- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Encrypted Traffic over the Palo Alto
- LIVEcommunity
- Discussions
- General Topics
- Re: Encrypted Traffic over the Palo Alto
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Encrypted Traffic over the Palo Alto
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-21-2014 06:22 AM
We have site to site VPN (both side PA) in our network, I want to send some encrypted traffic over the tunnel , How the palo alto will decide the encrypted traffic not to be scanned (threats) and filtering rule also not applied for the those traffic. Please suggest.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-21-2014 08:05 AM
If you are asking for, how to skip layer-7 processing (threats) for that encrypted traffic, we may need to apply an application-override policy for that. Reference DOC: How to Create an Application Override Policy
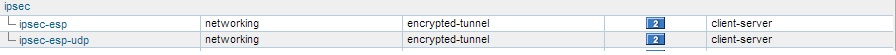
PAN has an application signature for ESP traffic:
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-21-2014 11:12 AM
If the PA firewall is just a pass through device for site-to-site VPN traffic, then we cannot subject it to threat scanning. But in your case since we are the end points for tunnel traffic, you can skip threat scanning by not configuring security profiles and attaching them to the security rules that allow inbound and outbound encrypted traffic over the tunnel. It is as simple as that. I am not sure about your question on filtering though. Can you elaborate please?
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-21-2014 12:10 PM
Hi Tiwara,
Lets say Networks has following topology.
Host---(Trust)PANW(VPN)----Tunnel----- Other End of Tunnel
1. Host send a Packet and it Hits Trust Zone of The Firewall.
2. There is a Policy Between Turst and VPN zone. If that policy has anti-virus, vulnerability, anti-spyware profile configured than Firewall will scan packet. If Policy doesnt have any profile, Firewall will not scan traffic.
3. Now After scan Packet Hits Tunnel and then sent accross the tunnel in Encrypted Format.
NOTE: Firewall do not inspect any kind of encrypted traffic like SSL/IPsec.
Lets say if Host send a packet with SSL header[means encrypted], than Firewall will not inspect it. Because firewall can not read content. [story is different is decryption is configured on firewall]
Lets say if firewall gets pass through traffic for IPsec, still it will not scan it. Because its encrypted and firewall can not read it.
Let me know if it helps.
Regards,
Hardik Shah
- 5763 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Palo Alto 3410 Firewall 100% DP CPU spike in Next-Generation Firewall Discussions
- How to add Wildcard Domains as a destination for Firewall policy PA1420 in General Topics
- Restrict access via GlobalProtect to permit access to only a specific Google Drive Account/Folder in GlobalProtect Discussions
- Cloud NGFW: Mandatory Panorama Upgrade to 11.2.7-h4 or higher for managing Cloud NGFW Firewalls. in General Topics
- Source and destination is APIPA or Soure is Legit machine and destination to Internet(zone) is APIPA in Next-Generation Firewall Discussions




