- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Centralized User ID Agent to All firewalls with AD integration
- LIVEcommunity
- Discussions
- General Topics
- Re: LDAP configuration Using User ID Agent
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Centralized User ID Agent to All firewalls with AD integration
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-17-2017 07:37 AM - edited 07-18-2017 12:36 AM
Dear Community,
Kindly note that we would like to achieve AD integration through centralized user id agent ,in that all of the firewalls will have userid agent which is integrated with AD.
So basically userid agent work as a proxy, How this can be achived. I had gone through this link,
Regarding LDAP configuration part , nothing is mentioned .Appreciate if any body help
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-18-2017 12:10 AM
hi @ymamis
The article you provided shows you how to enable LDAP proxy, what this does is this:
Under normal circumstances if you configure an LDAP server profile and an authentication profile calls for this LDAP server to authenticate someone (captive portal, VPN, admin ,...) the firewall will send out an LDAP connection from the management port (the tcp session will physically source from the management interface)
If you want to change that source for security reasons (eg. you want unencrypted ldap but you don't want a sniffer to be able to pick up your authentication sessions) you can enable ldap proxy on one of your UserID agents.
This setting will 'proxy' your ldap session over the secure user-id connection: the firewall has a permanent encrypted connection with the user-id agent, and an ldap session can be tunneled through that session. this will make the 'physical' source of the ldap, be the socket on the server where the user-id agent is installed (instead of the management interface)
your LDAP configuration does not change
enabling the proxy setting simply tells the firewall to send the tcp session over the user-id link instead of out the management interface
you may want to look into service routes also : Setting a Service Route for Services to Use a Dataplane Interface from the Web UI and CLI
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-18-2017 12:34 AM
Reaper,
Thanks for your clarification , could you please comment on our requirement . We want to integrate firewall to AD through userid agent, not directly , sounds like a centralized user id agent to all of the firewalls. Will this can be achievable ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-18-2017 01:44 AM
can you elaborate on your requirement?
Which aspect do you want to integrate exactly?
have you checked this article: Getting Started: User-ID it outlines everything about User-ID
the User-ID agent itself can only perform 3 functions:
-provide user-to-ip mapping to the firewall by means of reading security logs, server sessions, netbios/WMI probing or API/syslog
-provide NTLM authentication through the AD it is installed on
-proxy LDAP authentication sessions
multiple firewalls can connect to the same user-ID agent
multiple user-ID agents can serve a firewall
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-18-2017 04:08 AM
Hello Reaper,
Thank you for your comments, and our requirement is this one .
User----Captive portal--> Palo Alto Firewall -->User ID agent --> AD
We are using windows based user id agent and its integrated to AD. And there is no other integration from PA firewall to AD through palo-alto agents. Our target is to achieve browser challenge with NTLM authentication using User ID agent from PA firewall.
Specifically the concerns are
- Is this suffice to integrate firewall with user id agent only and through this can we achieve NTLM authentication. That means there is no AD integration in firewall and only user id agent can being communicate to AD.
- Do you have any document related to this ?
· The issue is that we have multiple firewalls and we don’t want every firewall to integrate with AD, rather than a centralized user id agent sounds good
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-18-2017 12:12 PM
have you read this article: Getting Started: User-ID ?
it covers all aspects of user-ID including NTLM.
you will need to configure an ldap profile and enable LDAP proxy on the user-id agent, and also enable NTLM on the user-id agent. as soon as those 2 boxes are checked only the agent will communicate with the AD
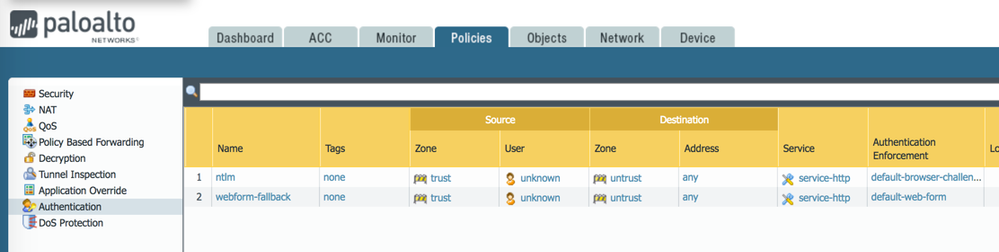
to tie everything together you'll need to enable Captive Portal with ntlm policies
PANgurus - Strata & Prisma Access specialist
- 5204 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Cortex XDR Pro – Does it scan USB devices upon insertion? in Cortex XDR Discussions
- MacOS uninstall password reset in Cortex XDR Discussions
- GlobalProtect MFA with external/USB user certificate in GlobalProtect Discussions
- GP with saml authentication always redirects to idp in General Topics
- Updating Cortex Agent by MDM in Cortex XDR Discussions