- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Application Incomplete - Leading causes?
- LIVEcommunity
- Discussions
- General Topics
- Re: Application Incomplete - Leading causes?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Application Incomplete - Leading causes?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2013 01:38 PM
So im doing work on our DR site. Two diff setup scenarios are failing; NAT over a VPN and routing from one PA to another and out a VPN. I can see the rule letting the packets out so a session should start for the return trip but .. nothing.
Both scenarios show Application incomplete; what are the leading causes of this? Incomplete handshake? So maybe the other side never returns an ack on the tcp handshake? Return routing does not work?
Any inout would be appreciated as im running out of options.
thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2013 01:44 PM
You should take packet capture by filter both source and destinaion ip address.This will make sure you to see if there is a drop or no return.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2013 01:49 PM
ok, thanks, ill try that
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2013 04:35 PM
You can find the definition for incomplete here: https://live.paloaltonetworks.com/docs/DOC-1549
As for the traffic, you can also look at the sessions to see if there are any packets from server to client. You can view this data from GUI through Monitor -> Traffic logs -> Click on the magnifying glass and look for packets sent and packets received. From cli you can do: show session all filter <interesting traffic> and show session id <id>. You can also look at the global counters to see if there are any drops.
You can alos refer to these documents for troubleshooting using counters & captures:
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-27-2013 09:40 PM
Incomplete denotes a lack of a tcp handshake. Syn packets allowed but never getting a syn-ack from the destination device. Perform client pcaps and span port on switch to help determine where those syn-acks are going if in fact the server is sending them.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-30-2013 02:29 AM
You mention DR site. Are you facing asynchronous routing ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-30-2013 11:41 AM
so i did a pcap.
seems the 'drop' log has a bunch of packets in it (outbound to server). So i guess they are being dropped on the way out on the initial connection attempt?
the transmit log is empty so i guess my packets are not even leaving the Firewall
however, if i test the fw rule from the command line everything seems fine (action allow).
test security-policy-match from ZONE source <My IP> to ZONE destination <Remote IP> protocol 6 destination-port 23
also, the rule as it stands right now is very loose.
@zarnia: Ill try looking at session data next,
@gafrol: I dont think there is a routing issue. The client LAN hooks up to the PA, then out through the IPSec VPN on the PA, so there not much room for different routes if any at all.
LAN -> PA/NAT -> IPSec VPN -> Remote Side
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-30-2013 12:35 PM
We're dropping packets? If you're good with flow basic, you can get granular information on why we're dropping? If not, please call into PAN Support as any debugging not done properly can impact services on or through the PAN device.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-30-2013 01:09 PM
Here are some good tips on debugging packet drops
1. Need to setup the filters for the traffic we are interested in. To do this, execute the following steps:
Navigate to Monitor--Packet Capture
Click 'Manage Filters'
Set Filter ID 1 to be the source IP and destination IP of traffic you feel is affected ( leave all other fields blank )
Set Filter ID 2 to be the exact inverse of what you did in step 3 (destination IP in source field, Source IP in destination field)
2. Setup up the captures
Create and name the file stage for a packet capture on all the stages (receive, transmit, firewall and drop)
3. Enable filters and captures
debug dataplane packet-diag set filter on
debug dataplane packet-diag set capture on
4. open 2 CLI windows
on 1 run the following command to look at the counter ( make sure it run this command once before running the traffic)
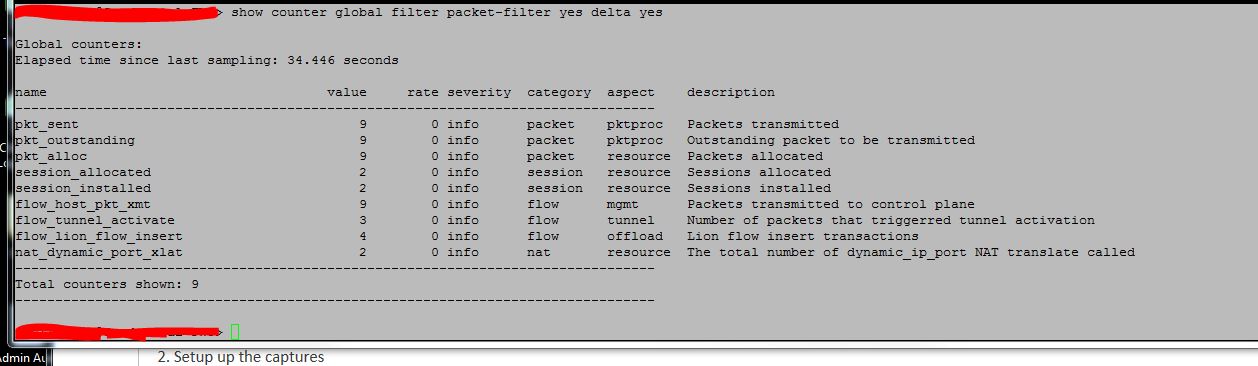
show counter global filter packet-filter yes delta yes
on the 2nd window run the following command to look at he sessions
show session all filter source <ip address> destination <ip address>
After your test has been done stop all the captures and filters and see if global counter show you anything why it is dropping the traffic or if you have getting pcap with drop stage.
This will help you narrow down the issue.
Let us know if this helps you resolve the issue.
Thanks
Numan
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-30-2013 02:03 PM
thanks fo the advice.
I cant see anything on the output thats helps so far
..and there was nothing in the session window, no session at all, so i guess the handshake never completes, i take it we can confirm the handshake never completes.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-30-2013 02:58 PM
sessions won't be built if we're dropping packets. global counters should be run consistently/repeatedly w/ hope of determining reason for dropped packets. The last screen shot unfortunately doesn't give you nor us insight.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-30-2013 03:29 PM
Hopefully those delta counters can give us a clue. Focus on dropped packets via the following:
admin@Phoenix-VM-Lab148> show counter global filter delta yes packet-filter yes severity drop
Global counters:
Elapsed time since last sampling: 3.307 seconds
name value rate severity category aspect description
--------------------------------------------------------------------------------
flow_rcv_dot1q_tag_err 627 189 drop flow parse Packets dropped: 802.1q tag not configured
flow_no_interface 627 189 drop flow parse Packets dropped: invalid interface
flow_host_service_deny 1 0 drop flow mgmt Device management session denied
--------------------------------------------------------------------------------
Total counters shown: 3
-------------------------------------------------------------------
Thanks!
- 14086 Views
- 13 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Cortex XDR Tenant Auto-Upgrade 3.17 → 5.0: UI mixed theme, AI pages stuck loading, Marketplace/Playbook Catalog empty + ingestion quota warning in Cortex XDR Discussions
- Multiple High/Critical Alert Detected via Port 18264 | Possible FP in General Topics
- Multiple High/Critical Alert Detected via Port 18264 | Possible FP in VirusTotal
- gov.in Website not accessible in Next-Generation Firewall Discussions
- Redirecting from 3rd party auth provider back to GlobalProtect Clientless VPN application in GlobalProtect Discussions




