- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
EDL and Custom URL
- LIVEcommunity
- Discussions
- Network Security
- Next-Generation Firewall Discussions
- EDL and Custom URL
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
EDL and Custom URL
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-29-2022 12:59 PM
Hi There,
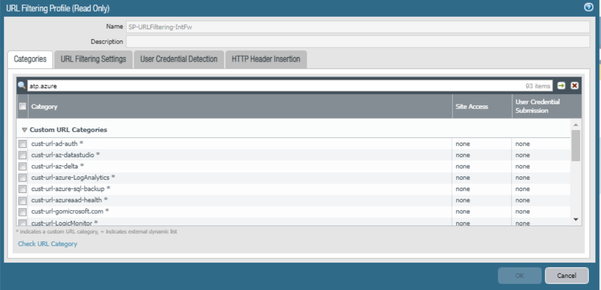
Problem Statement : We have custom URL lists(To allow Azure Endpoints only), also we have EDL(With Minemeld) integrated.
As per our Infosec Policy we should not use Minemeld feed for Microsoft as it has some of many wildcard. So desperately creating custom URL for each MSFT end points(viz Defender, AAD heath etc,,)
But some of URL is not working. I couldn't fetch the exact URL which is getting blocked(its default implementation PAN that, unlisted URLs will not show in URL filtering tab...? but in the Traffic Tab I am seeing very peculiar;
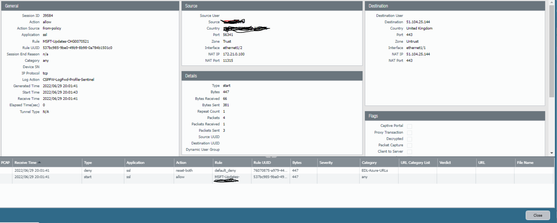
For example: As per below screen shot, Why session is starting the Rule which i configured and fall back to Deny (reset-both with "default deny") category showing EDL-Azure-URL(In fact we have not configured "EDL-Azure-URLs" in the policy.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-30-2022 01:57 AM - edited 06-30-2022 01:59 AM
Hi @Ramakrishnan ,
For the policies if traffic log at session START is enabled, there are chances that the logs will show matching incorrect policy. This is because, when request reaches the firewall interface, the first matching policy in the set will be matched to allow traffic and create session but still at backend, firewall is checking for matching the security profile configurations. So the logs at session END will show the correct rules once all the checks are done by the firewall. Kindly refer this article for more details.
Coming to your 2nd query that you are not able to see logs under URL filtering tabs. To view the logs, you need to make sure that URL category action is set to alert to log the URL filtering logs.
Hope it helps!
Check out my YouTube channel - https://www.youtube.com/@NetworkTalks
- 2428 Views
- 1 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- [SOLVED] GPUDATE /FORCE DOESN'T WORK WITH GLOBAL PROTECT in GlobalProtect Discussions
- Restrict access via GlobalProtect to permit access to only a specific Google Drive Account/Folder in GlobalProtect Discussions
- [SOLVED] Panorama's SAML-Based Administrator Cannot See Other Administrators And Generate TSFs in Panorama Discussions
- Panorama PDF summary report of 1 week/month in Panorama Discussions
- CUSTOMER ADVISORY: Required Action for Azure hosted VM-Series & AIRS Instances in VM-Series in the Public Cloud