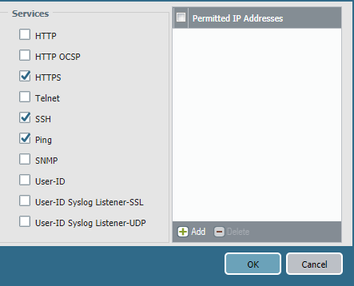
The management port supports the following services by default: HTTP, HTTP OCSP, HTTPS, Telnet, SSH, Ping, SNMP, User-ID, User-ID Syslog Listener SSL, and User-ID Syslog Listener-UDP.
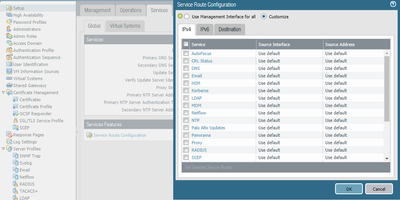
Additional services using the management port by default can be checked by going to: Setup --> Services --> Service Route Configuration
Note that if you have services that you do not want to go through the management port, you can always change it and set it to go through one of your data ports; however, bear in mind that by doing so, that traffic is now going through the data plane instead of the management plane; hence, if that service is critical for your environment and there is a unilateral failure of the data plane that service will no longer be available. Finally, if you decide to put that traffic over the data plane, now you will have to enforce it via specific security rules.
More details can be found at: https://www.paloaltonetworks.com/documentation/60/pan-os/pan-os/getting-started/set-up-management-ac...
I hope this helps.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-16-2017 12:46 PM
Hi @kjsocher
When you limit the access on the managemdnt port to specific ip addresses, it really depends on what services you have activated (ssh, https, snmp, ...). But for tje ip addresses you have to configure you only need to specify rhe ones which connect TO the mgmt ip address --> the access list only applies to incoming traffic. Outgoing traffic will still be allowed to dst's which you do not specify. (Panorama connection is also outgoing)
Hope this helps.
Regards,
Remo
- 3433 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Es posible bloquear una IP en cortex xdr pro in Cortex XDR Discussions
- Continuous Threat Logs Showing Management Server IP as Source in Next-Generation Firewall Discussions
- Panorama Very Slow on VMware ESXI in Panorama Discussions
- Avaya ports Blocking in General Topics
- Palo Alto FW manage by SCM - problem with HA in Strata Cloud Manager