- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Authentication seems to be the most difficult task....
- LIVEcommunity
- Discussions
- General Topics
- Authentication seems to be the most difficult task....
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-06-2017 06:10 AM
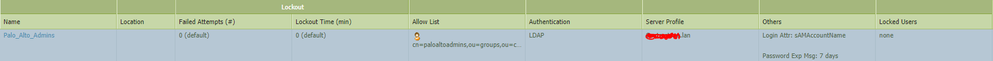
No matter how many articles I read or follow I can never get the authentication to work for LDAP. I create the LDAP server profile, create the Auth Profile, then the Auth Seq, add the user account to admins and assign the profile to that user and it never works. I also get this error when "testing":
admin@PA500-01> test authentication authentication-profile Palo_Alto_Admins username Steven.Williams.da password
Enter password :
Allow list check error:
Target vsys is not specified, user "Steven.Williams.da" is assumed to be configured with a shared auth profile.
Do allow list check before sending out authentication request...
User Steven.Williams.da is not allowed with authentication profile Palo_Alto_Admins
admin@PA500-01>
!
!
!
dmin@TN-19023-PA500-01> show user group-mapping state all
Group Mapping(vsys1, type: active-directory): Network_Administrators
Bind DN : ldap.read@domain.lan
Base : DC=domain,DC=lan
Group Filter: (None)
User Filter: (None)
Servers : configured 4 servers
10.100.6.205(636)
Last Action Time: 19 secs ago(took 0 secs)
Next Action Time: In 41 secs
10.100.6.210(636)
10.100.21.210(636)
10.110.6.210(636)
Number of Groups: 1
cn=paloaltoadmins,ou=groups,ou=domain,dc=domain,dc=lan
admin@PA500-01>
!
!
!
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-11-2017 08:30 AM
according to cli output the auth is working for ldap.
so have we solved the first part of the problem, recognising users and groups for auth profiles.
if so then the username must match exactly on local database as these are case sensitive.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-09-2017 03:21 AM
show user group name "cn=paloaltoadmins,ou=groups,ou=domain,dc=domain,dc=lan"
can you see group members?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-09-2017 09:28 AM
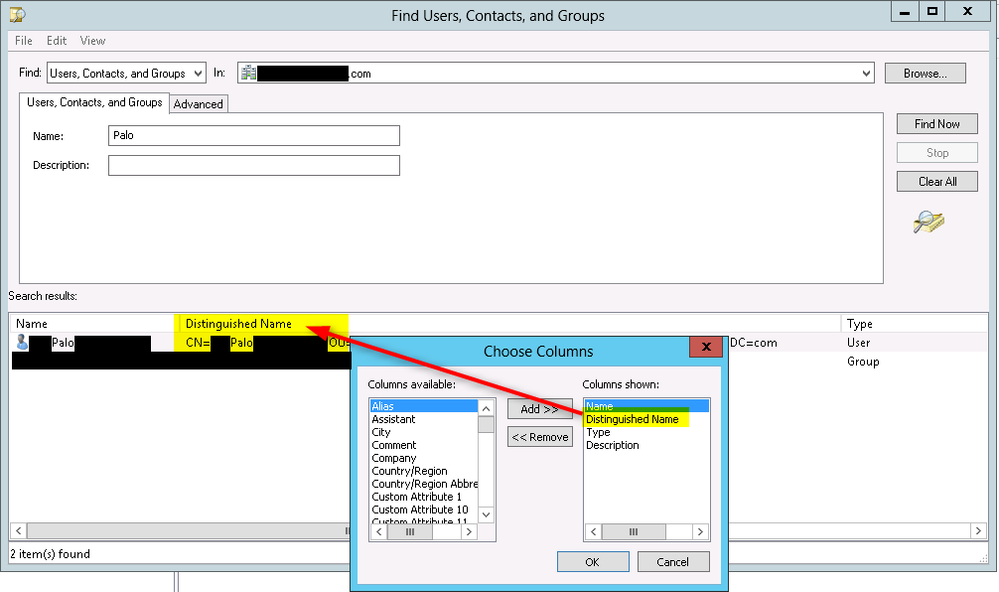
Matching the syntax of your accounts and groups is crucial for LDAP requests. You can find the proper synatax for your user or group by using the "Distinguished Name" field in "Active Directory Users and Computers".
Open up "Active Directory Users and Computers" and right click on your root domain. Choose the "Find" option from the pop-up menu. From the drop-down menu "View" select "Choose Columns" and then add the column for "Distinguished Name".
Search for your account. In this example we have a user with the word Palo in the name. The search box will show you the syntax for an LDAP query (example: CN=xxxxxx, OU=yyyyyy, DC=com). This will have your specific information required for the Palo Alto.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-09-2017 09:51 AM
That command returns nothing. So I assume it cant see it?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-09-2017 10:01 AM
if the PA cannot see it then it will not allow you to even try to auth, could be a number of things but for basics I would try:-
show user group list
this is just to make sure you have the correct group name in the first place.
then try to remove admins from the auth profile, open it up to "any" and redo the "test authentication authentication-profile" again.
also... to avoid vsys error.... set system setting target-vsys vsys1
Mick.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-09-2017 10:12 AM
sorry the show user group list may not help... as groups available was in your first post.
it may be that the bind account does not have enough permissions to see the users in the group, just the group lists.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-09-2017 10:22 AM
The show user group list only shows the user/groups in the Group Mapping Settings which from what I am reading this is not needed when doing WEB GUI auth.
Also that command you mention doesnt exist:
PA500-01> set system setting
> ctd ctd
> logging logging
> mp-memory-monitor Set monitoring of management memory
> packet packet
> packet-descriptor-monitor Set monitoring of packet descriptors
> pow pow
> shared-policy Shared policy management via Panorama
> ssl-decrypt ssl-decrypt
> template Template management via Panorama
> url-database URL database
> url-filtering-feature change URL filtering feature settings
> util util
> wildfire wildfire settings
> zip zip
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-09-2017 10:25 AM
sorry... busy day...
also ensure bind account in ldap profile is at least a member of server operators group in AD.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-09-2017 11:25 AM
Well if I set the authentication profile to "all users" it works just fine.
Enter password :
Target vsys is not specified, user "steven.williams.da" is assumed to be configured with a shared auth profile.
Do allow list check before sending out authentication request...
name "domain.lan\steven.williams.da" is in group "all"
Authentication to LDAP server at 10.100.21.210 for user "steven.williams.da"
Egress: 10.100.20.20
Type of authentication: GSSAPI
Starting LDAPS connection...
Succeeded to create a session with LDAP server
DN sent to LDAP server: CN=Steven Williams.da,OU=Users,OU=NoPoliciesApplied,OU=Users,OU=domain,DC=domain,DC=lan
User expires in days: never
Authentication succeeded for user "steven.williams.da"
admin@PA500-01>
So the Bind account is working, its just not working for a specific user group.
admin@PA500-01> show user group name cn=paloaltoadmins,ou=groups,ou=domain,dc=domain,dc=lan
short name: domain\paloaltoadmins
source type: ldap
source: Domain_Users_and_Groups
[1 ] domain\steven.williams.da
admin@PA500-01>
sees the user but can never auth with it. And yes I have created a user account in the local admins to match this.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-09-2017 11:41 AM
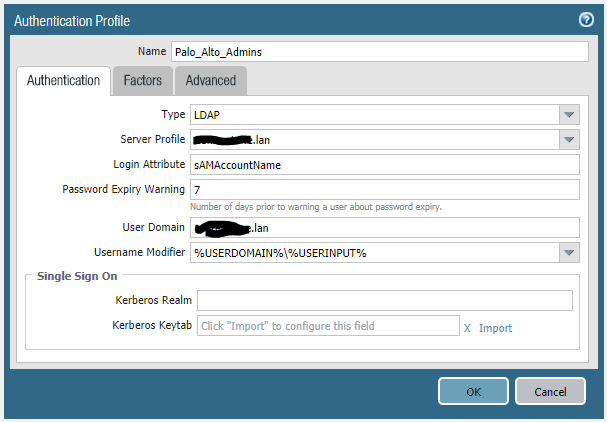
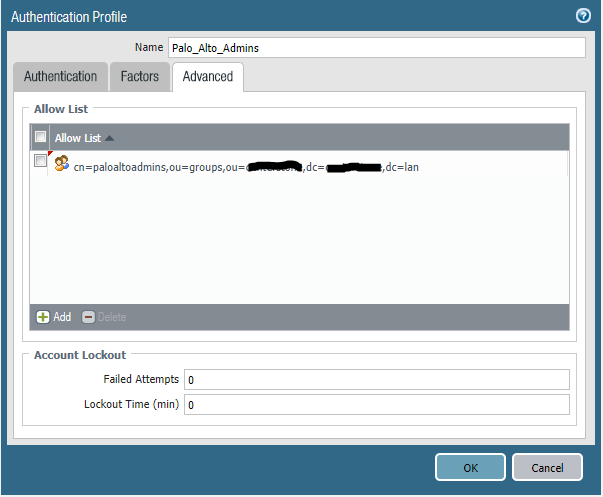
Could you post auth profile and advaced.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-09-2017 12:01 PM
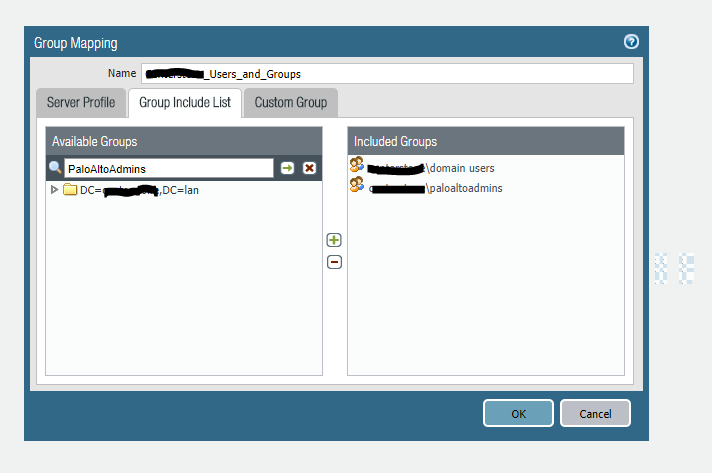
Looks fine, not sure why you are not using group mapping in user-id.
the pa will not do a dynamic lookup for group membership. It checks every 20 mins or so via group mapping and caches/updates locally.
this maybe why you cannot see yourself in show user group name.
try user-id group mapping, scroll to your group and add it to the list.
"debug user-id refresh group-mapping all". Will auto update or wait 20 mins.
then try show user group name again to see if you are seen in your group.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-09-2017 12:06 PM
Ok so what do you get if you do a show user group name for the domain admins group.
post if poss. Doesn't help but just curious.
- 1 accepted solution
- 22148 Views
- 51 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- CVE-2026-0261 PAN-OS_ Authenticated Admin Command Injection Vulnerability in Next-Generation Firewall Discussions
- Does Prisma Browser support device-based Conditional Access (device ID / compliance)? in Prisma Access Discussions
- GlobalProtect 6.3.3 + Duo SAML MFA loop after normal Windows login (works only via GP Credential Provider at Windows logon) in GlobalProtect Discussions
- GlobalProtect MFA with external/USB user certificate in GlobalProtect Discussions
- GlobalProtect Client Quadlet in GlobalProtect Discussions