- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Blocking macro-enabled Office files (docm, xlsm, etc)
- LIVEcommunity
- Discussions
- General Topics
- Blocking macro-enabled Office files (docm, xlsm, etc)
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-11-2016 04:57 PM
The available file types that can be filtered doesn't include Office documents with macros (docm, xlsm, etc). These are being used now to sneak garbage into the network. Is there a way to ID them or are they on the horizon for inclusion in the file blocking filters? An innovative way that is being used is to create an xlsm file with a malicious macro in it and then replace the xlsm extension with csv. User thinks it's just rows of text and clicks on it, Windows feeds it to Excel, and Excel opens it and runs the macro.
Gene
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-12-2016 10:15 AM
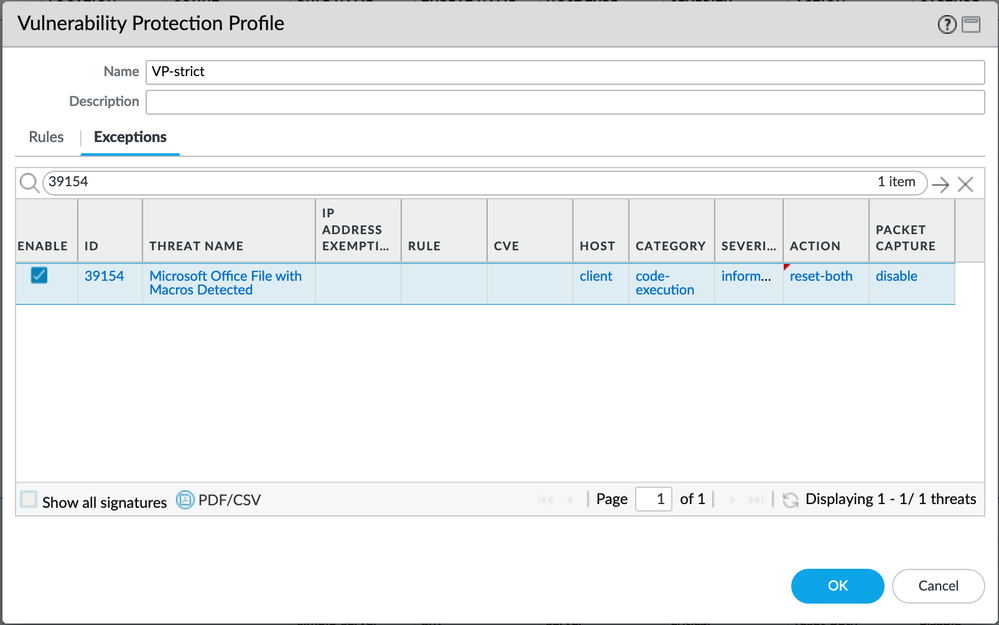
You can also block id 39154 which is Microsoft Office File with Macros. Please note that this isn't a perfect signature by far, but it does manage to take care of a good percentage of files before they hit our Barracudas
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-12-2016 07:17 AM - edited 07-07-2022 12:23 AM
Hi Gene
In fileblocking the firewall is not able to differentiate doc files with or without macros as they are basically the same file type, it will be able to identify doc files 'disguised' as CSV as it looks deeper into the file than merely the extention . You could block doc files altogether, which may be a bit over the top.
Vulnerability protection has an ID for Office files containing Macros as BPry mentions
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-12-2016 07:40 AM
Block macros with GPO.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-12-2016 10:15 AM
You can also block id 39154 which is Microsoft Office File with Macros. Please note that this isn't a perfect signature by far, but it does manage to take care of a good percentage of files before they hit our Barracudas
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-16-2016 01:54 PM
Or Subscribe to Wildfire, it does a pretty bang up job with handling them!
Good luck!
-sO
- 1 accepted solution
- 12572 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Es posible bloquear una IP en cortex xdr pro in Cortex XDR Discussions
- Issue with IOC not blocking MyPDFSwitch executable in Cortex XDR Discussions
- E token Cortex XDR blocking in Cortex XDR Discussions
- Translate Pop-up Feature Block in Next-Generation Firewall Discussions
- Avaya ports Blocking in General Topics