- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Access Domains and context switching
- LIVEcommunity
- Discussions
- Network Security
- Panorama Discussions
- Access Domains and context switching
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-19-2022 03:09 PM - edited 12-19-2022 03:09 PM
HI All,
I have configured access domains to control read only access to certain device groups, but the context switching is not working, I have configured a Admin Role locally, added the user to the local device with an admin role, even added the username as the device and vsys role to see if that would work, the log output from #tail follow yes mp-log authd.log shows that the user logs in and that role cannot be found for the user,
The odd thing is that for one of the device groups this works, the others are configured identically but do not.
Any help greatly appreciated.
Quick edit, this is version 10.1.6
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-22-2022 01:27 AM
Hi All,
After a call with TAC it has been discovered that this is in fact another bug in 10.1, fixed in 10.1.7 and above and tracked under
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-19-2022 04:05 PM
Do you get any error message when you try to switch context?
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-20-2022 01:30 AM
Hi
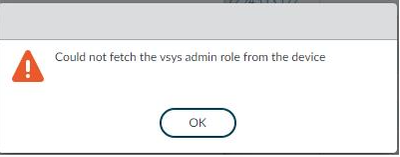
The error that we are getting is
The firewall in question has no VSYS configured and is not in multi VSYS mode, the error does change if there is no role configured on the firewall at all to, predictably, No role for user, there is no difference in configuration between the one that works and the ones that do not, I have also made sure that the contexts are all enabled in the access domain config.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-20-2022 01:38 AM
You created admin role under "Panorama > Admin Roles" and assigned to user but did not create role with matching name under "Device > Admin Roles" in firewall config?
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-20-2022 01:56 AM
The other way around, so the role for admin users was created on Panorama, this was applied to the users as well as the access domain, the role that was defined in that admin role for context switch does exist with the same name on the firewalls we are context switching to.
Does the admin role that is defined for the users on panorama by defined in the context switch and then be present on the firewall as well ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-20-2022 02:04 AM
Create role under "Panorama > Admin Roles" for Panorama and under "Device > Admin Roles" for firewall and try then.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-20-2022 02:34 AM
Hi
That hasn't solved it unfortunately, I have still got the Vsys error, this isn't a bug 10.1.6 is it ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-20-2022 06:01 AM
Do you mind to share screenshot of settings at "Panorama > Admin Roles" and "Device > Admin Roles"?
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-20-2022 06:21 AM - edited 12-20-2022 06:22 AM
Unfortunately I would have to redact it so much that it wouldn't be much use, just a quick question, when you say device > admin roles are you referring to the device templates stored on Panorama or locally on the firewall ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-22-2022 01:27 AM
Hi All,
After a call with TAC it has been discovered that this is in fact another bug in 10.1, fixed in 10.1.7 and above and tracked under
- 1 accepted solution
- 6891 Views
- 9 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GlobalProtect Cert+SAML in GlobalProtect Discussions
- Panorama read only with read only context switching via SAML? in Panorama Discussions
- Streamlined NGFW Alerts and Incidents Management in Strata Cloud Manager in AIOps for NGFW Discussions
- Windows Subsystem for Linux 1 Cannot connect to local gpd service. in GlobalProtect Discussions
- error: azure marketplace vm-series do not bootstrap in VM-Series in the Public Cloud