- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Behaviour identifying SSL after dynamic updates installation
- LIVEcommunity
- Discussions
- General Topics
- Behaviour identifying SSL after dynamic updates installation
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Behaviour identifying SSL after dynamic updates installation
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-13-2017 01:53 AM
Hi,
Last night the scheduled dynamic installation was done, the new version 734-4212 (apps) was installed. When this installation happened a lot of traffic before detected like ssl in previous version, it was being detected like "not-applicable" and jumping all rule until default deny. We did a revert updated packet to solve it.
Why PA suddenly stop identifying ssl app with this new update package??? what should we do in order to prevent this fail identifying apps in new apps package??
How should we procced_ Do we re-apply the current version? we should wait for a new one (junmping 734-4241 which is not identifying properly SSL?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-13-2017 02:38 AM
I haven't heard of any issues yet.
The application column shows not-applicable if the traffic matches an allowing/blocking security rule via a service filter rather than an application filter :
To prevent any unwanted things from happening you could configure a threshold in your update schedule.
If you decide to configure this threshold then please consider this DOC :
Cheers,
-Kiwi
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-13-2017 03:01 AM
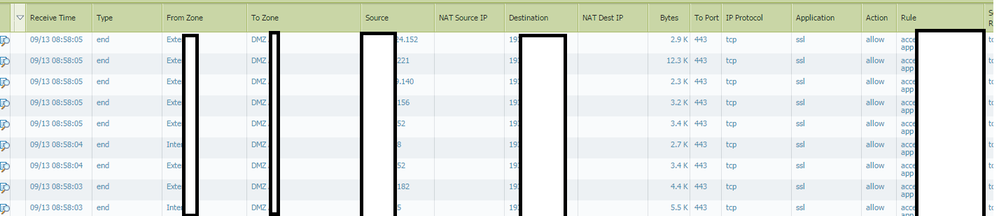
An example:
Before apps package was identifying properly the apps SSL. Traffic SSL and rule defined.
After installing last package (last night), we detect problem idetifying SSL
Why its not identifying SSL with the new apps package??
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-13-2017 05:47 AM
While I can't speak to this being a widespread issue as I don't have the current update installed on even my test enviroment at the moment, I would highly recommmend you put some type of delay on your production equipment so that the update needs to be x number of hours old before it gets applied. This usually gives those of us with test envioroments or those that don't have a delay set to notice any potential issues so PA has a chance to pull the update if it trully causes any issues.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-13-2017 07:29 AM
I cant find the cause why PA is not detecting this SSL traffic. I think it could be a widespead issue. If anyone has any PA confirmation just let me know.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-13-2017 07:41 AM
Have you reached out to TAC about this ?
If this was a widespread issue, I would have expected more similar reactions (as with content 729 about 2 weeks ago).
Cheers,
-Kiwi.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- 3101 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Python Script isn't being executed completely in Cortex XDR in Cortex XDR Discussions
- XQl query to identify software installation attempt and/or launching a software in MacOS in Cortex XDR Discussions
- Firewallupdates via Panorama - huge delay in download and install in General Topics
- Identifying Endpoints with WSL Installed from Host Insights in Cortex XDR Discussions
- Cortex XDR version 8 Autoupgrade behaviour on Server 2008 R2 in Cortex XDR Discussions