- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Network Interface not pushed from Panorama
- LIVEcommunity
- Discussions
- Network Security
- Panorama Discussions
- Network Interface not pushed from Panorama
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-07-2018 05:43 PM
Hello,
We need to add an extra IP Range to route out one of the existing sub interfaces on the Palo Alto firewall.
The change has been committed and pushed in Panorama but is not showing on the firewall.
Both using version 8.1.3
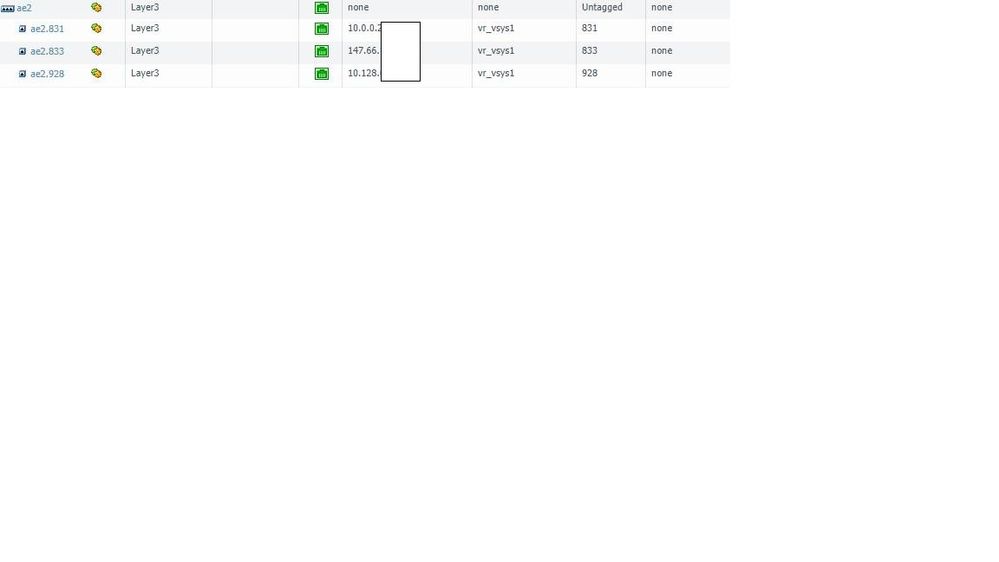
Firewall network interface:
Panorama network interface with the change circle in red:
How do we push this change to the firewall or do we have to replicate the change on the firewalls?
Any documentation on this?
Thanks in advance!
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-09-2018 02:47 AM
The green/yellow gear symbols behind the interface on your firewall screenshot indicates that you have an override active on the firewall. This means that the interface is configured locally and overwrites the config pushed from panorama.
You can disable the override on the firewall itself - there is an option to revert in the task line below the interfaces.
Furthermore you can force template values from panorama - but this will affect all overrides!
In both cases be very careful and check that the template configuration on panorama matches the local configuration of ther firewall - or you will run into trouble!
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-07-2018 06:04 PM
If the commit and push had finished completely are you positive you made the change to the right template?
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-08-2018 05:02 AM
I would check that it committed successfully. I remember when I first started using panorama I thought since I did not get an error that it committed and pushed correctly even though if you go in and check it my have failed for some reason.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-09-2018 02:47 AM
The green/yellow gear symbols behind the interface on your firewall screenshot indicates that you have an override active on the firewall. This means that the interface is configured locally and overwrites the config pushed from panorama.
You can disable the override on the firewall itself - there is an option to revert in the task line below the interfaces.
Furthermore you can force template values from panorama - but this will affect all overrides!
In both cases be very careful and check that the template configuration on panorama matches the local configuration of ther firewall - or you will run into trouble!
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-09-2018 07:24 AM
when you say
force template values from panorama - but this will affect all overrides!
does you mean this will override any local config on firewall to new values pushed from the panorama?
Help the community: Like helpful comments and mark solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-09-2018 08:08 AM
yes this is the case, any part of local configuration that also exists in the panorama template will be overwritten.
Local configuration parts that do not exist in the template will remain unchanged, they do not get deleted.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-21-2021 06:21 PM
...And if none of the above suggestions is your fix, and it's more like you have AE interfaces with subinterfaces, currently overriding Panorama-pushed, and then you are ready to revert those to Panorama-pushed, you may very well end up with an error similar to above... *The undocumented solution is, after verifying that your Panorama version of the interface configs (and corresponding VRs and zones) is correct, to manually delete (via CLI on firewall) the subinterfaces and then the corresponding AE, and then Panorama-pushed will show appear with all green cogs.
- 1 accepted solution
- 11748 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- [SOLVED] Panorama's SAML-Based Administrator Cannot See Other Administrators And Generate TSFs in Panorama Discussions
- How to make Router BGP ping into IP inside Palo Alto in Next-Generation Firewall Discussions
- I have concern in SDWAN, Kindly help out this. in Advanced SD-WAN for NGFW Discussions
- How does the Azure Virtual Network discovers that there is Palo Alto Gateway Interface in VM-Series in the Public Cloud
- Question on "default" VLAN Interface in Next-Generation Firewall Discussions