- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Changing the GlobalProtect Portal & Gateway ports
- LIVEcommunity
- Discussions
- General Topics
- Changing the GlobalProtect Portal & Gateway ports
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-28-2012 08:09 PM
Can the GlobalProtect Portal & Gateway ports (443) be changed from 443 to a user defined port number?
Thx
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-25-2013 12:52 AM
Hi,
There is a workaround that you can use to access the portal on a non-standard port:
Can GlobalProtect Portal Page be Configured to be Accessed on any Port?
Rgds
Raf
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-07-2020 05:40 AM
still no solountion to this issue ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-23-2020 08:14 AM
Create your GP portal on a loopback IP, and then use NAT and security rules to drive traffic to that from whatever port you want. I'm using 44443 now as a test and it works perfectly.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-10-2022 09:57 PM
What if you're trying to use SAML Authentication? The Assertion URL contains :443 and when you are logged in you're redirected back to the wrong port.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-09-2022 10:25 AM
Like some have already mentioned, this is indeed possible through a loopback interface.
Here's a working link to this KB:
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClGKCA0
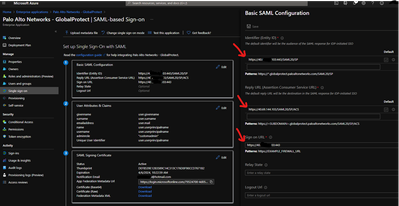
If GlobalProtect is in Azure (SAML), make sure to change the port here to your desired one:
Don't forget to hit that Like button if a post is helpful to you!
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-10-2022 06:49 PM
Hi Gustavo,
Thank you for the reply but unfortunately I'm using Duo and not Azure as my SAML IdP and the workaround described in the KB doesn't work. Setting the Login URL seems to do nothing and setting the ACS/Reply URL creates an error saying that the ACS URL doesn't match the URL in the Assertion. Even creating multiple ACS entries doesn't help, it just sends you back to the URL in the Assertion generated by the Palo.
I tried to find out from Duo if the workaround described in the KB is non-compliant SAML that just happens to work or if the functionality of the Duo system was incomplete but I couldn't get a clear answer.
Fortunately I was able to get this working as the customer could request an additional public IP address from their ISP and we were able to put GlobalProtect on 443 on the new IP address.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-17-2022 10:25 AM
I try this solution, and doesn´t work. My port is a 7000, when i try a redirect port in azure, the port is always the same 443 not 7000, only with saml
- 1 accepted solution
- 27375 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Global Protect count current users not match statistics in GlobalProtect Discussions
- GP with saml authentication always redirects to idp in General Topics
- GlobalProtect Gateway behind reverse proxy in GlobalProtect Discussions
- Intelligence Stream 504 Error, PCC v.33 in Cortex Cloud Discussions
- Rollout Strategy: GlobalProtect Disconnect Comments + 12-Hour Auto-Reconnect in GlobalProtect Discussions