- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
unknown ikev2 peer - PA1420 running PAN-OS 11.0.1-h1
- LIVEcommunity
- Discussions
- Network Security
- Next-Generation Firewall Discussions
- unknown ikev2 peer - PA1420 running PAN-OS 11.0.1-h1
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-01-2023 05:55 AM
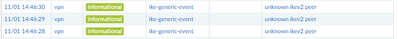
So, i have this type of errors in my logs and i really dont know how to tackle them.
No other info, like for example who is the peer that generates this event, like i used to get on an older PA device also running an older PANOS version
Any ideas?
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-01-2023 10:33 AM
You will get rid of noise coming from internet by permitting incoming VPN only from your peer IPs.
To figure out what IP is trying to connect you need to look into ikemgr.log log by using commands below
less mp-log ikemgr.log
tail follow yes mp-log ikemgr.log (updates log output in real time)
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-01-2023 10:33 AM
You will get rid of noise coming from internet by permitting incoming VPN only from your peer IPs.
To figure out what IP is trying to connect you need to look into ikemgr.log log by using commands below
less mp-log ikemgr.log
tail follow yes mp-log ikemgr.log (updates log output in real time)
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-02-2023 02:54 AM
Thanks, that did it (not doing much ike troubleshooting so i forgot about that log)
Still, i wished PanOS to display that info in the system monitor logs
Anyway, you said this:
"You will get rid of noise coming from internet by permitting incoming VPN only from your peer IPs"
How? i did not set an explicit rule to allow incoming vpn - i assumed the firewall did that behind the scene
Or do you mean to setup an explicit deny all incoming ike rule, with exception for an address group containing all my ike-gateways-ip-addresses?
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-02-2023 05:23 AM
You can add security policy
Source zone - WAN
Destination zone - WAN
Source IP - Your and your peer IPs that terminate IPSec
Destination IP - Your and your peer IPs that terminate IPSec
Application - ipsec
And at the end of the ruleset "block any" rule.
IPSec works because of "intrazone-default" rule permitting same zone traffic.
Be careful when you add "block any" rule because you might have other traffic relying on this intrazone-default rule.
Palo Alto Networks certified from 2011
- 1 accepted solution
- 8785 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Regarding the migration from HDD to SSD for PA-VM running in the Azure environment in VM-Series in the Public Cloud
- Palo Windows ARP Issue - Windows Hosts Not Installing ARP info in Next-Generation Firewall Discussions
- Telemetry shows success in cli but failed in GUI. in Next-Generation Firewall Discussions
- HA failover on Acitve Passive concerns in Next-Generation Firewall Discussions
- Palo Alto 3410 Firewall 100% DP CPU spike in Next-Generation Firewall Discussions